Topics in Computer and Network Security
Stanford cs 356, fall 2023.
CS 356 is graduate course that covers foundational work and current topics in computer and network security. The course consists of reading and discussing published research papers, presenting recent security work, and completing an original research project.

Course Information
Discussion: Mon/Wed 3:00–4:20 PM. Gates B12 . This course is largely based on in-person discussion rather than lecture. Attendance and participation is expected.
Instructor: Zakir Durumeric Office Hours: M/W 4:30–5:00 PM, or by appointment.
Course Assistant: Kimberly Ruth . Office hours by appointment.
Prerequisites: CS 356 is open to all graduate students as well as advanced undergraduate students. While the course has no official prerequisites, it requires a mature understanding of software systems and networks. Students are expected to have taken CS 155: Computer and Network Security or equivalent.
Topics and Readings
The tentative schedule and required readings for the class are below:
9/27 Introduction
Against security nihilism.
Blog Post. 2016. Chris Palmer.
Mining Your Ps and Qs: Detection of Widespread Weak Keys...
SEC '12 . N. Heninger, Z. Durumeric, E. Wustrow, J.A. Halderman.
How to Read a Paper
10/2 web privacy and security, the web never forgets: persistent tracking mechanisms in the....
CCS '14 . Gunes Acar, Christian Eubank, Steven Englehardt, Marc Juarez, Arvind Narayanan, Claudia Diaz.
Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice
CCS '15 . D. Adrian, K. Bhargavan, Z. Durumeric, P. Gaudry, M. Green, J.A. Halderman, N. Heninger, A. Springall, E. Thomé, L. Valenta, B. VanderSloot, E. Wustrow, S. Zanella-Beguelin, P. Zimmermann.
10/4 Usability
Alice in warningland: a large-scale field study of browser security.
SEC '13 . Devdatta Akhawe, Adrienne Porter Felt.
...no one can hack my mind”: Comparing Expert and Non-Expert Security Practices
SOUPS '15 . Iulia Ion, Rob Reeder, Sunny Consolvo.
10/9 Authentication and Phishing
The tangled web of password reuse.
NDSS '14 . Anupam Das, Joseph Bonneau, Matthew Caesar, Nikita Borisov, XiaoFeng Wang.
Detecting credential spearphishing in enterprise settings
SEC '17 . Grant Ho, Aashish Sharma, Mobin Javed, Vern Paxson, David Wagner.
10/11 Denial of Service
Inferring internet denial-of-service activity.
SEC '01 . David Moore, Geoffrey Voelker, Stefan Savage.
Understanding the Mirai Botnet
10/16 spam and ecrime, framing dependencies introduced by underground commoditization.
WEIS '15 . Kurt Thomas, Danny Huang, David Wang, Elie Bursztein, Chris Grier, Thomas Holt, Christopher Kruegel, Damon McCoy, Stefan Savage, Giovanni Vigna.
Spamalytics: An Empirical Analysis of Spam Marketing Conversion
CCS '08 . Chris Kanich, Christian Kreibich, Kirill Levchenko, Brandon Enright, Geoffrey Voelker, Vern Paxson, and Stefan Savage.
10/18 Software Attacks
Hacking blind s&p '14 . andrea bittau, adam belay, ali mashtizadeh, david mazieres, dan boneh. sok: eternal war in memory.
S&P '13 . Laszlo Szekeres, Mathias Payer, Tao Wei, Dawn Song.
10/23 Software Defenses
Native client: a sandbox for portable, untrusted x86 native code.
S&P '09 . Bennet Yee, David Sehr, Gregory Dardyk, J. Bradley Chen, Robert Muth, Tavis Ormandy, Shiki Okasaka, Neha Narula, Nicholas Fullagar.
Multiprogramming a 64 kB Computer Safely and Efficiently
SOSP '17 . Amit Levy, Bradford Campbell, Branden Ghena, Daniel B. Giffin, Pat Pannuto, Prabal Dutta, Philip Levis.
10/25 Malware and Supply Chain
Towards measuring supply chain attacks on package managers for interpreted languages.
NDSS '21 . Ruian Duan, Omar Alrawi, Ranjita Pai Kasturi, Ryan Elder, Brendan Saltaformaggio, Wenke Lee.
Before We Knew It: An Empirical Study of Zero-Day Attacks In The Real World
CCS '12 Leyla Bilge and Tudor Dumitraş.
10/30 Side Channels and Information Leakage
Timing analysis of keystrokes and timing attacks on ssh.
SEC '01 . Dawn Song, David Wagner, Xuqing Tia.
Spectre Attacks: Exploiting Speculative Execution
S&P '19 . P. Kocher, J. Horn, A. Fogh, D. Genkin, D. Gruss, W. Haas, M. Hamburg, M. Lipp, S. Mangard, T. Prescher, M. Schwarz, Y. Yarom.
11/1 Hardware
Stealthy dopant-level hardware trojans.
CHES '13 . Georg Becker, Francesco Regazzoni, Christof Paar, Wayne Burleson.
Comprehensive Experimental Analyses of Automotive Attack Surfaces
SEC '11 . Stephen Checkoway, Damon McCoy, Brian Kantor, Danny Anderson, Hovav Shacham, Stefan Savage.
W32.Stuxnet Dossier
Symantec Technical Report . Nicolas Falliere, Liam Murchu, Eric Chien.
11/8 Machine Learning
Towards evaluating the robustness of neural networks.
S&P '16 . Nicholas Carlini and David Wagner.
Outside the Closed World: On Using Machine Learning For Network Intrusion Detection
S&P '10 . Robin Sommer and Vern Paxson.
11/13 Vulnerable Populations / Security For Everyone
A stalker’s paradise: how intimate partner abusers exploit technology.
CHI '18 Diana Freed, Jackeline Palmer, Diana Minchala, Karen Levy, Thomas Ristenpart, Nicola Dell.
A11y Attacks: Exploiting Accessibility in Operating Systems
CCS '14 Yeongjin Jang, Chengyu Song, Simon Chung, Tielei Wang, Wenke Lee.
11/15 Privacy and Dark Patterns
Robust de-anonymization of large sparse datasets.
S&P '08 . Arvind Narayanan and Vitaly Shmatikov.
Dark patterns at scale: Findings from a crawl of 11K shopping websites
S&P '08 . Arunesh Mathur, Gunes Acar, Michael Friedman, Eli Lucherini, Jonathon Mayer, Marshini Chetty, Arvind Narayanan.
11/20 Thanksgiving Break
11/22 thanksgiving break, 11/27 surveillance and anonymity, keys under doormats.
MIT Technical Report '15. H. Abelson, R. Anderson, S. Bellovin, J. Benaloh, M. Blaze, W. Diffie, J. Gilmore, M. Green, S. Landau, P. Neumann, R. Rivest, J. Schiller, B. Schneier, M. Specter, D. Weitzner.
Tor: The Second-Generation Onion Router
SEC '04 . Roger Dingledine, Nick Mathewson, Paul Syverson.
11/29 Government Attacks and Disinformation
When governments hack opponents: a look at actors and technology.
SEC '14 . Bill Marczak, John Scott-Railton, Morgan Marquis-Boire, Vern Paxson.
Disinformation as Collaborative Work: Surfacing the Participatory Nature of Strategic Information Operations
CSCW '19 . Kate Starbird, Ahmer Arif, Tom Wilson.
12/4 Ethics and Problem Selection
The moral character of cryptographic work.
Phillip Rogaway.
Science, Security, and the Elusive Goal of Security as a Scientific Pursuit
S&P '17 . Cormac Herley and P.C. van Oorschot.
12/6 Final Presentations
No required reading. attendance mandatory., course structure.
This course is composed of three parts: reading and discussing foundational papers in every class, reading and presenting recent work for one class, and completing a group research project. Grading will be based on:
Readings and Discussion (30%)
We will read and discuss 1–2 papers for each class. Typically, these are formative works in an area of security. Students should come prepared to actively discuss assigned papers and to make substantive intellectual contributions. This means that you need to thoroughly read each paper ahead of time. Before each section, students will submit a short (400 word) summary and reaction for each each paper, as well as a proposal of one discussion question for class.
Students should submit the reading assignments through Gradescope by 2:30 pm on the day of each class . Paper responses should be completed individually without the assistance of LLMs (e.g., ChatGPT).
Grading will be based 20% on these written responses and 10% on in-class participation. We do not allow any late days for paper reactions, but students may skip two paper summaries and two lectures without penalty. We will take class attendance. However, participation grades are based on not only attendence, but active participation during class discussion.
Do not underestimate the amount of time required to properly read and process a research paper. Expect to spend several hours preparing for each section.
Topic Presentation (15%)
While reading formative papers helps to demonstrate how a subfield started, it oftentimes leaves us wondering how the area has evolved. To fill this gap, each student in the class will present one recent paper during the quarter topically relevant to that day's class. At the start of the quarter, students will have the opportunity to sign up for the topic/date that they want to present their paper. Stuents will have 12-15 minutes to present their paper.
Students are expected to do a literature search and to select a paper that was published in the last three years from a top-tier venue in security (e.g., IEEE Security and Privacy, USENIX Security, ACM Computer or Communication Security) or adjacent field (e.g., CHI, NSDI, ASPLOS, PLDI, etc.). Students should submit their papers to approval to the teaching staff a week prior to their presentation.
Course Project (55%)
Students will complete a quarter-long original research project in small groups (1–3 students) on a topic of their own choosing. Groups will present their work during the last two sections as well as submit a 6–10 page report, similar to the papers we read in the course.
- Project Proposal (5%). Project groups will meet with course staff to discuss their project during the third week of class and submit a one page project proposal. Written proposals are due on 10/16.
- Mid-Quarter Progress Report (5%). Submit a short (1–2 pages) progress report part way through the quarter. The report should indicate what has been accomplished, what work is remaining, obstacles the team has encountered, and any preliminary data or insights. Due 11/17.
- Class Presentation (10%). Each group will give a 10 minute class presentation during the last week of the course.
- Final Paper (35%). Groups will submit a final project report similar to the papers we read in the course. Papers should be 6–10 pages and use the USENIX LaTeX template . It may be helpful to read Writing Technical Articles if you haven't previously published any work in computer science. Due 12/8.
Students should submit all reports through Gradescope by 11:59PM on the day of each deadline.
In past offerings, well-executed projects have led to publications at top-tier security conferences and workshops. I'm happy to work with groups to publish their work.
This class has no final exam. Attendance on 12/6 is required.
Research Topics & Ideas: Cybersecurity
50 Topic Ideas To Kickstart Your Research

If you’re just starting out exploring cybersecurity-related topics for your dissertation, thesis or research project, you’ve come to the right place. In this post, we’ll help kickstart your research by providing a hearty list of cybersecurity-related research topics and ideas , including examples from recent studies.
PS – This is just the start…
We know it’s exciting to run through a list of research topics, but please keep in mind that this list is just a starting point . These topic ideas provided here are intentionally broad and generic , so keep in mind that you will need to develop them further. Nevertheless, they should inspire some ideas for your project.
To develop a suitable research topic, you’ll need to identify a clear and convincing research gap , and a viable plan to fill that gap. If this sounds foreign to you, check out our free research topic webinar that explores how to find and refine a high-quality research topic, from scratch. Alternatively, consider our 1-on-1 coaching service .
Cybersecurity-Related Research Topics
- Developing machine learning algorithms for early detection of cybersecurity threats.
- The use of artificial intelligence in optimizing network traffic for telecommunication companies.
- Investigating the impact of quantum computing on existing encryption methods.
- The application of blockchain technology in securing Internet of Things (IoT) devices.
- Developing efficient data mining techniques for large-scale social media analytics.
- The role of virtual reality in enhancing online education platforms.
- Investigating the effectiveness of various algorithms in reducing energy consumption in data centers.
- The impact of edge computing on the performance of mobile applications in remote areas.
- The application of computer vision techniques in automated medical diagnostics.
- Developing natural language processing tools for sentiment analysis in customer service.
- The use of augmented reality for training in high-risk industries like oil and gas.
- Investigating the challenges of integrating AI into legacy enterprise systems.
- The role of IT in managing supply chain disruptions during global crises.
- Developing adaptive cybersecurity strategies for small and medium-sized enterprises.
- The impact of 5G technology on the development of smart city solutions.
- The application of machine learning in personalized e-commerce recommendations.
- Investigating the use of cloud computing in improving government service delivery.
- The role of IT in enhancing sustainability in the manufacturing sector.
- Developing advanced algorithms for autonomous vehicle navigation.
- The application of biometrics in enhancing banking security systems.
- Investigating the ethical implications of facial recognition technology.
- The role of data analytics in optimizing healthcare delivery systems.
- Developing IoT solutions for efficient energy management in smart homes.
- The impact of mobile computing on the evolution of e-health services.
- The application of IT in disaster response and management.
Cybersecurity Research Ideas (Continued)
- Assessing the security implications of quantum computing on modern encryption methods.
- The role of artificial intelligence in detecting and preventing phishing attacks.
- Blockchain technology in secure voting systems: opportunities and challenges.
- Cybersecurity strategies for protecting smart grids from targeted attacks.
- Developing a cyber incident response framework for small to medium-sized enterprises.
- The effectiveness of behavioural biometrics in preventing identity theft.
- Securing Internet of Things (IoT) devices in healthcare: risks and solutions.
- Analysis of cyber warfare tactics and their implications on national security.
- Exploring the ethical boundaries of offensive cybersecurity measures.
- Machine learning algorithms for predicting and mitigating DDoS attacks.
- Study of cryptocurrency-related cybercrimes: patterns and prevention strategies.
- Evaluating the impact of GDPR on data breach response strategies in the EU.
- Developing enhanced security protocols for mobile banking applications.
- An examination of cyber espionage tactics and countermeasures.
- The role of human error in cybersecurity breaches: a behavioural analysis.
- Investigating the use of deep fakes in cyber fraud: detection and prevention.
- Cloud computing security: managing risks in multi-tenant environments.
- Next-generation firewalls: evaluating performance and security features.
- The impact of 5G technology on cybersecurity strategies and policies.
- Secure coding practices: reducing vulnerabilities in software development.
- Assessing the role of cyber insurance in mitigating financial losses from cyber attacks.
- Implementing zero trust architecture in corporate networks: challenges and benefits.
- Ransomware attacks on critical infrastructure: case studies and defence strategies.
- Using big data analytics for proactive cyber threat intelligence.
- Evaluating the effectiveness of cybersecurity awareness training in organisations.
Recent Cybersecurity-Related Studies
While the ideas we’ve presented above are a decent starting point for finding a research topic, they are fairly generic and non-specific. So, it helps to look at actual studies in the cybersecurity space to see how this all comes together in practice.
Below, we’ve included a selection of recent studies to help refine your thinking. These are actual studies, so they can provide some useful insight as to what a research topic looks like in practice.
- Cyber Security Vulnerability Detection Using Natural Language Processing (Singh et al., 2022)
- Security for Cloud-Native Systems with an AI-Ops Engine (Ck et al., 2022)
- Overview of Cyber Security (Yadav, 2022)
- Exploring the Top Five Evolving Threats in Cybersecurity: An In-Depth Overview (Mijwil et al., 2023)
- Cyber Security: Strategy to Security Challenges A Review (Nistane & Sharma, 2022)
- A Review Paper on Cyber Security (K & Venkatesh, 2022)
- The Significance of Machine Learning and Deep Learning Techniques in Cybersecurity: A Comprehensive Review (Mijwil, 2023)
- Towards Artificial Intelligence-Based Cybersecurity: The Practices and ChatGPT Generated Ways to Combat Cybercrime (Mijwil et al., 2023)
- ESTABLISHING CYBERSECURITY AWARENESS OF TECHNICAL SECURITY MEASURES THROUGH A SERIOUS GAME (Harding et al., 2022)
- Efficiency Evaluation of Cyber Security Based on EBM-DEA Model (Nguyen et al., 2022)
- An Overview of the Present and Future of User Authentication (Al Kabir & Elmedany, 2022)
- Cybersecurity Enterprises Policies: A Comparative Study (Mishra et al., 2022)
- The Rise of Ransomware: A Review of Attacks, Detection Techniques, and Future Challenges (Kamil et al., 2022)
- On the scale of Cyberspace and Cybersecurity (Pathan, 2022)
- Analysis of techniques and attacking pattern in cyber security approach (Sharma et al., 2022)
- Impact of Artificial Intelligence on Information Security in Business (Alawadhi et al., 2022)
- Deployment of Artificial Intelligence with Bootstrapped Meta-Learning in Cyber Security (Sasikala & Sharma, 2022)
- Optimization of Secure Coding Practices in SDLC as Part of Cybersecurity Framework (Jakimoski et al., 2022)
- CySSS ’22: 1st International Workshop on Cybersecurity and Social Sciences (Chan-Tin & Kennison, 2022)
As you can see, these research topics are a lot more focused than the generic topic ideas we presented earlier. So, for you to develop a high-quality research topic, you’ll need to get specific and laser-focused on a specific context with specific variables of interest. In the video below, we explore some other important things you’ll need to consider when crafting your research topic.
Get 1-On-1 Help
If you’re still unsure about how to find a quality research topic, check out our Research Topic Kickstarter service, which is the perfect starting point for developing a unique, well-justified research topic.

