- Princeton University Doctoral Dissertations, 2011-2024
- Electrical Engineering
Items in Dataspace are protected by copyright, with all rights reserved, unless otherwise indicated.

A survey on security challenges in cloud computing: issues, threats, and solutions
- Published: 28 February 2020
- Volume 76 , pages 9493–9532, ( 2020 )
Cite this article

- Hamed Tabrizchi 1 &
- Marjan Kuchaki Rafsanjani ORCID: orcid.org/0000-0002-3220-4839 1
16k Accesses
234 Citations
3 Altmetric
Explore all metrics
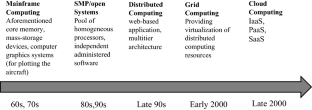
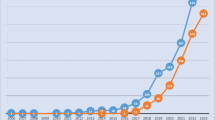
Cloud computing has gained huge attention over the past decades because of continuously increasing demands. There are several advantages to organizations moving toward cloud-based data storage solutions. These include simplified IT infrastructure and management, remote access from effectively anywhere in the world with a stable Internet connection and the cost efficiencies that cloud computing can bring. The associated security and privacy challenges in cloud require further exploration. Researchers from academia, industry, and standards organizations have provided potential solutions to these challenges in the previously published studies. The narrative review presented in this survey provides cloud security issues and requirements, identified threats, and known vulnerabilities. In fact, this work aims to analyze the different components of cloud computing as well as present security and privacy problems that these systems face. Moreover, this work presents new classification of recent security solutions that exist in this area. Additionally, this survey introduced various types of security threats which are threatening cloud computing services and also discussed open issues and propose future directions. This paper will focus and explore a detailed knowledge about the security challenges that are faced by cloud entities such as cloud service provider, the data owner, and cloud user.
This is a preview of subscription content, log in via an institution to check access.
Access this article
Price includes VAT (Russian Federation)
Instant access to the full article PDF.
Rent this article via DeepDyve
Institutional subscriptions
Similar content being viewed by others

Energy efficiency in cloud computing data centers: a survey on software technologies
Research trends in deep learning and machine learning for cloud computing security

A systematic review of homomorphic encryption and its contributions in healthcare industry
Subramanian N, Jeyaraj A (2018) Recent security challenges in cloud computing. Comput Electr Eng 71:28–42
Google Scholar
Mell P, Grance T (2018) SP 800-145, The NIST Definition of cloud computing | CSRC (online) Csrc.nist.gov. https://csrc.nist.gov/publications/detail/sp/800-145/final . Accessed 11 Dec 2018
Xu X (2012) From cloud computing to cloud manufacturing. Robot Comput Integr Manuf 28(1):75–86
Pippal SK, Kushwaha DS (2013) A simple, adaptable and efficient heterogeneous multi-tenant database architecture for ad hoc cloud. J Cloud Comput Adv Syst Appl 2(1):5
Shi B, Cui L, Li B, Liu X, Hao Z, Shen H (2018) Shadow monitor: an effective in-VM monitoring framework with hardware-enforced isolation. In: International Symposium on Research in Attacks, Intrusions, and Defenses. Springer, Berlin, pp 670–690
Bhamare D, Samaka M, Erbad A, Jain R, Gupta L, Chan HA (2017) Optimal virtual network function placement in multi-cloud service function chaining architecture. Comput Commun 102:1–16
Alzahrani A, Alalwan N, Sarrab M (2014) Mobile cloud computing. In: Proceedings of the 7th Euro American Conference on Telematics and Information Systems (EATIS’14)
Deka GC, Das PK (2018) Application of virtualization technology in IaaS cloud deployment model. In: Design and Use of Virtualization Technology in Cloud Computing: IGI Global, pp 29–99
Oracle.com (2018) The Oracle and KPMG Cloud Threat Report 2018 | Oracle (online). https://www.oracle.com/cloud/cloud-threat-report.html . Accessed 11 Dec 2018
Hashem IAT, Yaqoob I, Anuar NB, Mokhtar S, Gani A, Khan SU (2015) The rise of “big data” on cloud computing: review and open research issues. Inf Syst 47:98–115
Roman R, Lopez J, Mambo M (2018) Mobile edge computing, fog et al.: a survey and analysis of security threats and challenges. Future Gener Comput Syst 78:680–698
Ramachandra G, Iftikhar M, Khan FA (2017) A comprehensive survey on security in cloud computing. Proc Comput Sci 110:465–472
Csrc.nist.gov (2018) SP 500-299 (DRAFT), NIST Cloud Computing Security Reference Architecture | CSRC (online). https://csrc.nist.gov/publications/detail/sp/500-299/draft . Accessed 11 Sept 2018
Yu S, Wang C, Ren K, Lou W (Mar 2010) Achieving secure, scalable, and fine-grained data access control in cloud computing. In: Proceedings of the IEEE INFOCOM
Sgandurra D, Lupu E (2016) Evolution of attacks, threat models, and solutions for virtualized systems. ACM Comput Surv 48(3):1–38
Kaur M, Singh H (2015) A review of cloud computing security issues. Int J Adv Eng Technol 8(3):397–403
Kumar PR, Raj PH, Jelciana P (2018) Exploring data security issues and solutions in cloud computing. Proc Comput Sci 125:691–697
Khalil I, Khreishah A, Azeem M (2014) Cloud computing security: a survey. Computers 3(1):1–35
Bashir SF, Haider S (Dec 2011) Security threats in cloud computing. In: Proceedings of the International Conference for Internet Technology and Secured Transactions, pp 214–219
Ryan MD (2013) Cloud computing security: the scientific challenge, and a survey of solutions. J Syst Softw 86(9):2263–2268
Wang C, Wang Q, Ren K, Lou W (Mar 2010) Privacy-preserving public auditing for data storage security in cloud computing. In: Proceedings of the IEEE INFOCOM
Singh S, Jeong Y-S, Park JH (2016) A survey on cloud computing security: issues, threats, and solutions. J Netw Comput Appl 75:200–222
Khalil IM, Khreishah A, Azeem M (2014) Cloud computing security: a survey. Computers 3(1):1–35
Ahmed M, Litchfield AT (2018) Taxonomy for identification of security issues in cloud computing environments. J Comput Inf Syst 58(1):79–88
Fotiou N, Machas A, Polyzos GC, Xylomenos G (2015) Access control as a service for the Cloud. J Internet Serv Appl 6(1):11
Sumitra B, Pethuru C, Misbahuddin M (2014) A survey of cloud authentication attacks and solution approaches. Int J Innov Res Comput Commun Eng 2(10):6245–6253
Fernandes DA, Soares LF, Gomes JV, Freire MM, Inácio PR (2014) Security issues in cloud environments: a survey. Int J Inf Secur 13(2):113–170
Subashini S, Kavitha V (2011) A survey on security issues in service delivery models of cloud computing. J Netw Comput Appl 34(1):1–11
Zhang Y, Chen X, Li J, Wong DS, Li H, You I (2017) Ensuring attribute privacy protection and fast decryption for outsourced data security in mobile cloud computing. Inf Sci 379:42–61
MATH Google Scholar
Abbas H, Maennel O, Assar S (2017) Security and privacy issues in cloud computing. Springer, Berlin
TechRepublic (2018) Building Trust in a Cloudy Sky (online). https://www.techrepublic.com/resource-library/whitepapers/building-trust-in-a-cloudy-sky/ . Accessed 11 Sept 2018
Basu S et al (2018) Cloud computing security challenges and solutions—a survey. In: Proceedings of the IEEE 8th Annual on Computing and Communication Workshop and Conference (CCWC), pp 347–356
Dzombeta S, Stantchev V, Colomo-Palacios R, Brandis K, Haufe K (2014) Governance of cloud computing services for the life sciences. IT Prof 16(4):30–37
Butun I, Erol-Kantarci M, Kantarci B, Song H (2016) Cloud-centric multi-level authentication as a service for secure public safety device networks. IEEE Commun Mag 54(4):47–53
Saevanee H, Clarke N, Furnell S, Biscione V (2015) Continuous user authentication using multi-modal biometrics. Comput Secur 53:234–246
Khalil I, Khreishah A, Azeem M (2014) Consolidated identity management system for secure mobile cloud computing. Comput Netw 65:99–110
Faber T, Schwab S, Wroclawski J (2016) Authorization and access control: ABAC. In: McGeer R, Berman M, Elliott C, Ricci R (eds) The GENI book. Springer, Berlin, pp 203–234
Khan MA (2016) A survey of security issues for cloud computing. J Netw Comput Appl 71:11–29
Cai F, Zhu N, He J, Mu P, Li W, Yu Y (2018) Survey of access control models and technologies for cloud computing. Clust Comput 22(S3):6111–6122
Joshi MP, Joshi KP, Finin T (2018) Attribute based encryption for secure access to cloud based EHR systems. In: Proceedings of the International Conference on Cloud Computing
Indu I, Anand PR, Bhaskar V (2018) Identity and access management in cloud environment: mechanisms and challenges. Eng Sci Technol Int J 21(4):574–588
Mohit P, Biswas G (2017) Confidentiality and storage of data in cloud environment. In: Proceedings of the 5th International Conference on Frontiers in Intelligent Computing: Theory and Applications. Springer, Berlin, pp 289–295