You Might Also Like:

Submit a Comment Cancel reply
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.
- Print Friendly
For enquiries call:
+1-469-442-0620

60+ Latest Cyber Security Research Topics in 2024
Home Blog Security 60+ Latest Cyber Security Research Topics in 2024
The concept of cybersecurity refers to cracking the security mechanisms that break in dynamic environments. Implementing Cyber Security Project topics and cybersecurity thesis topics helps overcome attacks and take mitigation approaches to security risks and threats in real-time. Undoubtedly, it focuses on events injected into the system, data, and the whole network to attack/disturb it.
The network can be attacked in various ways, including Distributed DoS, Knowledge Disruptions, Computer Viruses / Worms, and many more. Cyber-attacks are still rising, and more are waiting to harm their targeted systems and networks. Detecting Intrusions in cybersecurity has become challenging due to their Intelligence Performance. Therefore, it may negatively affect data integrity, privacy, availability, and security.
This article aims to demonstrate the most current Cyber Security Topics for Projects and areas of research currently lacking. We will talk about cyber security research questions, cyber security topics for the project, latest research titles about cyber security.
.jpg&w=3840&q=75)
List of Trending Cyber Security Research Topics in 2024
Digital technology has revolutionized how all businesses, large or small, work, and even governments manage their day-to-day activities, requiring organizations, corporations, and government agencies to utilize computerized systems. To protect data against online attacks or unauthorized access, cybersecurity is a priority. There are many Cyber Security Courses online where you can learn about these topics. With the rapid development of technology comes an equally rapid shift in Cyber Security Research Topics and cybersecurity trends, as data breaches, ransomware, and hacks become almost routine news items. In 2024, these will be the top cybersecurity trends.
A. Exciting Mobile Cyber Security Research Paper Topics
- The significance of continuous user authentication on mobile gadgets.
- The efficacy of different mobile security approaches.
- Detecting mobile phone hacking.
- Assessing the threat of using portable devices to access banking services.
- Cybersecurity and mobile applications.
- The vulnerabilities in wireless mobile data exchange.
- The rise of mobile malware.
- The evolution of Android malware.
- How to know you’ve been hacked on mobile.
- The impact of mobile gadgets on cybersecurity.
B. Top Computer and Software Security Topics to Research
- Learn algorithms for data encryption
- Concept of risk management security
- How to develop the best Internet security software
- What are Encrypting Viruses- How does it work?
- How does a Ransomware attack work?
- Scanning of malware on your PC
- Infiltrating a Mac OS X operating system
- What are the effects of RSA on network security ?
- How do encrypting viruses work?
- DDoS attacks on IoT devices
C. Trending Information Security Research Topics
- Why should people avoid sharing their details on Facebook?
- What is the importance of unified user profiles?
- Discuss Cookies and Privacy
- White hat and black hat hackers
- What are the most secure methods for ensuring data integrity?
- Talk about the implications of Wi-Fi hacking apps on mobile phones
- Analyze the data breaches in 2024
- Discuss digital piracy in 2024
- critical cyber-attack concepts
- Social engineering and its importance
D. Current Network Security Research Topics
- Data storage centralization
- Identify Malicious activity on a computer system.
- Firewall
- Importance of keeping updated Software
- wireless sensor network
- What are the effects of ad-hoc networks
- How can a company network be safe?
- What are Network segmentation and its applications?
- Discuss Data Loss Prevention systems
- Discuss various methods for establishing secure algorithms in a network.
- Talk about two-factor authentication
E. Best Data Security Research Topics
- Importance of backup and recovery
- Benefits of logging for applications
- Understand physical data security
- Importance of Cloud Security
- In computing, the relationship between privacy and data security
- Talk about data leaks in mobile apps
- Discuss the effects of a black hole on a network system.
F. Important Application Security Research Topics
- Detect Malicious Activity on Google Play Apps
- Dangers of XSS attacks on apps
- Discuss SQL injection attacks.
- Insecure Deserialization Effect
- Check Security protocols
G. Cybersecurity Law & Ethics Research Topics
- Strict cybersecurity laws in China
- Importance of the Cybersecurity Information Sharing Act.
- USA, UK, and other countries' cybersecurity laws
- Discuss The Pipeline Security Act in the United States
H. Recent Cyberbullying Topics
- Protecting your Online Identity and Reputation
- Online Safety
- Sexual Harassment and Sexual Bullying
- Dealing with Bullying
- Stress Center for Teens
I. Operational Security Topics
- Identify sensitive data
- Identify possible threats
- Analyze security threats and vulnerabilities
- Appraise the threat level and vulnerability risk
- Devise a plan to mitigate the threats
J. Cybercrime Topics for a Research Paper
- Crime Prevention.
- Criminal Specialization.
- Drug Courts.
- Criminal Courts.
- Criminal Justice Ethics.
- Capital Punishment.
- Community Corrections.
- Criminal Law.
Cyber Security Future Research Topics
- Developing more effective methods for detecting and responding to cyber attacks
- Investigating the role of social media in cyber security
- Examining the impact of cloud computing on cyber security
- Investigating the security implications of the Internet of Things
- Studying the effectiveness of current cyber security measures
- Identifying new cyber security threats and vulnerabilities
- Developing more effective cyber security policies
- Examining the ethical implications of cyber security
Cyber Security Topics For Research Paper
- Cyber security threats and vulnerabilities
- Cyber security incident response and management
- Cyber security risk management
- Cyber security awareness and training
- Cyber security controls and countermeasures
- Cyber security governance
- Cyber security standards
- Cyber security insurance
- Cyber security and the law
- The future of cyber security
5 Current Research Topics in Cybersecurity
Below are the latest 5 cybersecurity research topics. They are:
- Artificial Intelligence
- Digital Supply Chains
- Internet of Things
- State-Sponsored Attacks
- Working From Home
Research Area in Cyber Security
The field of cyber security is extensive and constantly evolving. Its research covers a wide range of subjects, including:
- Quantum & Space
- Data Privacy
- Criminology & Law
- AI & IoT Security
- RFID Security
- Authorisation Infrastructure
- Digital Forensics
- Autonomous Security
- Social Influence on Social Networks
How to Choose the Best Research Topics in Cyber Security
A good cybersecurity assignment heading is a skill that not everyone has, and unfortunately, not everyone has one. You might have your teacher provide you with the topics, or you might be asked to come up with your own. If you want more research topics, you can take references from Certified Ethical Hacker Certification, where you will get more hints on new topics. If you don't know where to start, here are some tips. Follow them to create compelling cybersecurity assignment topics.
1. Brainstorm
In order to select the most appropriate heading for your cybersecurity assignment, you first need to brainstorm ideas. What specific matter do you wish to explore? In this case, come up with relevant topics about the subject and select those relevant to your issue when you use our list of topics. You can also go to cyber security-oriented websites to get some ideas. Using any blog post on the internet can prove helpful if you intend to write a research paper on security threats in 2024. Creating a brainstorming list with all the keywords and cybersecurity concepts you wish to discuss is another great way to start. Once that's done, pick the topics you feel most comfortable handling. Keep in mind to stay away from common topics as much as possible.
2. Understanding the Background
In order to write a cybersecurity assignment, you need to identify two or three research paper topics. Obtain the necessary resources and review them to gain background information on your heading. This will also allow you to learn new terminologies that can be used in your title to enhance it.
3. Write a Single Topic
Make sure the subject of your cybersecurity research paper doesn't fall into either extreme. Make sure the title is neither too narrow nor too broad. Topics on either extreme will be challenging to research and write about.
4. Be Flexible
There is no rule to say that the title you choose is permanent. It is perfectly okay to change your research paper topic along the way. For example, if you find another topic on this list to better suit your research paper, consider swapping it out.
The Layout of Cybersecurity Research Guidance
It is undeniable that usability is one of cybersecurity's most important social issues today. Increasingly, security features have become standard components of our digital environment, which pervade our lives and require both novices and experts to use them. Supported by confidentiality, integrity, and availability concerns, security features have become essential components of our digital environment.
In order to make security features easily accessible to a wider population, these functions need to be highly usable. This is especially true in this context because poor usability typically translates into the inadequate application of cybersecurity tools and functionality, resulting in their limited effectiveness.
Writing Tips from Expert
Additionally, a well-planned action plan and a set of useful tools are essential for delving into Cyber Security Research Topics. Not only do these topics present a vast realm of knowledge and potential innovation, but they also have paramount importance in today's digital age. Addressing the challenges and nuances of these research areas will contribute significantly to the global cybersecurity landscape, ensuring safer digital environments for all. It's crucial to approach these topics with diligence and an open mind to uncover groundbreaking insights.
- Before you begin writing your research paper, make sure you understand the assignment.
- Your Research Paper Should Have an Engaging Topic
- Find reputable sources by doing a little research
- Precisely state your thesis on cybersecurity
- A rough outline should be developed
- Finish your paper by writing a draft
- Make sure that your bibliography is formatted correctly and cites your sources.
Discover the Power of ITIL 4 Foundation - Unleash the Potential of Your Business with this Cost-Effective Solution. Boost Efficiency, Streamline Processes, and Stay Ahead of the Competition. Learn More!
Studies in the literature have identified and recommended guidelines and recommendations for addressing security usability problems to provide highly usable security. The purpose of such papers is to consolidate existing design guidelines and define an initial core list that can be used for future reference in the field of Cyber Security Research Topics.
The researcher takes advantage of the opportunity to provide an up-to-date analysis of cybersecurity usability issues and evaluation techniques applied so far. As a result of this research paper, researchers and practitioners interested in cybersecurity systems who value human and social design elements are likely to find it useful. You can find KnowledgeHut’s Cyber Security courses online and take maximum advantage of them.
Frequently Asked Questions (FAQs)
Businesses and individuals are changing how they handle cybersecurity as technology changes rapidly - from cloud-based services to new IoT devices.
Ideally, you should have read many papers and know their structure, what information they contain, and so on if you want to write something of interest to others.
The field of cyber security is extensive and constantly evolving. Its research covers various subjects, including Quantum & Space, Data Privacy, Criminology & Law, and AI & IoT Security.
Inmates having the right to work, transportation of concealed weapons, rape and violence in prison, verdicts on plea agreements, rehab versus reform, and how reliable are eyewitnesses?

Mrinal Prakash
I am a B.Tech Student who blogs about various topics on cyber security and is specialized in web application security
Avail your free 1:1 mentorship session.
Something went wrong
Upcoming Cyber Security Batches & Dates

- Calculators
- Swot Analysis
- Pestle Analysis
- Five Forces Analysis
- Organizational Structure
- Copywriting
- Research Topics
- Student Resources
Services We Provide

Resources We Provide

Login / Register

- 15 Latest Networking Research Topics for Students
Comparative analysis between snort and suricata IDS software(s)
Description of the topic
The main focus of this research is to conduct a comparative analysis between Snort and Suricata software to determine which IDS software can provide better performance. There are various IDS software(s) available that can be used by organizations but it is difficult to identify which one is best (Aldarwbi et al., 2022). Different organizational structures are often facing problems while setting up an IDS system which results in false positives and intrusions. Through this research, it can be identified which IDS software is better and what secure configuration is required to detect intrusions (Waleed et al., 2022).
Research objectives
- To evaluate Snort and Suricata IDS software(s) to determine the most optimal one.
- To identify the false positive rate of Snort and Suricata on the networked environment.
Research questions
RQ1: Which IDS software can perform better on the production network in terms of performance, security, scalability and reliability?
RQ2: What different ways can be followed to deal with false positive problems in IDS technology?
Research methodology
The given research objectives and research questions can be addressed using quantitative research methodology where an experimental approach can be followed. For the given topic, both Snort and Suricata IDS systems should be configured and tested against different attacks. Depending on the findings, it can be analyzed which IDS software can perform better in terms of performance and security (Shuai & Li, 2021).
- Aldarwbi, M.Y., Lashkari, A.H. and Ghorbani, A.A. (2022) “The sound of intrusion: A novel network intrusion detection system,” Computers and Electrical Engineering , 104, p. 108455.
- Shuai, L. and Li, S. (2021) “Performance optimization of Snort based on DPDK and Hyperscan,” Procedia Computer Science , 183, pp. 837-843.
- Waleed, A., Jamali, A.F. and Masood, A. (2022) “Which open-source ids? Snort, Suricata or Zeek,” Computer Networks , 213, p. 109116.
Role of honeypots and honey nets in network security
Network Security has become essential nowadays and there is a need for setting up robust mechanisms to maintain confidentiality and integrity (Feng et al., 2023). Due to the number of security mechanisms available, organizations found it hard to finalize and implement them on their network. For example, honey pots and honeynet approaches look almost the same and have the same purpose but work differently. Under this research topic, the configuration of honeynets and honeypots can be done to check which one can perform better security in terms of trapping cyber attackers. The entire implementation can be carried out in the cloud-based instance for improved security and it can be identified which type of honey pot technology must be preferred (Maesschalck et al., 2022).
- To set up a honey pot system using Open Canary on the virtual instance to protect against cyber attackers.
- To set up a honeynet system on the virtual instance to assure protection is provided against malicious attackers.
- To test honeypots and honeynets by executing DDoS attacks to check which can provide better security.
RQ1: Why is there a need for using honeypots over honey pots in a production networked environment?
RQ2: What are the differences between cloud-based and local honey pot systems for endpoint protection?
This research can be carried out using the quantitative method of research. At the initial stage, the implementation of honeypots and honeypots can be done on the virtual instance following different security rules. Once the rules are applied, the testing can be performed using a Kali Linux machine to check whether honey pots were effective or honeynets (Gill et al., 2020).
- Feng, H. et al. (2023) “Game theory in network security for Digital Twins in industry,” Digital Communications and Networks [Preprint].
- Gill, K.S., Saxena, S. and Sharma, A. (2020) “GTM-CSEC: A game theoretic model for cloud security based on ids and Honeypot,” Computers & Security , 92, p. 101732
- Maesschalck, S. et al. (2022) “Don’t get stung, cover your ICS in honey: How do honeypots fit within industrial control system security,” Computers & Security , 114, p. 102598.
How do malware variants are progressively improving?
This research can be based on evaluating how malware variants are progressively improving and what should be its state in the coming future. Malware is able to compromise confidential user’s information assets which is why this research can be based on identifying current and future consequences owing to its improvements (Deng et al., 2023). In this field, there is no research work that has been carried out to identify how malware variants are improving their working and what is expected to see in future. Once the evaluation is done, a clear analysis can also be done on some intelligent preventive measures to deal with dangerous malware variants and prevent any kind of technological exploitation (Tang et al., 2023).
- To investigate types of malware variants available to learn more about malware's hidden features.
- To focus on future implications of malware executable programs and how they can be avoided.
- To discuss intelligent solutions to deal with all malware variants.
RQ1: How do improvements in malware variants impact enterprises?
RQ2: What additional solutions are required to deal with malware variants?
In this research, qualitative analysis can be conducted on malware variants and the main reason behind their increasing severity. The entire research can be completed based on qualitative research methodology to answer defined research questions and objectives. Some real-life case studies should also be integrated into the research which can be supported by the selected topic (Saidia Fasci et al., 2023).
- Deng, H. et al. (2023) “MCTVD: A malware classification method based on three-channel visualization and deep learning,” Computers & Security , 126, p. 103084.
- Saidia Fasci, L. et al. (2023) “Disarming visualization-based approaches in malware detection systems,” Computers & Security , 126, p. 103062.
- Tang, Y. et al. (2023) “BHMDC: A byte and hex n-gram based malware detection and classification method,” Computers & Security , p. 103118.
Implementation of IoT - enabled smart office/home using cisco packet tracer
The Internet of Things has gained much more attention over the past few years which is why each enterprise and individual aims at setting up an IoT network to automate their processes (Barriga et al., 2023). This research can be based on designing and implementing an IoT-enabled smart home/office network using Cisco Packet Tracer software. Logical workspace, all network devices, including IoT devices can be used for preparing a logical network star topology (Elias & Ali, 2014). To achieve automation, the use of different IoT rules can be done to allow devices to work based on defined rules.
- To set up an IoT network on a logical workspace using Cisco Packet Tracer simulation software.
- To set up IoT-enabled rules on an IoT registration server to achieve automation (Hou et al., 2023).
RQ: Why is the Cisco packet tracer preferred for network simulation over other network simulators?
At the beginning of this research, a quantitative research methodology can be followed where proper experimental set-up can be done. As a packet tracer is to be used, the star topology can be used to interconnect IoT devices, sensors and other network devices at the home/office. Once a placement is done, the configuration should be done using optimal settings and all IoT devices can be connected to the registration server. This server will have IoT rules which can help in achieving automation by automatically turning off lights and fans when no motion is detected (Baggan et al., 2022).
- Baggan, V. et al. (2022) “A comprehensive analysis and experimental evaluation of Routing Information Protocol: An Elucidation,” Materials Today: Proceedings , 49, pp. 3040–3045.
- Barriga, J.A. et al. (2023) “Design, code generation and simulation of IOT environments with mobility devices by using model-driven development: Simulateiot-Mobile,” Pervasive and Mobile Computing , 89, p. 101751.
- Elias, M.S. and Ali, A.Z. (2014) “Survey on the challenges faced by the lecturers in using packet tracer simulation in computer networking course,” Procedia - Social and Behavioral Sciences , 131, pp. 11–15.
- Hou, L. et al. (2023) “Block-HRG: Block-based differentially private IOT networks release,” Ad Hoc Networks , 140, p. 103059.
Comparative analysis between AODV, DSDV and DSR routing protocols in WSN networks
For wireless sensor networks (WSN), there is a major need for using WSN routing rather than performing normal routines. As WSN networks are self-configured, there is a need for an optimal routing protocol that can improve network performance in terms of latency, jitter, and packet loss (Luo et al., 2023). There are often various problems faced when WSN networks are set up due to a lack of proper routing protocol selection. As a result of this, severe downtime is faced and all links are not able to communicate with each other easily (Hemanand et al., 2023). In this research topic, the three most widely used WSN routing protocols AODV, DSDV and DSR can be compared based on network performance. To perform analysis, three different scenarios can be created in network simulator 2 (Ns2).
- To create three different scenarios on ns2 software to simulate a network for 1 to 100 seconds.
- To analyze which WSN routing is optimal in terms of network performance metrics, including latency, jitter and packet loss.
- To use CBR and NULL agents for all wireless scenarios to start with simulation purposes.
RQ: How do AODV, DSR and DSDV routing protocols differ from each other in terms of network performance?
This research can be carried out using a quantitative research method. The implementation for the provided research topic can be based on Ns2 simulation software where three different scenarios can be created (AODV, DSDV and DSR). For each scenario, NULL, CSR and UDP agents can be done to start with simulation for almost 1 to 100 seconds. For all transmissions made during the given time, network performance can be checked to determine which routing is best (Mohapatra & Kanungo, 2012).
- Human and, D. et al. (2023) “Analysis of power optimization and enhanced routing protocols for Wireless Sensor Networks,” Measurement: Sensors , 25, p. 100610. Available at: https://doi.org/10.1016/j.measen.2022.100610.
- Luo, S., Lai, Y. and Liu, J. (2023) “Selective forwarding attack detection and network recovery mechanism based on cloud-edge cooperation in software-defined wireless sensor network,” Computers & Security , 126, p. 103083. Available at: https://doi.org/10.1016/j.cose.2022.103083.
- Mohapatra, S. and Kanungo, P. (2012) “Performance analysis of AODV, DSR, OLSR and DSDV routing protocols using NS2 Simulator,” Procedia Engineering , 30, pp. 69–76. Available at: https://doi.org/10.1016/j.proeng.2012.01.835.
Securing wireless network using AAA authentication and WLAN controller
Wireless networks often face intrusion attempts due to insecure protocols and sometimes open SSIDs. As a result of this, man-in-the-middle and eavesdropping attacks become easier which results in the loss of confidential information assets (Sivasankari & Kamalakkannan, 2022). When it comes to managing networks in a large area, there are higher chances for attacks that enable cyber attackers in intercepting ongoing communication sessions. However, there is currently no research conducted where the use of AAA authentication has been done with WLAN controllers to make sure a higher level of protection is provided (Nashwan, 2021). The proposed research topic can be based on securing wireless networks with the help of AAA authentication and WLAN controllers. The use of AAA authentication can be done to set up a login portal for users whilst the WLAN controller can be used for managing all wireless access points connected to the network (Nashwan, 2021).
- To set up AAA authentication service on the wireless network simulated on Cisco Packet Tracer for proper access control.
- To set up a WLAN controller on the network to manage all wireless access points effortlessly.
- To use WPA2-PSK protocol on the network to assure guest users are only able to access wireless networks over a secure protocol.
RQ1: What additional benefits are offered by AAA authentication on the WLAN networks?
RQ2: Why are wireless networks more likely to face network intrusions than wired networks?
This research topic is based on the secure implementation of a wireless LAN network using a Cisco packet tracer. Hence, this research can be carried out using a quantitative research method. The implementation can be carried out using AAA authentication which can assure that access control is applied for wireless logins. On the other hand, a WLAN controller can also be configured which can ensure that all WAPs are managed (ZHANG et al., 2012).
- Nashwan, S. (2021) “AAA-WSN: Anonymous Access Authentication Scheme for wireless sensor networks in Big Data Environment,” Egyptian Informatics Journal , 22(1), pp. 15–26.
- Sivasankari, N. and Kamalakkannan, S. (2022) “Detection and prevention of man-in-the-middle attack in IOT network using regression modeling,” Advances in Engineering Software , 169, p. 103126.
- ZHANG, J. et al. (2012) “AAA authentication for Network mobility,” The Journal of China Universities of Posts and Telecommunications , 19(2), pp. 81-86.
OWASP's approach to secure web applications from web application exploits
The research can revolve around the development of web applications by considering OWASP's top 10 rules. Usually, web applications are deployed by organizations depending on their requirements and these applications are vulnerable to various exploits, including injection, broken authentication and other forgery attacks (Poston, 2020). Identifying every single vulnerability is difficult when reference is not taken and often organizations end up hosting a vulnerable server that leads to privacy issues and compromises confidential information easily. In this research, OWASP's top 10 approaches can be followed to develop a secure web application that can be able to protect against top web application exploits. This approach is based on emphasizing severe and minor vulnerabilities which must be patched for protecting against web application attacks (Deepa & Thilagam, 2016).
- The first objective can be setting up an insecure web application on the cloud environment which can be exploited with different techniques.
- The second objective can be to consider all techniques and procedures provided by OWASP's top 10 methodologies.
- The last objective can be applying all fixes to insecure web applications to make them resistant to OWASP top 10 attacks (Sonmez, 2019).
RQ1: What are the benefits of using OWASP's top 10 approaches to harden web applications in comparison to other security approaches?
The research methodology considered for this research project can be quantitative using an experimental approach. The practical work can be done for the selected topic using AWS or the Azure cloud platform. Simply, a virtual web server can be configured and set up with a secure and insecure web application. Following OWASP's top 10 techniques and procedures, the web application can be secured from possible attacks. In addition, insecure applications can also be exploited and results can be evaluated (Applebaum et al., 2021).
- Applebaum, S., Gaber, T. and Ahmed, A. (2021) “Signature-based and machine-learning-based web application firewalls: A short survey,” Procedia Computer Science , 189, pp. 359–367. Available at: https://doi.org/10.1016/j.procs.2021.05.105.
- Deepa, G. and Thilagam, P.S. (2016) “Securing web applications from injection and logic vulnerabilities: Approaches and challenges,” Information and Software Technology , 74, pp. 160–180. Available at: https://doi.org/10.1016/j.infsof.2016.02.005.
- Poston, H. (2020) “Mapping the owasp top Ten to the blockchain,” Procedia Computer Science , 177, pp. 613-617. Available at: https://doi.org/10.1016/j.procs.2020.10.087.
- Sonmez, F.Ö. (2019) “Security qualitative metrics for Open Web Application Security Project Compliance,” Procedia Computer Science , 151, pp. 998-1003. Available at: https://doi.org/10.1016/j.procs.2019.04.140.
Importance of configuring RADIUS (AAA) server on the network
User authentication has become significant nowadays as it guarantees that a legitimate user is accessing the network. But a problem is faced when a particular security control is to be identified for authentication and authorization. These controls can be categorized based on mandatory access controls, role-based access control, setting up captive portals and many more. Despite several other security controls, one of the most efficient ones is the RADIUS server (SONG et al., 2008). This server can authenticate users on the network to make sure network resources are accessible to only legal users. This research topic can be based on understanding the importance of RADIUS servers on the network which can also be demonstrated with the help of the Cisco Packet Tracer. A network can be designed and equipped with a RADIUS server to ensure only legal users can access network resources (WANG et al., 2009).
- To configure RADIUS (AAA) server on the network which can be able to authenticate users who try to access network resources.
- To simulate a network on a packet tracer simulation software and verify network connectivity.
RQ1: What are other alternatives to RADIUS (AAA) authentication servers for network security?
RQ2: What are the common and similarities between RADIUS and TACACS+ servers?
As a logical network is to be designed and configured, a quantitative research methodology can be followed. In this research coursework, a secure network design can be done using a packet tracer network simulator, including a RADIUS server along with the DMZ area. The configuration for the RADIUS server can be done to allow users to only access network resources by authenticating and authorizing (Nugroho et al., 2022).
- Nugroho, Y.S. et al. (2022) “Dataset of network simulator related-question posts in stack overflow,” Data in Brief , 41, p. 107942.
- SONG, M., WANG, L. and SONG, J.-de (2008) “A secure fast handover scheme based on AAA protocol in Mobile IPv6 Networks,” The Journal of China Universities of Posts and Telecommunications , 15, pp. 14-18.
- WANG, L. et al. (2009) “A novel congestion control model for interworking AAA in heterogeneous networks,” The Journal of China Universities of Posts and Telecommunications , 16, pp. 97-101.
Comparing mod security and pF sense firewall to block illegitimate traffic
Firewalls are primarily used for endpoint security due to their advanced features ranging from blocking to IDS capabilities and many more. It is sometimes challenging to identify which type of firewall is best and due to this reason, agencies end up setting up misconfigured firewalls (Tiwari et al., 2022). This further results in a cyber breach, destroying all business operations. The research can be emphasizing conducting a comparison between the two most widely used firewalls i.e. Mod Security and pF sense. Using a virtualized environment, both firewalls can be configured and tested concerning possible cyber-attacks (Lu & Yang, 2020).
- To use the local environment to set up Mod security and pF sense firewall with appropriate access control rules.
- To test both firewalls by executing distributed denial of service attacks from a remote location.
- To compare which type of firewall can provide improved performance and robust security.
RQ: How do Mod security and pF sense differ from each other in terms of features and performance?
The practical experimentation for both firewalls can be done using a virtualized environment where two different machines can be created. Hence, this research can be carried out using a quantitative research method . The first machine can have Mod security and the second machine can have pF sense configured. A new subnet can be created which can have these two machines. The third machine can be an attacking machine which can be used for testing firewalls. The results obtained can be then evaluated to identify which firewall is best for providing security (Uçtu et al., 2021).
- Lu, N. and Yang, Y. (2020) “Application of evolutionary algorithm in performance optimization of Embedded Network Firewall,” Microprocessors and Microsystems , 76, p. 103087.
- Tiwari, A., Papini, S. and Hemamalini, V. (2022) “An enhanced optimization of parallel firewalls filtering rules for scalable high-speed networks,” Materials Today: Proceedings , 62, pp. 4800-4805.
- Uçtu, G. et al. (2021) “A suggested testbed to evaluate multicast network and threat prevention performance of Next Generation Firewalls,” Future Generation Computer Systems , 124, pp. 56-67.
Conducting a comprehensive investigation on the PETYA malware
The main purpose of this research is to conduct a comprehensive investigation of the PETYA malware variant (McIntosh et al., 2021). PETYA often falls under the category of ransomware attacks which not only corrupt and encrypt files but can compromise confidential information easily. Along with PETYA, there are other variants also which lead to a security outage and organizations are not able to detect these variants due to a lack of proper detection capabilities (Singh & Singh, 2021). In this research, a comprehensive analysis has been done on PETYA malware to identify its working and severity level. Depending upon possible causes of infection of PETYA malware, some proactive techniques can also be discussed (Singh & Singh, 2021). A separation discussion can also be made on other malware variants, their features, and many more.
- The main objective of this research is to scrutinize the working of PETYA malware because a ransomware attack can impact the micro and macro environment of the organizations severely.
- The working of PETYA malware along with its source code can be reviewed to identify its structure and encryption type.
- To list all possible CVE IDs which are exploited by the PETYA malware.
RQ1: How dangerous is PETYA malware in comparison to other ransomware malware?
This research can be based on qualitative research methodology to evaluate the working of PETYA malware from various aspects, the methodology followed and what are its implications. The research can be initiated by evaluating the working of PETYA malware, how it is triggered, what encryption is applied and other factors. A sample source code can also be analyzed to learn more about how cryptography is used with ransomware (Abijah Roseline & Geetha, 2021).
- Abijah Roseline, S. and Geetha, S. (2021) “A comprehensive survey of tools and techniques mitigating computer and mobile malware attacks,” Computers & Electrical Engineering , 92, p. 107143.
- McIntosh, T. et al. (2021) “Enforcing situation-aware access control to build malware-resilient file systems,” Future Generation Computer Systems , 115, pp. 568-582.
- Singh, J. and Singh, J. (2021) “A survey on machine learning-based malware detection in executable files,” Journal of Systems Architecture , 112, p. 101861.
Setting up a Live streaming server on the cloud platform
Nowadays, various organizations require a live streaming server to stream content depending upon their business. However, due to a lack of proper hardware, organizations are likely to face high network congestion, slowness and other problems (Ji et al., 2023). Referring to the recent cases, it has been observed that setting up a streaming server on the local environment is not expected to perform better than a cloud-based streaming server configuration (Martins et al., 2019). This particular research topic can be based on setting up a live streaming server on the AWS or Azure cloud platform to make sure high network bandwidth is provided with decreased latency. The research gap analysis would be conducted to analyze the performance of live streaming servers on local and cloud environments in terms of network performance metrics (Bilal et al., 2018).
- To set up a live streaming server on the AWS or Azure cloud platform to provide live streaming services.
- To use load balancers alongside streaming servers to ensure the load is balanced and scalability is achieved.
- To use Wireshark software to test network performance during live streaming.
RQ1: Why are in-house streaming servers not able to provide improved performance in comparison to cloud-based servers?
RQ2: What additional services are provided by cloud service providers which help in maintaining network performance?
The implementation is expected to carry out on the AWS cloud platform with other AWS services i.e. load balancer, private subnet and many more (Efthymiopoulou et al., 2017). Hence, this research can be carried out using a quantitative research method. The configuration of ec2 instances can be done which can act as a streaming server for streaming media and games. For testing this project, the use of OBS studio can be done which can help in checking whether streaming is enabled or not. For network performance, Wireshark can be used for testing network performance (George et al., 2020).
- Bilal, KErbad, A. and Hefeeda, M. (2018) “QoE-aware distributed cloud-based live streaming of multi-sourced Multiview Videos,” Journal of Network and Computer Applications , 120, pp. 130-144.
- Efthymiopoulou, M. et al. (2017) “Robust control in cloud-assisted peer-to-peer live streaming systems,” Pervasive and Mobile Computing , 42, pp. 426-443.
- George, L.C. et al. (2020) “Usage visualization for the AWS services,” Procedia Computer Science , 176, pp. 3710–3717.
- Ji, X. et al. (2023) “Adaptive QoS-aware multipath congestion control for live streaming,” Computer Networks , 220, p. 109470.
- Martins, R. et al. (2019) “Iris: Secure reliable live-streaming with Opportunistic Mobile Edge Cloud offloading,” Future Generation Computer Systems , 101, pp. 272-292.
Significance of using OSINT framework for Network reconnaissance
Network reconnaissance is becoming important day by day when it comes to penetration testing. Almost all white hat hackers are dependent on the OSINT framework to start with network reconnaissance and footprinting when it comes to evaluating organizational infrastructure. On the other hand, cyber attackers are also using this technique to start fetching information about their target. Currently, there is no investigation carried out to identify how effective the OSINT framework is over traditional reconnaissance activities (Liu et al., 2022). This research is focused on using OSINT techniques to analyze victims using different sets of tools like Maltego, email analysis and many other techniques. The analysis can be based on fetching sensitive information about the target which can be used for conducting illegal activities (Abdullah, 2019).
- To use Maltego software to conduct network reconnaissance on the target by fetching sensitive information.
- To compare the OSINT framework with other techniques to analyze why it performs well.
RQ1: What is the significance of using the OSINT framework in conducting network reconnaissance?
RQ2: How can the OSINT framework be used by cyber hackers for conducting illegitimate activities?
The OSINT framework is easily accessible on its official website where different search options are given. Hence, this research can be carried out using a quantitative research method. Depending upon the selected target, each option can be selected and tools can be shortlisted for final implementation. Once the tools are shortlisted, they can be used to conduct network reconnaissance (González-Granadillo et al., 2021). For example, Maltego can be used as it is a powerful software to fetch information about the target.
- Abdullah, S.A. (2019) “Seui-64, bits an IPv6 addressing strategy to mitigate reconnaissance attacks,” Engineering Science and Technology , an International Journal, 22(2), pp. 667–672.
- Gonzalez-Granadillo, G. et al. (2021) “ETIP: An enriched threat intelligence platform for improving OSINT correlation, analysis, visualization and sharing capabilities,” Journal of Information Security and Applications , 58, p. 102715.
- Liu, W. et al. (2022) “A hybrid optimization framework for UAV Reconnaissance Mission Planning,” Computers & Industrial Engineering , 173, p. 108653.
Wired and wireless network hardening in cisco packet tracer
At present, network security has become essential and if enterprises are not paying attention to the security infrastructure, there are several chances for cyber breaches. To overcome all these issues, there is a need for setting up secure wired and wireless networks following different techniques such as filtered ports, firewalls, VLANs and other security mechanisms. For the practical part, the use of packet tracer software can be done to design and implement a highly secure network (Sun, 2022).
- To use packet tracer simulation software to set up secure wired and wireless networks.
- Use different hardening techniques, including access control rules, port filtering, enabling passwords and many more to assure only authorized users can access the network (Zhang et al., 2012).
RQ: Why is there a need for emphasizing wired and wireless network security?
Following the quantitative approach, the proposed research topic implementation can be performed in Cisco Packet Tracer simulation software. Several devices such as routers, switches, firewalls, wireless access points, hosts and workstations can be configured and interconnected using Cat 6 e cabling. For security, every device can be checked and secure design principles can be followed like access control rules, disabled open ports, passwords, encryption and many more (Smith & Hasan, 2020).
- Smith, J.D. and Hasan, M. (2020) “Quantitative approaches for the evaluation of Implementation Research Studies,” Psychiatry Research , 283, p. 112521.
- Sun, J. (2022) “Computer Network Security Technology and prevention strategy analysis,” Procedia Computer Science , 208, pp. 570–576.
- Zhang, YLiang, R. and Ma, H. (2012) “Teaching innovation in computer network course for undergraduate students with a packet tracer,” IERI Procedia , 2, pp. 504–510.
Different Preemptive ways to resist spear phishing attacks
When it comes to social engineering, phishing attacks are rising and are becoming one of the most common ethical issues as it is one of the easiest ways to trick victims into stealing information. This research topic is based on following different proactive techniques which would help in resisting spear phishing attacks (Xu et al., 2023). This can be achieved by using the Go-Phish filter on the machine which can automatically detect and alert users as soon as the phished URL is detected. It can be performed on the cloud platform where the apache2 server can be configured along with an anti-phishing filter to protect against phishing attacks (Yoo & Cho, 2022).
- To set up a virtual instance on the cloud platform with an apache2 server and anti-phishing software to detect possible phishing attacks.
- To research spear phishing and other types of phishing attacks that can be faced by victims (Al-Hamar et al., 2021).
RQ1: Are phishing attacks growing just like other cyber-attacks?
RQ2: How effective are anti-phishing filters in comparison to cyber awareness sessions?
The entire research can be conducted by adhering to quantitative research methodology which helps in justifying all research objectives and questions. The implementation of the anti-phishing filter can be done by creating a virtual instance on the cloud platform which can be configured with an anti-phishing filter. Along with this, some phishing attempts can also be performed to check whether the filter works or not (Siddiqui et al., 2022).
- Al-Hamar, Y. et al. (2021) “Enterprise credential spear-phishing attack detection,” Computers & Electrical Engineering , 94, p. 107363.
- Siddiqui, N. et al. (2022) “A comparative analysis of US and Indian laws against phishing attacks,” Materials Today: Proceedings , 49, pp. 3646–3649.
- Xu, T., Singh, K. and Rajivan, P. (2023) “Personalized persuasion: Quantifying susceptibility to information exploitation in spear-phishing attacks,” Applied Ergonomics , 108, p. 103908.
- Yoo, J. and Cho, Y. (2022) “ICSA: Intelligent chatbot security assistant using text-CNN and multi-phase real-time defense against SNS phishing attacks,” Expert Systems with Applications , 207, p. 117893.
Evaluating the effectiveness of distributed denial of service attacks
The given research topic is based on evaluating the effectiveness of distributed denial of service attacks on cloud and local environments. Hence, this research can be carried out using a quantitative research method. Cyber attackers find DDoS as one of the most dangerous technological exploitation when it comes to impacting network availability (Krishna Kishore et al., 2023). This research can revolve around scrutinizing the impact of DDoS attacks on the local environment and cloud environment. This can be done by executing DDoS attacks on a simulated environment using hoping or other software(s) to check where it has a higher magnitude (de Neira et al., 2023).
- To set up a server on the local and cloud environment to target using DDoS attacks for checking which had experienced slowness.
- To determine types of DDoS attack types, their magnitude and possible mitigation techniques.
RQ: Why do DDoS attacks have dynamic nature and how is it likely to sternly impact victims?
The experimentation for this research can be executed by creating a server on the local and cloud environment. Hence, this research can be carried out using a quantitative research method. These servers can be set up as web servers using apache 2 service. On the other hand, a Kali Linux machine can be configured with DDoS execution software. Each server can be targeted with DDoS attacks to check its effectiveness (Benlloch-Caballero et al., 2023).
- Benlloch-Caballero, P., Wang, Q. and Alcaraz Calero, J.M. (2023) “Distributed dual-layer autonomous closed loops for self-protection of 5G/6G IOT networks from distributed denial of service attacks,” Computer Networks , 222, p. 109526.
- de Neira, A.B., Kantarci, B. and Nogueira, M. (2023) “Distributed denial of service attack prediction: Challenges, open issues and opportunities,” Computer Networks , 222, p. 109553.
- Krishna Kishore, P., Ramamoorthy, S. and Rajavarman, V.N. (2023) “ARTP: Anomaly-based real time prevention of distributed denial of service attacks on the web using machine learning approach,” International Journal of Intelligent Networks , 4, pp. 38–45.
Recommended Readings
Latest Web Development Research Topics
Top Management Research Topics
Newest AI Research Topics
Research in every field is becoming more and more essential because of constant developments around the world. Similar is the case in the field of networking. This is the reason; students who are preparing to master the field of networking need to keep their knowledge of the current state of the art in the field up to date.
However, choosing the right research topic often becomes a tough task for students to carry out their research effectively. That being the case, this list contains 15 latest research topics in the field of networking. Whether you are a seasoned researcher or just starting, this list can provide you with ample inspiration and guidance to drive your research forward in the dynamic and evolving field of Networking.
Copyright © 2023 CrowJack. All Rights Reserved
network security Recently Published Documents
Total documents.
- Latest Documents
- Most Cited Documents
- Contributed Authors
- Related Sources
- Related Keywords
A Survey on Ransomware Malware and Ransomware Detection Techniques
Abstract: is a kind of malignant programming (malware) that takes steps to distribute or hinders admittance to information or a PC framework, for the most part by scrambling it, until the casualty pays a payoff expense to the assailant. As a rule, the payoff request accompanies a cutoff time. Assuming that the casualty doesn't pay on schedule, the information is gone perpetually or the payoff increments. Presently days and assailants executed new strategies for effective working of assault. In this paper, we center around ransomware network assaults and study of discovery procedures for deliver product assault. There are different recognition methods or approaches are accessible for identification of payment product assault. Keywords: Network Security, Malware, Ransomware, Ransomware Detection Techniques
Analysis and Evaluation of Wireless Network Security with the Penetration Testing Execution Standard (PTES)
The use of computer networks in an agency aims to facilitate communication and data transfer between devices. The network that can be applied can be using wireless media or LAN cable. At SMP XYZ, most of the computers still use wireless networks. Based on the findings in the field, it was found that there was no user management problem. Therefore, an analysis and audit of the network security system is needed to ensure that the network security system at SMP XYZ is safe and running well. In conducting this analysis, a tool is needed which will be used as a benchmark to determine the security of the wireless network. The tools used are Penetration Testing Execution Standard (PTES) which is one of the tools to become a standard in analyzing or auditing network security systems in a company in this case, namely analyzing and auditing wireless network security systems. After conducting an analysis based on these tools, there are still many security holes in the XYZ wireless SMP that allow outsiders to illegally access and obtain vulnerabilities in terms of WPA2 cracking, DoS, wireless router password cracking, and access point isolation so that it can be said that network security at SMP XYZ is still not safe
A Sensing Method of Network Security Situation Based on Markov Game Model
The sensing of network security situation (NSS) has become a hot issue. This paper first describes the basic principle of Markov model and then the necessary and sufficient conditions for the application of Markov game model. And finally, taking fuzzy comprehensive evaluation model as the theoretical basis, this paper analyzes the application fields of the sensing method of NSS with Markov game model from the aspects of network randomness, non-cooperative and dynamic evolution. Evaluation results show that the sensing method of NSS with Markov game model is best for financial field, followed by educational field. In addition, the model can also be used in the applicability evaluation of the sensing methods of different industries’ network security situation. Certainly, in different categories, and under the premise of different sensing methods of network security situation, the proportions of various influencing factors are different, and once the proportion is unreasonable, it will cause false calculation process and thus affect the results.
The Compound Prediction Analysis of Information Network Security Situation based on Support Vector Combined with BP Neural Network Learning Algorithm
In order to solve the problem of low security of data in network transmission and inaccurate prediction of future security situation, an improved neural network learning algorithm is proposed in this paper. The algorithm makes up for the shortcomings of the standard neural network learning algorithm, eliminates the redundant data by vector support, and realizes the effective clustering of information data. In addition, the improved neural network learning algorithm uses the order of data to optimize the "end" data in the standard neural network learning algorithm, so as to improve the accuracy and computational efficiency of network security situation prediction.MATLAB simulation results show that the data processing capacity of support vector combined BP neural network is consistent with the actual security situation data requirements, the consistency can reach 98%. the consistency of the security situation results can reach 99%, the composite prediction time of the whole security situation is less than 25s, the line segment slope change can reach 2.3% ,and the slope change range can reach 1.2%,, which is better than BP neural network algorithm.
Network intrusion detection using oversampling technique and machine learning algorithms
The expeditious growth of the World Wide Web and the rampant flow of network traffic have resulted in a continuous increase of network security threats. Cyber attackers seek to exploit vulnerabilities in network architecture to steal valuable information or disrupt computer resources. Network Intrusion Detection System (NIDS) is used to effectively detect various attacks, thus providing timely protection to network resources from these attacks. To implement NIDS, a stream of supervised and unsupervised machine learning approaches is applied to detect irregularities in network traffic and to address network security issues. Such NIDSs are trained using various datasets that include attack traces. However, due to the advancement in modern-day attacks, these systems are unable to detect the emerging threats. Therefore, NIDS needs to be trained and developed with a modern comprehensive dataset which contains contemporary common and attack activities. This paper presents a framework in which different machine learning classification schemes are employed to detect various types of network attack categories. Five machine learning algorithms: Random Forest, Decision Tree, Logistic Regression, K-Nearest Neighbors and Artificial Neural Networks, are used for attack detection. This study uses a dataset published by the University of New South Wales (UNSW-NB15), a relatively new dataset that contains a large amount of network traffic data with nine categories of network attacks. The results show that the classification models achieved the highest accuracy of 89.29% by applying the Random Forest algorithm. Further improvement in the accuracy of classification models is observed when Synthetic Minority Oversampling Technique (SMOTE) is applied to address the class imbalance problem. After applying the SMOTE, the Random Forest classifier showed an accuracy of 95.1% with 24 selected features from the Principal Component Analysis method.
Cyber Attacks Visualization and Prediction in Complex Multi-Stage Network
In network security, various protocols exist, but these cannot be said to be secure. Moreover, is not easy to train the end-users, and this process is time-consuming as well. It can be said this way, that it takes much time for an individual to become a good cybersecurity professional. Many hackers and illegal agents try to take advantage of the vulnerabilities through various incremental penetrations that can compromise the critical systems. The conventional tools available for this purpose are not enough to handle things as desired. Risks are always present, and with dynamically evolving networks, they are very likely to lead to serious incidents. This research work has proposed a model to visualize and predict cyber-attacks in complex, multilayered networks. The calculation will correspond to the cyber software vulnerabilities in the networks within the specific domain. All the available network security conditions and the possible places where an attacker can exploit the system are summarized.
Network Security Policy Automation
Network security policy automation enables enterprise security teams to keep pace with increasingly dynamic changes in on-premises and public/hybrid cloud environments. This chapter discusses the most common use cases for policy automation in the enterprise, and new automation methodologies to address them by taking the reader step-by-step through sample use cases. It also looks into how emerging automation solutions are using big data, artificial intelligence, and machine learning technologies to further accelerate network security policy automation and improve application and network security in the process.
Rule-Based Anomaly Detection Model with Stateful Correlation Enhancing Mobile Network Security
Research on network security technology of industrial control system.
The relationship between industrial control system and Internet is becoming closer and closer, and its network security has attracted much attention. Penetration testing is an active network intrusion detection technology, which plays an indispensable role in protecting the security of the system. This paper mainly introduces the principle of penetration testing, summarizes the current cutting-edge penetration testing technology, and looks forward to its development.
Detection and Prevention of Malicious Activities in Vulnerable Network Security Using Deep Learning
Export citation format, share document.