Khan SI, Hoque ASL (2016) Privacy and security problems of national health data warehouse: a convenient solution for developing countries. In: Proceedings of the IEEE International Conference on Networking Systems and Security (NSysS), pp 1–6
Tang J, Cui Y, Li Q, Ren K, Liu J, Buyya R (2016) Ensuring security and privacy preservation for cloud data services. ACM Comput Surv (CSUR) 49(1):13
Islam MA, Vrbsky SV (2017) Transaction management with tree-based consistency in cloud databases. Int J Cloud Comput 6(1):58–78
Ku C-Y, Chiu Y-S (2013) A novel infrastructure for data sanitization in cloud computing. In: Diversity, Technology, and Innovation for Operational Competitiveness: Proceedings of the 2013 International Conference on Technology Innovation and Industrial Management, pp 3–25
Singh HJ, Bawa S (2018) Scalable metadata management techniques for ultra-large distributed storage systems—a systematic review. ACM Comput Surv (CSUR) 51(4):82
Sehgal NK, Bhatt PCP (2018) Cloud computing concepts and practics. Springer
Prokhorenko V, Choo K-KR, Ashman H (2016) Web application protection techniques: a taxonomy. J Netw Comput Appl 60:95–112
Shin S et al (2014) Rosemary: a robust, secure, and high-performance network operating system. In: Proceedings of the 2014 ACM SIGSAC Conference on Computer and Communications Security. ACM, New York, pp 78–89
Somani G, Gaur MS, Sanghi D, Conti M, Buyya R (2017) DDoS attacks in cloud computing: issues, taxonomy, and future directions. Comput Commun 107:30–48
Sattar K, Salah K, Sqalli M, Rafiq R, Rizwan M (2017) A delay-based countermeasure against the discovery of default rules in firewalls. Arab J Sci Eng 42(2):833–844
Iqbal S, Kiah ML, Dhaghighi B, Hussain M, Khan S, Khan MK, Choo KKR (2016) On cloud security attacks: a taxonomy and intrusion detection and prevention as a service. J Netw Comput Appl 74:98–120
Mishra P, Pilli ES, Varadharajan V, Tupakula U (2017) Intrusion detection techniques in cloud environment: a survey. J Netw Comput Appl 77:18–47
Kohnfelder L, Garg P (1999) The threats to our products. Microsoft Interface, Microsoft Corporation, New York, p 33
Tounsi W, Rais HJC (2018) A survey on technical threat intelligence in the age of sophisticated cyber attacks. Comput Secur 72:212–233
Meinig M, Sukmana MI, Torkura KA, Meinel CJPCS (2019) Holistic strategy-based threat model for organizations. Proc Comput Sci 151:100–107
Mokhtar B, Azab MJAEJ (2015) Survey on security issues in vehicular ad hoc networks. Alex Eng J 54(4):1115–1126
Tan Y, Wu F, Wu Q, Liao XJTJOS (2019) Resource stealing: a resource multiplexing method for mix workloads in cloud system. J Supercomput 75(1):33–49
Hong JB, Nhlabatsi A, Kim DS, Hussein A, Fetais N, Khan KMJCN (2019) Systematic identification of threats in the cloud: a survey. Comput Netw 150:46–69
Haber MJ, Hibbert B (2018) Asset attack vectors. Apress, Berkeley, CA
Rai S, Sharma K, Dhakal D (2019) A survey on detection and mitigation of distributed denial-of-service attack in named data networking. In: Sarma H, Borah S, Dutta N (eds) Advances in communication, cloud, and big data. Lecture notes in networks and systems, vol 31. Springer, Singapore
Bojović P, Bašičević I, Ocovaj S, Popović M (2019) A practical approach to detection of distributed denial-of-service attacks using a hybrid detection method. Comput Electr Eng 73:84–96
Eldewahi AE, Hassan A, Elbadawi K, Barry BI (2018) The analysis of MATE attack in SDN based on STRIDE model. In: Proceedings of the International Conference on Emerging Internetworking, Data and Web Technologies, pp 901–910
Tuma K, Scandariato R (2018) Two architectural threat analysis techniques compared. In: Proceedings of the European Conference on Software Architecture. Springer, Berlin, pp 347–363
Symantec.com (2019) Cloud Security Threat Report (CSTR) 2019 | Symantec (online). https://www.symantec.com/security-center/cloud-security-threat-report . Accessed 19 July 2019
Akshaya MS, Padmavathi G (2019) Taxonomy of security attacks and risk assessment of cloud computing. In: Peter J, Alavi A, Javadi B (eds) Advances in big data and cloud computing. Advances in intelligent systems and computing, vol 750. Springer, Singapore
Subramanian N, Jeyaraj AJC, Engineering E (2018) Recent security challenges in cloud computing. Comput Electr Eng 71:28–42
Tan CB, Hijazi MHA, Lim Y, Gani A (2018) A survey on proof of retrievability for cloud data integrity and availability: cloud storage state-of-the-art, issues, solutions and future trends. J Netw Comput Appl 110:75–86