- Search by keyword
- Search by citation
Page 1 of 5
Polar code-based secure transmission with higher message rate combining channel entropy and computational entropy
The existing physical layer security schemes, which are based on the key generation model and the wire-tap channel model, achieve security by utilizing channel reciprocity entropy and noise entropy, respective...
- View Full Text
Dissecting zero trust: research landscape and its implementation in IoT
As a progressive security strategy, the zero trust model has attracted notable attention and importance within the realm of network security, especially in the context of the Internet of Things (IoT). This pap...
Study of smart grid cyber-security, examining architectures, communication networks, cyber-attacks, countermeasure techniques, and challenges
Smart Grid (SG) technology utilizes advanced network communication and monitoring technologies to manage and regulate electricity generation and transport. However, this increased reliance on technology and co...
A multi-agent adaptive deep learning framework for online intrusion detection
The network security analyzers use intrusion detection systems (IDSes) to distinguish malicious traffic from benign ones. The deep learning-based (DL-based) IDSes are proposed to auto-extract high-level featur...
Iterative and mixed-spaces image gradient inversion attack in federated learning
As a distributed learning paradigm, federated learning is supposed to protect data privacy without exchanging users’ local data. Even so, the gradient inversion attack , in which the adversary can reconstruct the ...
Winternitz stack protocols for embedded systems and IoT
This paper proposes and evaluates a new bipartite post-quantum digital signature protocol based on Winternitz chains and an oracle. Mutually mistrustful Alice and Bob are able to agree and sign a series of do...
Joint contrastive learning and belief rule base for named entity recognition in cybersecurity
Named Entity Recognition (NER) in cybersecurity is crucial for mining information during cybersecurity incidents. Current methods rely on pre-trained models for rich semantic text embeddings, but the challenge...
DTA: distribution transform-based attack for query-limited scenario
In generating adversarial examples, the conventional black-box attack methods rely on sufficient feedback from the to-be-attacked models by repeatedly querying until the attack is successful, which usually res...
A survey on lattice-based digital signature
Lattice-based digital signature has become one of the widely recognized post-quantum algorithms because of its simple algebraic operation, rich mathematical foundation and worst-case security, and also an impo...
Shorter ZK-SNARKs from square span programs over ideal lattices
Zero-knowledge succinct non-interactive arguments of knowledge (zk-SNARKs) are cryptographic protocols that offer efficient and privacy-preserving means of verifying NP language relations and have drawn consid...
Revocable and verifiable weighted attribute-based encryption with collaborative access for electronic health record in cloud
The encryption of user data is crucial when employing electronic health record services to guarantee the security of the data stored on cloud servers. Attribute-based encryption (ABE) scheme is considered a po...
Maxwell’s Demon in MLP-Mixer: towards transferable adversarial attacks
Models based on MLP-Mixer architecture are becoming popular, but they still suffer from adversarial examples. Although it has been shown that MLP-Mixer is more robust to adversarial attacks compared to convolu...
Practical solutions in fully homomorphic encryption: a survey analyzing existing acceleration methods
Fully homomorphic encryption (FHE) has experienced significant development and continuous breakthroughs in theory, enabling its widespread application in various fields, like outsourcing computation and secure...
A circuit area optimization of MK-3 S-box
In MILCOM 2015, Kelly et al. proposed the authentication encryption algorithm MK-3, which applied the 16-bit S-box. This paper aims to implement the 16-bit S-box with less circuit area. First, we classified th...
Intrusion detection system for controller area network
The rapid expansion of intra-vehicle networks has increased the number of threats to such networks. Most modern vehicles implement various physical and data-link layer technologies. Vehicles are becoming incre...
CT-GCN+: a high-performance cryptocurrency transaction graph convolutional model for phishing node classification
Due to the anonymous and contract transfer nature of blockchain cryptocurrencies, they are susceptible to fraudulent incidents such as phishing. This poses a threat to the property security of users and hinder...
Enhanced detection of obfuscated malware in memory dumps: a machine learning approach for advanced cybersecurity
In the realm of cybersecurity, the detection and analysis of obfuscated malware remain a critical challenge, especially in the context of memory dumps. This research paper presents a novel machine learning-bas...
BRITD: behavior rhythm insider threat detection with time awareness and user adaptation
Researchers usually detect insider threats by analyzing user behavior. The time information of user behavior is an important concern in internal threat detection.

F3l: an automated and secure function-level low-overhead labeled encrypted traffic dataset construction method for IM in Android
Fine-grained function-level encrypted traffic classification is an essential approach to maintaining network security. Machine learning and deep learning have become mainstream methods to analyze traffic, and ...
WAS: improved white-box cryptographic algorithm over AS iteration
The attacker in white-box model has full access to software implementation of a cryptographic algorithm and full control over its execution environment. In order to solve the issues of high storage cost and in...
Full-round impossible differential attack on shadow block cipher
Lightweight block ciphers are the essential encryption algorithm for devices with limited resources. Its goal is to ensure the security of data transmission through resource-constrained devices. Impossible dif...
Minimizing CNOT-count in quantum circuit of the extended Shor’s algorithm for ECDLP
The elliptic curve discrete logarithm problem (ECDLP) is a popular choice for cryptosystems due to its high level of security. However, with the advent of the extended Shor’s algorithm, there is concern that E...
Towards the transferable audio adversarial attack via ensemble methods
In recent years, deep learning (DL) models have achieved significant progress in many domains, such as autonomous driving, facial recognition, and speech recognition. However, the vulnerability of deep learnin...
LayerCFL: an efficient federated learning with layer-wised clustering
Federated Learning (FL) suffers from the Non-IID problem in practice, which poses a challenge for efficient and accurate model training. To address this challenge, prior research has introduced clustered FL (C...
A novel botnet attack detection for IoT networks based on communication graphs
Intrusion detection systems have been proposed for the detection of botnet attacks. Various types of centralized or distributed cloud-based machine learning and deep learning models have been suggested. Howeve...

Machine learning based fileless malware traffic classification using image visualization
In today’s interconnected world, network traffic is replete with adversarial attacks. As technology evolves, these attacks are also becoming increasingly sophisticated, making them even harder to detect. Fortu...
Research on privacy information retrieval model based on hybrid homomorphic encryption
The computational complexity of privacy information retrieval protocols is often linearly related to database size. When the database size is large, the efficiency of privacy information retrieval protocols is...
Performance evaluation of Cuckoo filters as an enhancement tool for password cracking
Cyberthreats continue their expansion, becoming more and more complex and varied. However, credentials and passwords are still a critical point in security. Password cracking can be a powerful tool to fight ag...
Tor network anonymity evaluation based on node anonymity
In order to address the shortcomings of traditional anonymity network anonymity evaluation methods, which only analyze from the perspective of the overall network and ignore the attributes of individual nodes,...
Verifiable delay functions and delay encryptions from hyperelliptic curves
Verifiable delay functions (VDFs) and delay encryptions (DEs) are two important primitives in decentralized systems, while existing constructions are mainly based on time-lock puzzles. A disparate framework ha...
MSLFuzzer: black-box fuzzing of SOHO router devices via message segment list inference
The popularity of small office and home office routers has brought convenience, but it also caused many security issues due to vulnerabilities. Black-box fuzzing through network protocols to discover vulnerabi...
A deep learning aided differential distinguisher improvement framework with more lightweight and universality
In CRYPTO 2019, Gohr opens up a new direction for cryptanalysis. He successfully applied deep learning to differential cryptanalysis against the NSA block cipher SPECK32/64, achieving higher accuracy than trad...
Attack based on data: a novel perspective to attack sensitive points directly
Adversarial attack for time-series classification model is widely explored and many attack methods are proposed. But there is not a method of attack based on the data itself. In this paper, we innovatively pro...
Improved lower bound for the complexity of unique shortest vector problem
Unique shortest vector problem (uSVP) plays an important role in lattice based cryptography. Many cryptographic schemes based their security on it. For the cofidence of those applications, it is essential to c...

Evolution of blockchain consensus algorithms: a review on the latest milestones of blockchain consensus algorithms
Blockchain technology has gained widespread adoption in recent years due to its ability to enable secure and transparent record-keeping and data transfer. A critical aspect of blockchain technology is the use ...
Graph neural network based approach to automatically assigning common weakness enumeration identifiers for vulnerabilities
Vulnerability reports are essential for improving software security since they record key information on vulnerabilities. In a report, CWE denotes the weakness of the vulnerability and thus helps quickly under...
EPASAD: ellipsoid decision boundary based Process-Aware Stealthy Attack Detector
Due to the importance of Critical Infrastructure (CI) in a nation’s economy, they have been lucrative targets for cyber attackers. These critical infrastructures are usually Cyber-Physical Systems such as powe...
Generic attacks on small-state stream cipher constructions in the multi-user setting
Small-state stream ciphers (SSCs), which violate the principle that the state size should exceed the key size by a factor of two, still demonstrate robust security properties while maintaining a lightweight de...
Evicting and filling attack for linking multiple network addresses of Bitcoin nodes
Bitcoin is a decentralized P2P cryptocurrency. It supports users to use pseudonyms instead of network addresses to send and receive transactions at the data layer, hiding users’ real network identities. Tradit...
Aparecium: understanding and detecting scam behaviors on Ethereum via biased random walk
Ethereum’s high attention, rich business, certain anonymity, and untraceability have attracted a group of attackers. Cybercrime on it has become increasingly rampant, among which scam behavior is convenient, c...
An efficient permutation approach for SbPN-based symmetric block ciphers
It is challenging to devise lightweight cryptographic primitives efficient in both hardware and software that can provide an optimum level of security to diverse Internet of Things applications running on low-...
IHVFL: a privacy-enhanced intention-hiding vertical federated learning framework for medical data
Vertical Federated Learning (VFL) has many applications in the field of smart healthcare with excellent performance. However, current VFL systems usually primarily focus on the privacy protection during model ...
Intrusion detection systems for wireless sensor networks using computational intelligence techniques
Network Intrusion Detection Systems (NIDS) are utilized to find hostile network connections. This can be accomplished by looking at traffic network activity, but it takes a lot of work. The NIDS heavily utiliz...
Detecting fake reviewers in heterogeneous networks of buyers and sellers: a collaborative training-based spammer group algorithm
It is not uncommon for malicious sellers to collude with fake reviewers (also called spammers) to write fake reviews for multiple products to either demote competitors or promote their products’ reputations, f...
Continuously non-malleable codes from block ciphers in split-state model
Non-malleable code is an encoding scheme that is useful in situations where traditional error correction or detection is impossible to achieve. It ensures with high probability that decoded message is either c...
Use of subword tokenization for domain generation algorithm classification
Domain name generation algorithm (DGA) classification is an essential but challenging problem. Both feature-extracting machine learning (ML) methods and deep learning (DL) models such as convolutional neural n...
A buffer overflow detection and defense method based on RISC-V instruction set extension
Buffer overflow poses a serious threat to the memory security of modern operating systems. It overwrites the contents of other memory areas by breaking through the buffer capacity limit, destroys the system ex...