Ghafir I, Jibran S, Mohammad H, Hanan F, Vaclav P, Sardar J, Sohail J, Thar B (2018) Security threats to critical infrastructure: the human factor. J Supercomput 74(10):4986–5002
Yamin MM, Katt B, Sattar K, Ahmad MB (2019) Implementation of insider threat detection system using honeypot based sensors and threat analytics. In: Future of Information and Communication Conference. Springer, Berlin, pp 801–829
Osanaiye O, Choo K-KR, Dlodlo MJJON (2016) Distributed denial of service (DDoS) resilience in cloud: review and conceptual cloud DDoS mitigation framework. J Netw Comput Appl 67:147–165
Alsmadi I (2019) Incident response. In: The NICE Cyber Security Framework, pp 331–346
Fernandes G, Rodrigues JJPC, Carvalho LF, Al-Muhtadi JF, Proença ML (2018) A comprehensive survey on network anomaly detection. Telecommun Syst 70(3):447–489
Nashimoto S, Homma N, Hayashi Y, Takahashi J, Fuji H, Aoki T (2016) Buffer overflow attack with multiple fault injection and a proven countermeasure. J Cryptogr Eng 7(1):35–46
Chen Z, Han H (2017) Attack mitigation by data structure randomization. In: Cuppens F, Wang L, Cuppens-Boulahia N, Tawbi N, Garcia-Alfaro J (eds) Foundations and practice of security. FPS 2016. Lecture notes in computer science, vol 10128. Springer, Cham
Cohen A, Nissim N, Rokach L, Elovici Y (2016) SFEM: structural feature extraction methodology for the detection of malicious office documents using machine learning methods. Expert Syst Appl 63:324–343
Sangeetha R (Feb 2013) Detection of malicious code in user mode. In: Proceedings of the International Conference on Information Communication and Embedded Systems (ICICES)
Lichtman M, Poston JD, Amuru S, Shahriar C, Clancy TC, Buehrer RM, Reed JH (2016) A communications jamming taxonomy. IEEE Secur Priv 14(1):47–54
Wu M, Moon YB (2017) Taxonomy of cross-domain attacks on cyber manufacturing system. Proc Comput Sci 114:367–374
Bhagwani H, Negi R, Dutta AK, Handa A, Kumar N, Shukla SK (2019) Automated classification of web-application attacks for intrusion detection. In: Lecture notes in computer science, pp 123–141
Chen M-S, Park JS, Yu PS (1996) Data mining for path traversal patterns in a web environment. In: Proceedings of 16th International Conference on Distributed Computing Systems, pp 385–392
Murugan K, Suresh P (2018) Efficient anomaly intrusion detection using hybrid probabilistic techniques in wireless ad hoc network. Int J Netw Secur 20(4):730–737
Ghose N, Lazos L, Li M (2018) Secure device bootstrapping without secrets resistant to signal manipulation attacks. In: Proceedings of the IEEE Symposium on Security and Privacy (SP), pp 819–835
Osanaiye O, Choo K-KR, Dlodlo M (2016) Distributed denial of service (DDoS) resilience in cloud: review and conceptual cloud DDoS mitigation framework. J Netw Comput Appl 67:147–165
Zhang X, Zhang Y, Mo Q, Xia H, Yang Z, Yang M, Wang X, Lunand L, Duan H (2018) An empirical study of web resource manipulation in real-world mobile applications. In: Proceedings of the 27th Security Symposium (Security 18), pp 1183–1198
Coppolino L, D’Antonio S, Mazzeo G, Romano L (2017) Cloud security: emerging threats and current solutions. Comput Electr Eng 59:126–140
Gumaei A, Sammouda R, Al-Salman AMS, Alsanad A (2019) Anti-spoofing cloud-based multi-spectral biometric identification system for enterprise security and privacy-preservation. J Parallel Distrib Comput 124:27–40
Vlajic N, Chowdhury M, Litoiu M (2019) IP Spoofing in and out of the public cloud: from policy to practice. Computers 8(4):81
Download references
Author information
Authors and affiliations.
Department of Computer Science, Faculty of Mathematics and Computer, Shahid Bahonar University of Kerman, Kerman, Iran
Hamed Tabrizchi & Marjan Kuchaki Rafsanjani
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to Marjan Kuchaki Rafsanjani .
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Reprints and permissions
About this article
Tabrizchi, H., Kuchaki Rafsanjani, M. A survey on security challenges in cloud computing: issues, threats, and solutions. J Supercomput 76 , 9493–9532 (2020). https://doi.org/10.1007/s11227-020-03213-1
Download citation
Published : 28 February 2020
Issue Date : December 2020
DOI : https://doi.org/10.1007/s11227-020-03213-1
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Cloud computing
- Vulnerabilities
- Data protection
- Find a journal
- Publish with us
- Track your research
Research on Cloud Computing Security Platform
Ieee account.
- Change Username/Password
- Update Address
Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.

- < Previous
Home > Graduate College > Theses > 919
Masters Theses
Security and privacy in cloud computing.
Ramakrishnan Krishnan
Date of Award
Spring 2017

Degree Name
Master of Science
Computer Science
First Advisor
Dr. Leszek T. Lilien
Second Advisor
Dr. John Kapenga
Third Advisor
Dr. Ikhlas Abdul Qader
Cloud, cloud security, cloud privacy, intertwined security and privacy, cloud based services
Access Setting
Masters Thesis-Open Access
Cloud computing (CC) gained a widespread acceptance as a paradigm of computing. The main aim of CC is to reduce the need for customers' investment in new hardware or software by offering flexible cloud services, with a user reaping the benefits of the pay per use approach. CC demands addressing many security and privacy issues : both problems (vulnerabilities, threats, and attacks) and solutions (controls). The thesis discusses all these classes of problems and solutions, categorizing them as either security-related issues, privacy-related issues, or intertwined security and privacy issues. The main contributions of the thesis are twofold: first, using the above categorization of the issues; and second, the literature review of the security and privacy issues in CC within the categorization framework. The major lessons learned during this research include confirmation of the decisive role that security and privacy solutions play and will continue to play in adopting CC by customers; understanding numerous vulnerabilities, threats, and attacks; and identifying controls for these problems. In addition, the sheer number of references to trust (in both problems and solutions), demonstrated a significant role of trust in CC.
Recommended Citation
Krishnan, Ramakrishnan, "Security and Privacy in Cloud Computing" (2017). Masters Theses . 919. https://scholarworks.wmich.edu/masters_theses/919
Since July 06, 2017
Included in
Information Security Commons
ScholarWorks
Advanced Search
- Notify me via email or RSS
- Collections
- Disciplines
Author Corner
- Graduate College
Western Michigan University Libraries, Kalamazoo MI 49008-5353 USA | (269) 387-5611
Home | About | FAQ | My Account | Accessibility Statement
Privacy | Copyright

- Home
- University of Bedfordshire e-theses
- PhD e-theses
A novel approach to providing secure data storage using multi cloud computing

Description
Collections.
The following license files are associated with this item:
- Creative Commons
entitlement

Related items
Showing items related by title, author, creator and subject.
Multiple-clouds computing security approaches: a comparative study
A multi-cloud approach for secure data storage on smart device, personally identifiable information security in cloud computing, export search results.
The export option will allow you to export the current search results of the entered query to a file. Different formats are available for download. To export the items, click on the button corresponding with the preferred download format.
By default, clicking on the export buttons will result in a download of the allowed maximum amount of items.
To select a subset of the search results, click "Selective Export" button and make a selection of the items you want to export. The amount of items that can be exported at once is similarly restricted as the full export.
After making a selection, click one of the export format buttons. The amount of items that will be exported is indicated in the bubble next to export format.
- På svenska
- Ammattikorkeakoulut
- Turun ammattikorkeakoulu
- Opinnäytetyöt (Avoin kokoelma)
- Näytä viite
Security attacks in cloud computing
Pandey, prabin (2021).
Avaa tiedosto
Tiivistelmä, selaa kokoelmaa, henkilökunnalle.
Academia.edu no longer supports Internet Explorer.
To browse Academia.edu and the wider internet faster and more securely, please take a few seconds to upgrade your browser .
Enter the email address you signed up with and we'll email you a reset link.
- We're Hiring!
- Help Center

thesis Cloud Computing & Security final.doc

A cloud is the powerful combination of cloud computing, storage, management solution. More and more turning to data storage, management in the cloud computing & Security. It is often provided "as a service “over the Internet, typically in the form of infrastructure as a service (IaaS), platform as a service (PaaS), or software as a service (SaaS). Cloud computing is a general term for anything that involves delivering hosted services over the Internet. Amazon Elastic Compute Cloud (Amazon EC2) is a web service that provides secure, resizable compute capacity in the cloud. It is designed to make web-scale cloud computing easier for developers. In this thesis paper we analysis about AWSEC2 and GCE and compare both which is better. Amazon EC2 reduces the time required to obtain and boot new server instances to minutes, allowing you to quickly scale capacity, both up and down, as your computing requirements change. Google Compute Engine lets you create and run virtual machines on Google infrastructure. Compute Engine offers scale, performance, and value that allow you to easily launch large compute clusters on Google's infrastructure. There are no upfront investments and you can run thousands of virtual CPUs on a system that has been designed to be fast, and to offer strong consistency of performance. Arguably, Infrastructure as a Service (IaaS) is the most important cloud computing vertical. Within that, in terms of services and features, AWS enjoys the top position, while Google Cloud Platform is slowly catching up. In this post, we’ll discuss major differences between Amazon’s EC2 and Google Compute Engine (GCE). This paper we proposed a method by implementing RSA algorithm will explore data security of cloud in cloud computing by implementing digital signature and encryption with elliptic curve cryptography.