Quantized autoencoder (QAE) intrusion detection system for anomaly detection in resource-constrained IoT devices using RT-IoT2022 dataset
In recent years, many researchers focused on unsupervised learning for network anomaly detection in edge devices to identify attacks. The deployment of the unsupervised autoencoder model is computationally exp...
Detecting compromised email accounts via login behavior characterization
The illegal use of compromised email accounts by adversaries can have severe consequences for enterprises and society. Detecting compromised email accounts is more challenging than in the social network field,...
Security estimation of LWE via BKW algorithms
The Learning With Errors (LWE) problem is widely used in lattice-based cryptography, which is the most promising post-quantum cryptography direction. There are a variety of LWE-solving methods, which can be cl...
- Editorial Board
- Sign up for article alerts and news from this journal
Affiliated with

The Institute of Information Engineering (IIE) is a national research institute in Beijing that specializes in comprehensive research on theories and applications related to information technology.
IIE strives to be a leading global academic institution by creating first-class research platforms and attracting top researchers. It also seeks to become an important national strategic power in the field of information technology.
IIE’s mission is to promote China’s innovation and industrial competitiveness by advancing information science, standards, and technology in ways that enhance economic security and public safety as well as improve our quality of life.
Read more..
The journal is indexed by
- EI Compendex
- Emerging Sources Citation Index
- EBSCO Discovery Service
- Institute of Scientific and Technical Information of China
- Google Scholar
- Norwegian Register for Scientific Journals and Series
- OCLC WorldCat Discovery Service
- ProQuest-ExLibris Primo
- ProQuest-ExLibris Summon
- TD Net Discovery Service
- UGC-CARE List (India)