Related Papers
IJFRCSCE Journal
Journal of Computer Science IJCSIS
In today's modern IT everything is possible on the web by cloud computing, it allows us to create, configure, use and customize the applications, services, and storage online. The Cloud Computing is a kind of Internet-based computing, where shared data, information and resources are provided with computers and other devices on-demand. The Cloud Computing offers several advantages to the organizations such as scalability, low cost, and flexibility. In spite of these advantages, there is a major problem of cloud computing, which is the security of cloud storage. There are a lot of mechanisms that is used to realize the security of data in the cloud storage. Cryptography is the most used mechanism. The science of designing ciphers, block ciphers, stream ciphers and hash functions is called cryptography. Cryptographic techniques in the cloud must enable security services such as authorization, availability, confidentiality, integrity, and non-repudiation. To ensure these services of security, we propose an effective mechanism with a significant feature of the data. This paper is to show how to improve the security of the Cloud storage using the implementation of a hybrid encryption algorithm and hash functions. It proposes the implementation of two algorithms, Rivest-Shamir-Adleman (RSA) and Advanced Encryption Standard (AES) with a secure hashing algorithm (SHA256) by using Netbeans IDE 8.0.2, JDK 1.7 tool and EyeOS2.5 as a cloud platform on ubuntu14.04.
Dr Manikandasaran S S , Arockiam Lawrence
Abstract— Current security scheme in cloud computing applied single encryption algorithm. However, usage of a single algorithm is not effective for high-level security requirement towards data processing in cloud computing. Therefore, this study proposes combination of AES, ECC and RSA encryption method to strengthen the security in cloud in terms of authentication and encryption. The method for this study is the text data has been encrypted using AES then, AES key have been encrypted by ECC only after that RSA will encrypt both the ciphertext and the encoding key again. Java NetBean is used to program the evaluation tool to calculate the performance of the encryption method. First, the tool has applied the three algorithms AES, ECC and RSA using a dataset consisting of multiple text file with different sizes. Evaluation has been performed using encryption time, decryption time and secrecy measure. Results showed that the proposed method has the ability to fulfil both efficiency and security factors with highest secrecy value. The impact of combination layer of encryption algorithms provides a higher secrecy value compared to single layer encryption. Keywords- cloud computing; AES; RSA; ECC; secrecy
International Journal of Advance Research in Computer Science and Management Studies [IJARCSMS] ijarcsms.com
International Journal of Scientific Research in Science, Engineering and Technology IJSRSET
At present, cloud computing is the fastest growing technology in today's world. Cloud computing is a model that provides the services based on as-needed and when-needed basis. Cloud computing provides online information storage, infrastructure and application. Many organizations shift towards cloud computing due to its benefits of less hardware maintenance and reduced expenditure start-up cost and at the same time, cloud computing offers many hazards. Network and Internet applications are growing very fast, since the need to secure these applications are very fast. For this purpose cryptography algorithms (symmetric & Asymmetric) are proposed. The use of relevant algorithm deals with the level of data safety in cloud because data security in cloud computing is a serious issue as the data centers are located worldwide. Authentication is the most essential procedure to ensure the cloud data in a secured manner. However, strong user authentication is the main requirement for cloud computing that reduces the unauthorized user access of data on cloud. Data security is a more important issue of cloud computing. Thus, the need to ensure the safety of information. Here in this survey paper, I have presented encryption based security algorithms for cloud computing.
IJCSMC Journal
IJIRST - International Journal for Innovative Research in Science and Technology
In Cloud computing, Data sharing is the important functionality. Secure distributed data storage was developed to reduce the burden of data owner from managing numerous files, by transferring the files from data owner to proxy servers. Proxy servers can convert encrypted files for the owner to encrypted files for the receiver withoutthe necessity of knowing the content of the original files. In practice, the original files will be removed by the owner for the sake of space efficiency. Therefore, there is no guarantee that the outsourced files are not accessed by the unauthorized users and not modified by proxy servers is an important problem that has been considered. Hence, the issues on confidentiality and integrity of the outsourced data must be addressed carefully. In this paper, there are two Identity-Based Secure Distributed Data Storage (IBSDDS) schemes. The properties of IBSDDS schemes are as follows: The file owner can decide the access permission independently without the help of the private key generator; for one query, a receiver can only access one file, instead of all files of the owner. These schemes are secure against the collusion attacks, namely even if the receiver can compromise the proxy server, but cannot obtain the owner’s secret key. Though the first scheme is only secure against the chosen plaintext attacks (CPA), the second scheme is secure against the chosen cipher text attacks (CCA). To the best of our knowledge, it is the firstscheme where access permission is made by the owner for an exact file and collusion attacks can be protected.
TJPRC Publication
Cloud Computing is an emerging technology widely used in the IT sector due its wide range of characteristics. These characteristics serve a medium for the intruders to attack the cloud and its users. The security of cloud can be compromised by employing different strategies and techniques. Many systems and techniques have been proposed for solving the security issues and implementing a high level of security on both the sides. Encryption is one of the best method suggested for making the cloud more secure and increasing its areas of application. This paper contains an overall study and comparison of various cryptographic algorithms implemented for cloud security. We also study some hybrid systems designed using combination of various crypto terminologies for enhancing data security in cloud. The hybrid systems implement multiple cryptographic algorithms like RSA and Digital signature, Diffie Hellman and AES in combination with Digital signature. Some of the comparison parameters included are technique proposed, type of algorithm, algorithm, scalability.
RELATED PAPERS
Claudia Liliana Daza Saray
Apresentações Trabalhos Científicos
Eliana Cristina Nogueira Barion
Iranian Red Crescent Medical Journal
tahereh zare
Carbohydrate Polymers
Camila Pereira
Western Journal of Applied Forestry
Qing-lai Dang
JPPM (Jurnal Pengabdian dan Pemberdayaan Masyarakat)
Yulia Wahyuni
Juan Almagro
TẠP CHÍ KHOA HỌC ĐẠI HỌC MỞ THÀNH PHỐ HỒ CHÍ MINH - KỸ THUẬT VÀ CÔNG NGHỆ
MATEC Web of Conferences
P. Zalimidis
Razvan Rababoc
Studies in Business and Economics
saeed ul Hassan Shah
Massimiliano Ferrara
Research, Society and Development
Lucrécia Loureiro
Climatic Change
Göran Sundqvist
antonio Herbert sena moreira
Ignacio Götz
Mama Quilla
Constanza Ruiz-Danegger
Epidemiology and Infection
Alfred Kayira
Orhan Gülen
Mechanisms of Ageing and Development
Nimrat Chatterjee
Journal of Luminescence
Bonex Mwakikunga
Recent Advances in Wireless Communications and Networks
Jia-Chin Lin
IIUM Press eBooks
Bouhedda Ghalia
Language in India
Mahmud Al Hasan
Journal of Preventive Medicine and Hygiene
P. Castiglia
RELATED TOPICS
- We're Hiring!
- Help Center
- Find new research papers in:
- Health Sciences
- Earth Sciences
- Cognitive Science
- Mathematics
- Computer Science
- Academia ©2024

IMAGES
VIDEO
COMMENTS
THE CONCEPT OF CLOUD COMPUTING AND THE MAIN SECURITY ISSUES IN IT. This thesis focuses on studying and analyzing the Cloud Computing technology in concept and its security, which is still a developing technology with great convenience and portability for exchanging information over the Internet via different platforms.
Cloud computing has become a widely exploited research area in academia and industry. Cloud computing benefits both cloud services providers (CSPs) and consumers. The security challenges associated with cloud computing have been widely studied in the literature. This systematic literature review (SLR) is aimed to review the existing research studies on cloud computing security, threats, and ...
7.1. Challenges. Via analysis and contrast, we observe that cloud computing security protection work has achieved satisfactory research results. However, many problems remain, which prompt the consideration of a variety of security factors and continuous improvements in defense technology and security strategies. 1.
This Magister thesis aims to identify the security issues of virtualization in the cloud computing environments and also reviewing the mitigation techniques in order to improve the security of cloud systems. Systematic literature review or systematic review is performed in this study for finding ... 2.2-Security issues of cloud computing ...
and mitigate potential security threats targeting customers' VMs in cloud computing. CloudMonatt monitors the security health of VMs and attests to customers if they are getting their desired security. It takes actions to mitigate the potential threats that can compromise the security properties requested. We design cloud management and ...
cability in cloud computing. Current research in cloud data protection primarily falls into three main categories: 1) Authentication & Access Control, 2) Encryption, and 3) Intrusion Detection. This thesis examines the various mechanisms that currently exist to protect data being stored in a public cloud computing environment. It also looks at ...
Mechanism in Cloud Computing", "Cloud Computing Security Challenges" and "Cloud Computing Security Threats and Attacks with Their Mitigation Techniques. 1.3 Aim & Objectives This thesis aims to illustrate various existing cyber and network threats that can be vulnerable for any business that operates through a cloud computing server.