Annual Journal Metrics
2022 Citation Impact 3.1 - 2-year Impact Factor 4.8 - 5-year Impact Factor 2.071 - SNIP (Source Normalized Impact per Paper) 1.266 - SJR (SCImago Journal Rank)
2023 Speed 8 days submission to first editorial decision for all manuscripts (Median) 95 days submission to accept (Median)
2023 Usage 408,523 downloads 15 Altmetric mentions
- ISSN: 2523-3246 (electronic)
You are using an outdated browser. Please upgrade your browser .
T4Tutorials.com
Network security research topics for ms phd, network security research topic ideas for ms, or ph.d. degree.
I am sharing with you some of the research topics regarding Network Security that you can choose for your research proposal for the thesis work of MS, or Ph.D. Degree.
- CompTIA security+ guide to network security fundamentals
- A survey of moving target defenses for network security
- Modeling network security: Case study of email system
- Programmable In-Network Security for Context-aware {BYOD} Policies
- Composite metrics for network security analysis
- Network security analysis using big data technology and improved neural network
- CPT‐TODIM method for bipolar fuzzy multi‐attribute group decision making and its application to network security service provider selection
- Optical network security management: requirements, architecture, and efficient machine learning models for detection of evolving threats
- Classifying anomalies for network security
- Cloud integrated IoT enabled sensor network security: research issues and solutions
- Bio-Inspired Network Security for 5G-Enabled IoT Applications
- Computer Network Security and Preventive Measures in the Age of Big Data
- Scalable Game-Focused Learning of Adversary Models: Data-to-Decisions in Network Security Games.
- Challenges and Novel Solutions for 5G Network Security, Privacy and Trust
- A Review in Recent Development of Network Threats and Security Measures
- Patterns and Interactions in Network Security
- A Study of Network Security Situational Awareness in Internet of Things
- Data-driven network layer security detection model and simulation for the Internet of Things based on an artificial immune system
- Quantification of distribution network security with high penetration of distributed generators
- NSAPs: A novel scheme for network security state assessment and attack prediction
- Network security and privacy evaluation scheme for cyber physical systems (CPS)
- What to Make of the Huawei Debate? 5G Network Security and Technology Dependency in Europe
- An efficient method for network security situation assessment
- Application of information communication network security management and control based on big data technology
- Augmenting smart home network security using blockchain technology
- Sdn/nfv-based security service function tree for cloud
- Multiple pattern matching for network security applications: Acceleration through vectorization
- Machine Learning, Image Processing, Network Security and Data Sciences: Second International Conference, MIND 2020, Silchar, India, July 30-31, 2020 …
- Network intrusion detection combined hybrid sampling with deep hierarchical network
- An Assessment of Practical Hands-On Lab Activities in Network Security Management
- Cyber Deception for Computer and Network Security: Survey and Challenges
- Computer Network System Security Management and Maintenance Strategy
- Deep Learning for Security Problems in 5G Heterogeneous Networks
- Reference architecture of the telecom network security protection system for cloud network convergence
- Fortified Network Security Perception: A Decentralized Multiagent Coordination Perspective
- Network security prediction model using neural networks
- Machine learning enhanced network security
- Prediction of network security based on DS evidence theory
- Quantitative Evaluation Model of Network Security Situation Based on DS Evidence Theory
- Computer Network Security Based on GABP Neural Network Algorithm
- Decision Support for Mission-Centric Network Security Management
- Strategy of Enterprise Network Security Protection Based on Cloud Computing
- A systematic comparison of mobile Ad-hoc network security attacks
- Research on the Quantitative Assessment and Security Measures of Hierarchical Network Security Threat Situation
- Computer network security countermeasures based on big data
- Network Security-Security Methods in Transnational Corporations (TNC)
- Application of Computer Information Management Technology in Network Security
- Research on network security protection technology of energy industry based on blockchain
- A Comprehensive Study on Machine Learning Algorithms for Wireless Sensor Network Security
- Security Technology of Wireless Sensor Network Based on IPSEC
- Research on Computer Network Security Analysis Modeling Based on Artificial Intelligence Technology
- Network security situation prediction based on grey relational analysis and support vector machine Algorithm
- HMMs based masquerade detection for network security on with parallel computing
- Analysis of Computer Network Security Threat Defense Measures under the Environment of Internet of Things
- Composite Metrics for Network Security Analysis
- Exploiting Channel Distortion for Transmitter Identification for In-Vehicle Network Security
- Network Security Policy for Higher Education Institutions based on ISO Standards
- Implementation of Machine Learning in Network Security
- Research on Computer Network Security Problems and Protective Measures under the Background of Big Data
- Discussion on the Countermeasures of Network Security in Computer Application
- 5G Network Security for IoT Implementation: A Systematic Literature Review
- Research on Enterprise Computer Network Security Protection Technology Based on Information Technology
- Long Term Evolution Network Security and Real-Time Data Extraction
- Computer Network Security Hazards and Preventive Strategies
- Research on Wireless Sensor Network Security Location Based on Received Signal Strength Indicator Sybil Attack
- Research on Industrial Control Network Security Data Acquisition System
- Network Security Issues of Data Link Layer: An Overview
- Multi-source and multi-dimensional network security situational awareness model
- Security Analysis of Public Security Terminal Network and Its Peripheral Equipment
- A novel security model for cooperative virtual networks in the IoT era
- Comprehensive fault simulation method in active distribution network with the consideration of cyber security
- Research on Network Security Trend Prediction Based on Exponential Smoothing Algorithm
- Security monitoring and network management for the power control network
- A Research Journey of Full-Duplex at University of California from Self-Interference Cancellation to Wireless Network Security
- Identifying the Best Network Security Using EDAS
- Improving architectures for automating network security using specification-based protocols
- A Logical Controller Architecture for Network Security
- Network security situation analysis based on a dynamic Bayesian network and phase space reconstruction
- Investigating the Filter Capacity of Linecouplers in KNX regarding network security
- of Network Security: An End-to-End Panorama
- CRYPTOGRAPHY TECHNOLOGY WITH NETWORK SECURITY
- Improving Network Security through Collaborative Sharing
- Information network security construction based on depth learning and modulus algorithm
- Communications and Network Security
- Construction of network security job service model based on rough set data analysis algorithm
- Principles of Adaptive Corporate Network Security Management
- Improvement of network security with the help of security key (Yubikey)
- Reform of Network Security Technology Practice Teaching System Based on Virtual Simulation Training Platform
- Analysis and Evaluation on the Network Security Defense in Power Marketing Industrial Control System
- REAL-TIME TRAFFIC DETECTION AND ANALYSIS OF NETWORK SECURITY INTRUSION ATTACK: SNORT INTRUSION PREVENTION SYSTEM
- Research on Computer Network Security Vulnerabilities and Preventive Measures Based on Multi-Platform
- DEMILITARIZED ZONE AND PORT KNOCKING METHODS FOR COMPUTER NETWORK SECURITY
- Research on Ad Hoc Network Security Risk Assessment Method
- Research on Network Optimization and Network Security in Power Wireless Private Network
- Research on Network Security Active Defense System Oriented to Electric Power Monitoring System
- Development of trusted network and challenges it faces
- Design of College Network Security Management System Based on SNMP Management Model
- High-Performance and Range-Supported Packet Classification Algorithm for Network Security Systems in SDN
- ULTRA-HIGH-SPEED NETWORK SECURITY APPLICATIONS
- Network Security Intelligence Centres for Information Security Incident Management
- Study on Experimental Teaching Virtual Simulation for Network Security and Law Enforcement Major
- Real-time Network Intrusion Detection System with Supporting Cyber Security Regulations for Nuclear Power Plants
- An Analytical Framework for Evaluation of Reliability and Security in Advanced Network Systems
- A Review on Security and Privacy Issues and Challenges in Internet of Things
- Research on the Security Strategy and Technology of Information Resource Network of Chinese Academy Library
- Smart Pillboxes with Network Security
- Network Security using Notable Cryptographic Algorithm for IoT Data
- Security, Controllability, Manageability and Survivability in Trustworthy Network
- A Remote Access Security Model based on Vulnerability Management
- Computer and Network Security
- Network Security Situation Prediction in Software Defined Networking Data Plane
- A Data Fusion Framework of Multi-Source Heterogeneous Network Security Situational Awareness Based on Attack Pattern
- Software-Defined Network Security over OpenStack Clouds: A Systematic Analysis.
- Research on the Application of Deep Learning in Computer Network Information Security
- Research on the game of network security attack‐defense confrontation through the optimal defense strategy
- Leveraging Virtual Labs for Personalised Group-based Assessment in a Postgraduate Network Security and Penetration Testing Module
- On the Improvement of the Stipulation of the Crime of Refusing to Fulfill the Obligation of Information Network Security Management
- The Exploration and Research of the Network Security Offense and Defense Laboratory Cooperated by Schools and Enterprises under the Background of New …
- Network Layer Security Detection Model of Internet of Things Based on Immune System
- Security Analysis of Wireless Local Area Network (WLAN) Network with the Penetration Testing Method
- Network Security Enabled Arduino Devices for Military Communication
- Research on Information Security Monitoring and Early Warning Mechanism of Internet Application Network Based on Particle Swarm Optimization
- Key Technology Analysis of Malicious Code Emergency Response in Computer Communication Network Security
- Network Security Cryptographic Protocols and Lattice Problems
- Network Security Situation Prediction based on Combining 3D-CNNs and Bi-GRUs.
- Intelligent detection system of asset security vulnerability hidden danger under multiple and heterogeneous Web network
- Construction of Compound DDOS Network Security System Based on PKI and CA Authentication
- Construction and Research of Comprehensive Management Platform for Network Security of China University Information System
- A Quantitative Study: Using the Latin Square Design Model in the Prioritization of Network Security Threats
- Topological Data Analysis for Evaluation of Network Security Data
- Quadratic Poly Certificateless Inductive Signcryption for Network Security
- Research on Network Information Security Issues and Strategies under the Internet Plus Environment
- A Review paper on Network Security and Cryptography
- Research Productivity of Publications towards IoT in Network Security
- Application of target tracking and abnormal target detection algorithm in power network security
- A New Experiment Teaching Mode for Network Security & Law Enforcement Major to Meet the Need of New Engineering Talent Training
- Analysis of Information Security Protection of Power System Computer Network
- A Conceptual Model for the Implementation of Cyber Security Measures in a Process Control Network Environment
- Network security defense model based on firewall and IPS
- Encryption and Decryption for Network Security Using Reverse Context-Free Grammar Productions
- Wireless Sensor Network Security for Smart Home IoT Systems
- Security in SDN: A comprehensive survey
- Zero Trust Network Security Model in containerized environments
- Research on Situation Awareness of Universities’ Network Information Security in the Big Data Environment
- Applying network analysis to explore the global scientific literature on food security
- ” 5G network security”.
- Study on the Training Mode of Network Security Practical Talent in Vocational and Technical College Based on Gamification and Leveling up
- Exploring Network Security Using Vigenere Multiplicative Cipher Encryption and Implementation
- Adversarial detection games in network security applications with imperfect and incomplete information
- Learning to upgrade internet information security and protection strategy in big data era
- Computer Network Information Security and Protection Strategy
- Information Encryption Algorithm in Power Network Communication Security Model
- Research on Campus Network Security Problem and Protection Strategy
- Anonymization of Event Logs for Network Security Monitoring
- Self-corrected coefficient smoothing method based network security situation prediction
- CS 646-102: Network Protocols Security (Revised for Remote Learning)
- Special issue on security and privacy in network computing
- Security region of natural gas network in electricity-gas integrated energy system
- Forecasting Security Alerts Based on Time Series
- A composable security treatment of the lightning network
- Cloud Security Issues &Network Security in Private Cloud
- 5G carrier network data collection and security management evolution ideas
- UNSW-NB15 Computer Security Dataset: Analysis through Visualization
- 5G network slicing: a security overview
- New Security Management Scheme for Software-Defined-Networks
- In-vehicle network intrusion detection using deep convolutional neural network
- Security for mobile edge cloud
- Critical infrastructure under attack: lessons from a honeypot
- The Development of Artificial Intelligence Technology And Its Application in Communication Security
- Moving Target Defense to set Network Slicing Security as a KPI
- Computer Security Vulnerabilities and Preventive Measures
- Security-aware virtual network embedding algorithm based on reinforcement learning
- A cloud-fog-edge closed-loop feedback security risk prediction method
- A Matter of Life and Death: Analyzing the Security of Healthcare Networks
- Security Risk Analysis based on Data Criticality
- Security and privacy in vehicular ad hoc network and vehicle cloud computing: a survey
- Powerless Security
- Security design and application of Internet of things based on asymmetric encryption algorithm and neural network for COVID-19
- Research on intelligent cyber security protection for electric power dispatching and control system
- Machine learning threatens 5G security
- Technological Tools for Data Security in the Treatment of Data Reliability in Big Data Environments
- Blockchain-Enabled Distributed Security Framework for Next-Generation IoT: An Edge Cloud and Software-Defined Network-Integrated Approach
- Real-time task scheduling and network device security for complex embedded systems based on deep learning networks
- Management Innovation of Network Society Based on Big Data
- Who’s that knocking at the door? The problem of credential abuse
- Consumer IoT: Security vulnerability case studies and solutions
- New Security System Development Universally Applicable and Enforceable
- The state‐of‐the‐art in container technologies: Application, orchestration and security
- Network slicing in 5G and the security concerns
- Research on Computer Security Protection Technology Based on Information
- Research of Security Routing Protocol for UAV Communication Network Based on AODV
- Deep learning for cyber security intrusion detection: Approaches, datasets, and comparative study
- Hybrid analysis of android apps for security vetting using deep learning
- Mobility enabled security for optimizing IoT based intelligent applications
- Providing Information Security on the Base of Artificial Immune System for Industrial Internet of Things
- A Survey of The Design and Security Mechanisms of The Wireless Networks and Mobile Ad-Hoc Networks
- An enhanced anonymity resilience security protocol for vehicular ad-hoc network with scyther simulation
- LSWBVM: A lightweight security without using batch verification method scheme for a vehicle ad hoc network
- The limitations in the state-of-the-art counter-measures against the security threats in H-IoT
- Deepopf: A deep neural network approach for security-constrained dc optimal power flow
- Security and privacy challenges in 5G-enabled vehicular networks
- A Zero Trust Network Research Based on Overlay Technology
- 6g white paper: Research challenges for trust, security and privacy
- Blockchains, Cryptocurrency, and Smart Contracts Technology: Security Considerations
- Security information transmission algorithms for IoT based on cloud computing
- The four biggest malware threats to UK businesses
- Are your IT staff ready for the pandemic-driven insider threat?
- Smart security audit: Reinforcement learning with a deep neural network approximator
- Analysis and Research of Enterprise Information System Security Based on e-Commerce
- NETWORK SECURITY & INTERKONEKSI JARINGAN DENGAN L2TP+ IPSEC
- Anomaly Detection for Network Flow Using Immune Network and Density Peak.
- Routing, Wavelength and Time-Slot Assignment Approaches with Security Level in QKD-Enabled Optical Networks
- An intelligent cross layer security based fuzzy trust calculation mechanism (CLS-FTCM) for securing wireless sensor network (WSN)
- A review on IoT security architecture: attacks, protocols, trust management issues, and elliptic curve cryptography
- New Model and Application of Security Region for Metering Device Status Estimation
- Cyber-Physical Security of Powertrain Systems in Modern Electric Vehicles: Vulnerabilities, Challenges and Future Visions
- Accounting Informationization in Computer Network Environment
- TUGAS RESUME SEMINAR ACHIEVING A QUANTUM LEAP IN NETWORK SECURITY
- Research on Security Protection Technology Based on Terminal Information Jump
- Through the lens of code granularity: A unified approach to security policy enforcement
- Discussion and Analysis of Computer Information Data Security and Encryption Technology
- ZSM security: Threat surface and best practices
- Optimal network defense strategy selection based on Bayesian game
- Architecture of Security Protection technology for Aviation Cyberspace
- Selection of intermediate routes for secure data communication systems using graph theory application and grey wolf optimisation algorithm in MANETs
- Hybrid intrusion detection system using machine learning
- Cyber-security on smart grid: Threats and potential solutions
- Information Security Applications
- Comparative analysis of ML classifiers for network intrusion detection
- A Network Traffic Classification Method Based on Hierarchical Clustering
- Security architecture for defining and enforcing security profiles in dlt/sdn-based iot systems
- Exploring the Storj Network: a Security Analysis
- Designing a cyber-security culture assessment survey targeting critical infrastructures during covid-19 crisis
- Security and trust in blockchains: Architecture, key technologies, and open issues
- Efficient signal and protocol level security for network communication
- Intrudtree: a machine learning based cyber security intrusion detection model
- Self-aware networks that optimize security, QoS, and energy
- Network Traffic Control Using AI
- Predicting the adoption of a mobile government security response system from the user’s perspective: An application of the artificial neural network approach
- A Hybrid Framework for Security in Cloud Computing Based on Different Algorithms
- Modeling the impact of network connectivity on consensus security of Proof-of-Work blockchain
- Software-defined network (SDN) data plane security: issues, solutions, and future directions
- Intelligent security and optimization in Edge/Fog Computing
- 5G network slicing with QKD and quantum-safe security
- Safety Situation Assessment of Underwater Nodes Based on BP Neural Network
- Security and Privacy Concerns in Wireless Networks-A Survey
- Federating Tactical Edge Networks: Ways to Improve Connectivity, Security, and Network Efficiency in Tactical Heterogeneous Networks
- Critical analysis of security and privacy challenges for the Internet of drones: a survey
- Towards a Security Enhanced Virtualised Network Infrastructure for Internet of Medical Things (IoMT)
- Robust detection for network intrusion of industrial IoT based on multi-CNN fusion
- Smart city-based e-commerce security technology with improvement of SET network protocol
- Security issues in cloud computing
- New Ways of Implementing Cyber Security to Help in Protecting America
- Spacechain: a three-dimensional blockchain architecture for IoT security
- Effective attack detection in internet of medical things smart environment using a deep belief neural network
- Innovation and risk walk hand-in-hand with 5G and IoT
- A Comprehensive Mechanism of MANET Network Layer Based Security Attack Prevention
- Managing endpoints, the weakest link in the security chain
- Power system reserve scheduling with wind farm integration considering robust security constraints
- IoT Security: Simulation and Analysis of TCP SYN Flooded DDOS Attack using WireShark
- Machine learning based solutions for security of Internet of Things (IoT): A survey
- An efficient Lightweight integrated Blockchain (ELIB) model for IoT security and privacy
- Targeted cyber attacks: how to mitigate the increasing risk
- Data Security Risk and Preventive Measures of Virtual Cloud Server Based on Cloud Computing
- Attacks and Security Measures in Wireless Sensor Network
- The Exploration of the Training Mode in the Major of Information Security in University
- Towards {HTTPS} Everywhere on Android: We Are Not There Yet
- Comprehensive analysis of MQTT 5.0 susceptibility to network covert channels
- Analysing and forecasting the security in supply-demand management of Chinese forestry enterprises by linear weighted method and artificial neural network
- Image transformation network for privacy-preserving deep neural networks and its security evaluation
- TLS-level security for low power industrial IoT network infrastructures
- A comprehensive report on security and privacy challenges in Software as a Service
- Big data analytics in cyber security: Network traffic and attacks
- Security of HyperLogLog (HLL) cardinality estimation: Vulnerabilities and protection
- Security Clustering Algorithm Based on Integrated Trust Value for Unmanned Aerial Vehicles Network
- Solving the security problem of intelligent transportation system with deep learning
- Analysis of security and energy efficiency for shortest route discovery in low‐energy adaptive clustering hierarchy protocol using Levenberg‐Marquardt neural network …
- Topological analysis of bitcoin’s lightning network
- Modeling network architecture: a cloud case study
- Security architectures in wireless sensor network
- Physical layer security of a two way relay based mixed FSO/RF network in the presence of multiple eavesdroppers
- Research on Model of Assessing Security Situation for Industrial IoT
- Physical Layer Security for UAV Communications
- Methods and Techniques for Dynamic Deployability of Software-Defined Security Services
- Security Analysis of Two Unbalancing Pairing-free Identity-based Authenticated Key Exchange Protocols
- Research on Ideological and Political Education of College Students Based on Network Information Security
- Security and privacy challenges in vehicular ad hoc networks
- Security of RPL based 6LoWPAN Networks in the Internet of Things: A Review
- ATTDC: An active and trace-able trust data collection scheme for industrial security in smart cities
- TD²SecIoT: Temporal, Data-Driven and Dynamic Network Layer Based Security Architecture for Industrial IoT.
- A review of machine learning approaches to power system security and stability
- Review on the security threats of internet of things
- Internet of Things: A Secure Cloud-Based MANET Mobility Model
- Research on the technology of artificial intelligence in computer network under the background of big data
- IoT security: Advances in authentication
- Open source and security: why transparency now equals strength
- Exploration on the Diversified Cultivation of Cyber Space Security Talent in Higher Vocational Colleges under the Background of the Fusion of Production and …
- Deep recurrent neural network for IoT intrusion detection system
- Social network analysis and mining: privacy and security on Twitter
- An efficient XGBoost–DNN-based classification model for network intrusion detection system
- Modified zone based intrusion detection system for security enhancement in mobile ad hoc networks
- How data can be the lingua franca for security and IT
- A comprehensive survey: Benefits, services, recent works, challenges, security, and use cases for sdn-vanet
- Securing of Unmanned Aerial Systems (UAS) against security threats using human immune system
- TNSR security networking software: Basic configuration of a security solution
- A support system for civil aviation navigation equipment security management
- Unmanned Systems Security: Models, Challenges, and Future Directions
- Study of artificial neural networks in information security risk assessment
- Identifying and mitigating security risks for secure and robust NGI networks
- Wireless Sensor Network in Agriculture: Model of Cyber Security
- Automated Deployment of a Security Operations Center
- Deep Q-Network for Enhanced Data Privacy and Security of IoT Traffic
- 12th International Symposium on Foundations and Practice of Security, Toulouse, 05/11/19-07/11/19
- Security challenges of Internet of Underwater Things: A systematic literature review
- Methodology for complex security
- Security and channel noise management in cognitive radio networks
- Review of Physical Layer Security Technology in Battlefield Network
- Survey on the internet of vehicles: Network architectures and applications
- iOS, Your {OS}, Everybody’s {OS}: Vetting and Analyzing Network Services of iOS Applications
- Demystifying internet of things security: successful iot device/edge and platform security deployment
- Research on Index System Construction and Assessment Methods of Distribution Network CPS Security Against Cyber Attack
- Stochastic two-stage reliability-based Security Constrained Unit Commitment in smart grid environment
- Integrating complex event processing and machine learning: An intelligent architecture for detecting IoT security attacks