Security Analysis and Framework of Cloud Computing with Parity-Based Partially Distributed File System By Ali Asghary Karahroudy July, 2011 Director of Thesis or Dissertation: Dr. M.H.N. Tabrizi Major Department: Department of Computer Science Abstract - Cloud computing offers massive scalability, immediate availability, and low cost
Cloud security is dependent primarily on SaaS layers and web applications because they mainly offer cloud services. Therefore, the availability and security of the overall cloud services are dependent on the overall safety of the APIs, software applications, and web browsers [17]. Table 8. Common security attacks.
In this research the SLR is undertaken to discover published papers related to the security challenges and mitigation techniques in Cloud Computing associated with security attacks. To achieve the research objectives we selected the papers published between 2001 and 2010.
This dissertation proposes a new architectural framework, CloudMonatt, to detect and mitigate potential security threats targeting customers' VMs in cloud computing. CloudMonatt monitors the security health of VMs and attests to customers if they are getting their desired security. It takes actions to mitigate the potential threats that can ...
This document represents the Master Thesis of the Master in Computing, at Barcelona School of ... Cloud computing is a computing paradigm in which organizations can store their data remotely in the cloud (Internet) and access applications, services and infrastructure on-demand from a shared ... Therefore, security mechanisms to protect this ...
Data Security and the Cloud. The initial stage sought to provide a clear de nition for Cloud Computing and the security issues therein, looking to identify precisely where and when threats can occur to data and how these threats ought to be mitigated. Predicate Based Encryption. The next stage focused solely upon PBE schemes discussing
the security architecture, which can be operated across two or more clouds with different security approaches. This thesis researched security approaches to architecting hybrid cloud security, by evaluating security implementations and coming up with recommendations on se-curity posturing.
N. Amara, Huang Zhiqui, Awais Ali [1] conducted a survey of Cloud Computing Security Threats and Attacks with their Mitigation Techniques. This paper discussed the architectural principles of ...
1.5 Thesis Organization Chapter 1: Introduction; contains introduction about cloud computing and problems need to be addresses. The chapter also discusses the objective and structure of the thesis. Chapter 2: Cloud Computing and Security; Contains detail discussion about cloud computing, cloud security, and security policy.
Western Michigan University
The security issues related to cloud communication, network, data privacy, application, and web services are some traditional issues that are present at the beginning of cloud computing. Security issues that emerge due to multi-tenancy, virtualization, and shared pool resources are innovative security issues.
Objectives: This thesis aims to identify security challenges for adapt- ... For this the objective is to identify exist-ing cloud computing security challenges and their solutions. Identify the challenges that have no mitigation strategies and gather solution-s/guidelines/practices from practitioners, for a challenge with more ...
As a kind of new technology, cloud computing has become a study highlight in both industrial field and academic field. As the users have to save their data in the cloud to use cloud computing, the security of cloud could affect users' trust in cloud computing service directly. The thesis discusses the architecture and tier of cloud computing, analyzes the basic system structure of cloud ...
Cloud computing (CC) gained a widespread acceptance as a paradigm of computing. The main aim of CC is to reduce the need for customers' investment in new hardware or software by offering flexible cloud services, with a user reaping the benefits of the pay per use approach. CC demands addressing many security and privacy issues: both problems (vulnerabilities, threats, and attacks) and ...
Cloud computing paradigms are gaining widespread acceptance due to the various benefits they offer. These include cost-effectiveness, time savings and efficient
This study aims to improve the security of the delivered cloud storage service via multiple-cloud computing and to develop an approach for providing a secure data storage system that could be installed, configured, and easily consumed through the appropriate multiple-cloud model. The developed approached is supposed to maintain the ...
Cloud computing (CC) is likely to prove commercial sustainability for many firms due to its flexibility and pay-as-you-go cost structure, particularly in the current situation of economic difficulties. This master thesis analyses the nature of CC and depicts how this technology
This thesis discusses the major types of cybersecurity attacks. In particular, it discusses the essential process, needs, and a secure protocol that can be easily understood by beginners or those who are interested in using cloud computing as their daily services to counter potential network threats. The thesis deliberates the concept of ...
The Cloud Computing is a kind of Internet-based computing, where shared data, information and resources are provided with computers and other devices on-demand. The Cloud Computing offers several advantages to the organizations such as scalability, low cost, and flexibility. In spite of these advantages, there is a major problem of cloud ...
Yael Tauman Kalai's breakthroughs secure the digital world, from cloud computing to our quantum future. Yael Tauman Kalai, a cryptographer at Microsoft's New England Research and Development Center, focuses on ways to safeguard computations. Yael Tauman Kalai is a pioneering theoretical computer scientist who's won impressive awards and ...
Investment Thesis. CrowdStrike Holdings (NASDAQ:CRWD) is a cybersecurity company that offers endpoint security, ... the cloud computing market is expected to grow at a 15% CAGR from 2023 to 2028 ...