- Optimising storage processes to reduce the risk of ransomware
- An ANP-GRA-based evaluation model for security features of IoT systems
- SDARP: Security based Data Aware Routing Protocol for ad hoc sensor networks
- Convolutional neural network-based feature extraction using multimodal for high security application
- Security offloading network system for expanded security coverage in IPv6-based resource constrained data service networks
- Security-Aware Carrier Network Planning
- Addressing security and privacy issues of IoT using blockchain technology
- Ensuring security framework for WBANs
- Network information theoretic security
- Improving CAN bus security by assigning dynamic arbitration IDs
- A Canvass of 5G Network Slicing: Architecture and Security Concern
- Operational technology security–a data perspective
- Towards security-Aware 5G slice embedding
- Review of security challenges in healthcare internet of things
- Mobile Payment Security in the Context of Big Data: Certificateless Public Key Cryptography
- Practical Security for Cooperative Ad Hoc Systems
- Improving the Security and Reliability of Embedded Networks With TTMAC-CAN
- A Voice Signal Interpreter using Machine Learning Techniques
- The 2020 Data Breach Investigations Report–a CSO’s perspective
- Security and Privacy for Mobile Edge Caching: Challenges and Solutions
- On Development of a Game‐Theoretic Model for Deception‐Based Security
- Advanced malicious beaconing detection through AI
- What does ‘secure by design’actually mean?
- Advanced metering infrastructures: security risks and mitigation
- Sdn-based vanets, security attacks, applications, and challenges
- On the Security of a Practical Constant-Size Ring Signature Scheme.
- DecChain: A decentralized security approach in Edge Computing based on Blockchain
- Evaluating the performance of the OSCORE security protocol in constrained IoT environments
- LoRaWAN protocol: specifications, security, and capabilities
- Security Approaches in Machine Learning for Satellite Communication
- Keyloggers: silent cyber security weapons
- Security of Cryptocurrencies in blockchain technology: State-of-art, challenges and future prospects
- INSPIRE-5Gplus: Intelligent security and pervasive trust for 5G and beyond networks
- The future of blockchain technology in healthcare internet of things security
- Security and privacy in 6G networks: New areas and new challenges
- Security and Privacy of Lightning Network Payments with Uncertain Channel Balances
- Security and Communication Network Automatic Analysis Architecture of IoT Malware Samples
- Optimized image processing and clustering to mitigate security threats in mobile ad hoc network.
- A survey on boosting IoT security and privacy through blockchain
- Construction of Innovation and Entrepreneurship Training System for Network Information Security Talents
- Secure Socket Layer (SSL) in the Network and Web Security
- ANALYZING AND EVALUATING THE SECURITY STANDARDS IN WIRELESS NETWORK: A REVIEW STUDY
- Discussion on the Application of 5G Network UAV in Public Security of Smart Cities
- Security Architecture and Protocols for Secure MQTT-SN
- Internet of Things (IoT) enabling technologies, requirements, and security challenges
- Sustainable Infrastructure Monitoring for Security-Oriented Purposes
- Modbus Protocol Based on the Characteristics of the Transmission of Industrial Data Packet Forgery Tampering and Industrial Security Products Testing
- HELAD: A novel network anomaly detection model based on heterogeneous ensemble learning
- Research on term extraction technology in computer field based on wireless network technology
- A Proposed Approach for Wireless Sensor Networks Security
- Network and System Security
- Sports and health big data system based on 5G network and Internet of Things system
- Cloud Computing Security Challenges and Threats
- A Security Protection Method for In-Vehicle Millimeter Wave Radar Network Based on Digital Watermarking Technology
- A security policy model transformation and verification approach for software defined networking
- Data presentation in security operations centres: exploring the potential for sonification to enhance existing practice
- BAT: deep learning methods on network intrusion detection using NSL-KDD dataset
- Secure data storage and recovery in industrial blockchain network environments
- Internet of Things: Evolution and technologies from a security perspective
- Bot mitigation–how gapsin understanding and ownership are exposingbusinesses to greater threats
- Truck platoon security: State-of-the-art and road ahead
- Expansion of {ICS} testbed for security validation based on {MITRE} atT&Ck techniques
- Research and implementation of information security for intelligent distribution network
- Enhancing medical data security via combining elliptic curve cryptography and image steganography
- Security analysis of an automobile controller area network bus
- Towards blockchain-based software-defined networking: security challenges and solutions
- Security Analysis of Hybrid Multi-Carrier Energy Systems
- IoT-KEEPER: Detecting malicious IoT network activity using online traffic analysis at the edge
- Source-Grid-Load Combined Security Assessment of PV-Penetrated Distribution Network
- Fast key-frame image retrieval of intelligent city security video based on deep feature coding in high concurrent network environment
- Enhancing the Robustness and Security Against Various Attacks in a Scale: Free Network
- 5G network-based Internet of Things for demand response in smart grid: A survey on application potential
- Security/stability-based Pareto optimal solution for distribution networks planning implementing NSGAII/FDMT
- POSTER: A Survey of Security Challenges with 5G-IoT
- Computer Network Information Security in the Big Data Era
- Blockchain technology in the future of business cyber security and accounting
- A secure fuzzy extractor based biometric key authentication scheme for body sensor network in Internet of Medical Things
- Identifying the attack surface for IoT network
- Cyber security threats and vulnerabilities: a systematic mapping study
- Security and privacy in social networks: data and structural anonymity
- Nozomi Networks: OT/IoT Security Report
- Analysis of wireless sensor network multi-sensor data fusion security method
- Overview of the mobility related security challenges in LPWANs
- Behavioral and game-theoretic security investments in interdependent systems modeled by attack graphs
- Security provision for vehicular fog computing
- Towards a reliable comparison and evaluation of network intrusion detection systems based on machine learning approaches
- Deep reinforcement learning approach for autonomous vehicle systems for maintaining security and safety using LSTM-GAN
- Security Issues in Fog Environment: A Systematic Literature Review
- A taxonomy of network threats and the effect of current datasets on intrusion detection systems
- Overview and prospect of 5G security
- Ensuring information security as an ideological problem
- A Review on the Security of the Internet of Things: Challenges and Solutions
- Ddosnet: A deep-learning model for detecting network attacks
- Security implications of underlying network technologies on industrial internet of things
- SecONet: A Security Framework for a Photonic Network-on-Chip
- Towards an Insightful Computer Security Seminar
- Bitcoin and blockchain: Security and privacy
- Multidomain security authentication for the Internet of things
- Computer Network Information Security Protection Based on Virtual Private Network
- Addressing cyber security skills: the spectrum, not the silo
- Data Security in Mobile Cloud Computing: A State of the Art Review.
- Security of Wi-Fi as a Key Factor for IoT
- Blockchain technology, improvement suggestions, security challenges on smart grid and its application in healthcare for sustainable development
- What Email Servers Can Tell to Johnny: An Empirical Study of Provider-to-Provider Email Security
- On the security of networked control systems in smart vehicle and its adaptive cruise control
- Smart city development in Taiwan: From the perspective of the information security policy
- Conditional Privacy-Preserving Anonymous Authentication Scheme With Forward Security in Vehicle-to-Grid Networks
- Adhering to privacy by design with identity-as-a-service
- Intelligence, security, and vehicular sensor networks in internet of things (IoT)-enabled smart-cities: An overview
- A survey of DDoS attacking techniques and defence mechanisms in the IoT network
- Overcoming the Security Shortcomings Between Open vSwitch and Network
- Software-Defined Network (SDN) Architecture and Security Considerations for 5G Communications
- Significant Role of Security in IOT Development and IOT Architecture
- Design of a Security Service Orchestration Framework for NFV
- Distb-sdoindustry: Enhancing security in industry 4.0 services based on distributed blockchain through software defined networking-iot enabled architecture
- A Lightweight Internet Sharing Scheme for Sectional Medical Images according to Existing Hospital Network Facilities and Basic Information Security Rules
- Orchestrating SDN Control Plane towards Enhanced IoT Security
- Secure D2D communication for 5G IoT network based on lightweight cryptography
- Security on Blockchain Technology
- Research on security situation assessment algorithm under virtual technology of cloud platform
- A survey on security challenges in cloud computing: issues, threats, and solutions
- An efficient approach for enhancing security in Internet of Things using the optimum authentication key
- Technology Architecture of Smart Grid Information Security Defense System
- Design and implementation of automated IoT security testbed
- DMASK-BAN: Improving the security of body area networks
- A Deep Learning Approach for Detecting Security Attacks on Blockchain.
- Network slicing: Recent advances, taxonomy, requirements, and open research challenges
- Security monitoring of heterogeneous networks for big data based on distributed association algorithm
- When wireless security meets machine learning: Motivation, challenges, and research directions
- Salsa20 based lightweight security scheme for smart meter communication in smart grid
- Security Analysis of Power System Network Based on Complex Network
- A blockchain-enabled deduplicatable data auditing mechanism for network storage services
- A Mobile Crowdsensing Data Security Delivery Model Based on Tangle Network
- Research on Information Security Evaluation Based on Artificial Neural Network
- A study on a security model for the establishment of a non-face-to-face smart work working environment in a physical network separation environment of public …
- Borders of Digital Network Freedom in Public Security Space
- Multilevel Security Framework for NFV Based on Software Defined Perimeter
- Security in low-power wide-area networks: state-of-the-art and development toward the 5G
- Artificial intelligence models in power system analysis
- Random linear network coding based physical layer security for relay-aided device-to-device communication
- Dynamic patterns of terrorist networks: Efficiency and security in the evolution of eleven islamic extremist attack networks
- Comments on “Dropping Activation Outputs with Localized First-Layer Deep Network for Enhancing User Privacy and Data Security”
- Security Method for Internet of Things Using Machine Learning Against Cyber Attacks
- A Study on Wireless Network Management for Security Enhancement
- Convolutional Neural Network Based Sound Recognition Methods for Detecting Presence of Amateur Drones in Unauthorized Zones
- The Security Issues in IoT-Cloud: A Review
- Data Security System for A Bank Based on Two Different Asymmetric Algorithms Cryptography
- Keeping a secure hold on data through modern electronic content management
- Trustworthy image security via involving binary and chaotic gravitational searching within PRNG selections
- Security Concerns during Photo Sharing in Social Network Platforms
- Security schemes based conditional privacy-preserving in vehicular ad hoc networks
- Security Vulnerabilities, Attacks, Threats and the Proposed Countermeasures for the Internet of Things Applications
- Roadmap Toward a Network Infrastructure for Public Safety and Security
- Bluetooth Low Energy Mesh Networks: Survey of Communication and Security Protocols
- A survey on security and privacy issues in edge computing-assisted internet of things
- Energy efficient protocol in wireless sensor network: optimized cluster head selection model
- Security in wireless sensor networks: Issues and challenges
- Computer network simulation with ns-3: A systematic literature review
- Stable Multi-agent Clustering Method to Improve the Security in VANET
- Research on Data Security of Wireless Body Area Network
- Plaintext-related image encryption algorithm based on perceptron-like network
- CS 646-852: Network Protocols Security
- AI-driven zero touch network and service management in 5G and beyond: Challenges and research directions
- Technique for Information Security Based on Controls Established by the SysAdmin Audit, Networking and Security Institute
- Integrating Smartphone Network Architecture and Data Security Techniques to Mitigate Sharp Practices in Non-Profit Organizations
- A study of ensemble methods for cyber security
- Security problems of 5G voice communication
- Security and privacy issues in fog computing for healthcare 4.0
- Applying Smart Security Model to Protect Client Services From the Threats of the Optical Network
- A crowdsourcing method for online social networks security assessment based on human-centric computing
- Security mechanism building for big data based on Trusted Computing
- A stacking ensemble for network intrusion detection using heterogeneous datasets
- Security in a mobile learning environment
- Using the security triad to assess blockchain technology in public sector applications
- Cognitive Radio Network-Based Design and Security Challenges in 5G Communication
- A real-time and ubiquitous network attack detection based on deep belief network and support vector machine
- Entity identification and security solutions in IoT based on PKI and Blockchain technology
- SEPAD–Security Evaluation Platform for Autonomous Driving
- Security of Distributed Machine Learning
- Key business drivers for IoT development and security principles
- LD2FA-PSO: A novel Learning Dynamic Deterministic Finite Automata with PSO algorithm for secured energy efficient routing in Wireless Sensor Network
- A dynamic event-triggered approach to observer-based PID security control subject to deception attacks
- Physical Layer Security for in-Body Wireless Cardiac Sensor Network
- Physical layer security for massive access in cellular Internet of Things
- A Clustering TDMA and Code Block Binding Algorithms to Enhance the Node Energy and Security of the Network
- Critical risk considerations in auto-ID security: Barcode vs. RFID
- SCADA (Supervisory Control and Data Acquisition) systems: Vulnerability assessment and security recommendations
- The IoT security gap: a look down into the valley between threat models and their implementation
- IGAN-IDS: An imbalanced generative adversarial network towards intrusion detection system in ad-hoc networks
- Analyzing the Effects of Ad Hoc Security in MANET with AODV
- Towards the Impact of Security Vunnerabilities in Software Design: A Complex Network-Based Approach
- On the placement of security-related Virtualised Network Functions over data center networks
- Security Issues and Challenges in Cloud Computing-Review
- A Bayesian learning based scheme for online dynamic security assessment and preventive control
- Security threats and countermeasures in software defined network using efficient and secure trusted routing mechanism
- Security issues in IoT and their countermeasures in smart city applications
- Offline witness encryption with semi-adaptive security
- An Overview on Cyber Security Paradigms
- Security Risks and Challenges in IoT-Based Applications
- Adaptive data and verified message disjoint security routing for gathering big data in energy harvesting networks
- Internet of things architecture and security challenges
- Network Power: China’s efford to reshape Asia’s Regional Security Architecture
- Cyber-physical systems security education through hands-on lab exercises
- A Security Concept Based on Scaler Distribution of a Novel Intrusion Detection Device for Wireless Sensor Networks in a Smart Environment
- Testbeds, attacks, and dataset generation for big data cluster: A system application for big data platform security analysis
- Improving Internet of Things (IoT) security with software-defined networking (SDN)
- Evolving deep learning architectures for network intrusion detection using a double PSO metaheuristic
- Riskio: A serious game for cyber security awareness and education
- Cyber Security Risk Analysis and Protection Structure Design for Power Distribution IoT
- Security, privacy and trust of different layers in Internet-of-Things (IoTs) framework
- Hardware Security of the Controller Area Network (CAN Bus)
- The Risk of Facebook Social Media Network on Social Security
- Artificial Intelligence Techniques for Information Security in 5G IoT Environments
- Security and Performance Evaluation of Master Node Protocol in the Bitcoin Peer-to-Peer Network
- How Can IoT Services Pose New Security Threats In Operational Cellular Networks?
- Bio-inspired security analysis for IoT scenarios
- Information Security of Power Plants
- Security and the smart city: A systematic review
- Security Access Solution of Cloud Services for Trusted Mobile Terminals Based on TrustZone.
- Security challenges over cloud environment from service provider prospective
- Development of testbed for cyber-manufacturing security issues
- Image Processing and Post-Data Mining Processing for Security in Industrial Applications: Security in Industry
- Effectiveness of SCADA System Security Used Within Critical Infrastructure
- Statistical in-depth security analysis for Vehicle to everything communication over 5g network
- Security Properties of Light Clients on the Ethereum Blockchain
- Application Research of “Edge-Cloud Collaboration” Architecture in Security Protection of Ubiquitous Power Internet of Things
- IoT Security Using Deception–Measuring Improved Risk Posture
- A systematic literature review of blockchain cyber security
- A Review on Security and Privacy of Internet of Medical Things
- A Security Enhanced 5G Authentication Scheme for Insecure Channel
- Security Attacks In MANET–A Comprehensive Study
- Understanding security in the government’s use of blockchain technology with value focused thinking approach
- A survey of network virtualization techniques for internet of things using sdn and nfv
- A security Assessment of Distribution Network CPS Based on Association Matrix Modeling Analysis
- A methodology for security classification applied to smart grid infrastructures
- Design and Implementation of Full-Scale Industrial Control System Test Bed for Assessing Cyber-Security Defenses
- Improving information security risk analysis by including threat-occurrence predictive models
- Security-enhanced OFDM-PON with two-level coordinated encryption strategy at the bit-level and symbol-level
- Cyber ranges and security testbeds: Scenarios, functions, tools and architecture
- Towards fuzzy anomaly detection-based security: a comprehensive review
- Security issues and challenges in V2X: A Survey
- A multi-stage anomaly detection scheme for augmenting the security in IoT-enabled applications
- … network modeling to estimate upscaled parameters for the Topopah Spring, lava flow, and Tiva Canyon Aquifers at Pahute Mesa, Nevada National Security …
- Regulation and Security Modelling of Essential Services in Network of Information Systems
- Survey on IoT: Security Threats and Applications
- Deep learning and big data technologies for IoT security
- A Concept for Establishing a Security Operations and Training Centre at the Bulgarian Naval Academy
- Analysis of the Information Security Risk Assessment Mechanism Based on the Power System
- Security, cybercrime and digital forensics for IoT
- A Systematic Survey on Software-Defined Networks, Routing Protocols and Security Infrastructure for Underwater Wireless Sensor Networks (UWSNs)
- Feature Selection for Deep Neural Networks in Cyber Security Applications
- Design and implementation of a security system based on ADSL access technology
- Improved Security Particle Swarm Optimization (PSO) Algorithm to Detect Radio Jamming Attacks in Mobile Networks
- Security Threats in 5G Edge Computing Environments
- A Research Paper on Social Engineering and Growing Challenges in Cyber Security
- Has the global expansion of energy markets truly improved energy security?
- Study on Stochastic Differential Game Model in Network Attack and Defense
- Security overhead of random linear network coding in multicast relay networks
- Development of security mechanisms for a remote sensing system based on opportunistic and mesh networks
- Ethereum smart contract security research: survey and future research opportunities
- Cyber-physical security and resiliency analysis testbed for critical microgrids with ieee 2030.5
- Research on Application of Internet of Things Information Security Using Blockchain Technology
- Virtualization Construction of Security Components of Edge IoT Agent Based on Security Requirements
- Assessment of Security Issues in Banking Sector of Libya
- The Technique of Implementation Security into Clinical Internet of Things
- Enlisting human resources to mitigate information security risks
- Understanding the MANET Security Using Various Algorithms and Types
- On the Application of Computer Archives Management System and the Path of Security Maintenance
- Vehicle communication network in intelligent transportation system based on internet of things
- Design and modeling an Adaptive Neuro-Fuzzy Inference System (ANFIS) for the prediction of a security index in VANET
- Analysis of Segregated Witness Implementation for Increasing Efficiency and Security of the Bitcoin Cryptocurrency
- Improved lightweight security approach routing protocol in internet of things
- Understanding the role of incentives in security behavior
- A Sharding Scheme based Many-objective Optimization Algorithm for Enhancing Security in Blockchain-enabled Industrial Internet of Things
- Co-design of dual security control and communication for nonlinear CPS under DoS attack
- Physical layer security in vehicular networks with reconfigurable intelligent surfaces
- SECURING OF THE AD HOC NETWORK BY USING SECURITY PROTOCOL FOR RELIABLE DATA DELIVERY
- A survey on the security of blockchain systems
- Fast image encryption algorithm with high security level using the Bülban chaotic map
- Security Fundamentals for E-Commerce
- A Security Trust Mechanism for Data Collection with Mobile Vehicles in Smart City
- Randomly Elected Blockchain System based on Grouping Verifiers for Efficiency and Security
- 5G vehicular network resource management for improving radio access through machine learning
- Five Years of Cyber Security Education Reform in China
- Maintenance and Security System for PLC Railway LED Sign Communication Infrastructure
- Privacy and security issues in the future: A social media
- Mix Networks: Existing Scenarios and Future Directions on Security and Privacy
- SDN Based Security in Mobile Ad hoc Networks
- On safeguarding privacy and security in the framework of federated learning
- Security in cognitive radio network: defense against primary user emulation attacks using genetic artificial bee colony (GABC) algorithm
- Security and privacy for green IoT-based agriculture: Review, blockchain solutions, and challenges
- 6G: Opening new horizons for integration of comfort, security, and intelligence
- Topology-free optimal power dispatch for distribution network considering security constraints and flexible building thermal inertia
- MARGINAL PROBABILITIES OF PERSONAL DATA SECURITY AND USER INTERACTION IN THE SOCIAL NETWORK
- Region model and application of regional integrated energy system security analysis
- Performance of the Transport Layer Security Handshake Over 6TiSCH
- The role of computer security management in preventing financial technology risks
- SECURITY RISK ASSESSMENT OF TURKEY’S ROAD NETWORK
- Critical success factors to create 5G networks in the smart cities of India from the security and privacy perspectives
- Comparative analysis of a new VSC‐optimal power flow formulation for power system security planning
- A comprehensive insight into game theory in relevance to cyber security
- An experimental analysis of security vulnerabilities in industrial IoT devices
- Enhancing SCADA System Security Via Spiking Neural Network
- Cyber security awareness, knowledge and behavior: a comparative study
- A security‐driven network architecture for routing in industrial Internet of Things
- Scope and Limitations of Ethical Hacking and Information Security
- ANALYSIS OF SECURITY FOR CLOUD COMPUTING
- An anomaly detection framework for cyber-security data
- Cyber-Physical Systems Security Introductory Course for STEM Students
- A Research of Distributed Security and QoS Testing Framework
- Using deep learning to solve computer security challenges: a survey
- A comprehensive survey on attacks, security issues and blockchain solutions for IoT and IIoT
- Independent Co-Assurance using the Safety-Security Assurance Framework (SSAF): A Bayesian Belief Network Implementation for IEC 61508 and Common …
- Towards 5G-based IoT security analysis against Vo5G eavesdropping
- Context-Aware Autonomous Security Assertion for Industrial IoT
- Combination of D-AHP and Grey Theory for the Assessment of the Information Security Risks of Smart Grids
- Security architecture for cloud-based command and control system in IoT environment
- Convergence of blockchain and artificial intelligence in IoT network for the sustainable smart city
- Cyber-physical systems security: Limitations, issues and future trends
- Security Control Mechanism for Safety Critical Functions Operating on Automotive Controller Area Network
- A novel security protocol for wireless sensor networks with cooperative communication
- Towards a new thermal monitoring based framework for embedded CPS device security
- Improvised Guard for Next Level Security Automated Vehicle Security system using Artificial intelligence and Convolutional Neural Network
- The Development of Method for Evaluation of Information Security Threats in Critical Systems
- Scalability, Consistency, Reliability and Security in SDN Controllers: A Survey of Diverse SDN Controllers
- Security, Privacy Research issues in Various Computing Platforms: A Survey and the Road Ahead.
- Analysis of energy security level in the Baltic States based on indicator approach
- Bobtail: improved blockchain security with low-variance mining
- Moving from blocker to enabler: cloud security and the modern CISO
- Work-in-Progress: Compromising Security of Real-time Ethernet Devices by means of Selective Queue Saturation Attack
- Robust Transmission Network Expansion Planning with Nk Security Criterion and Uncertainty Factors
- DATA, INFORMATION AND IT SECURITY-SOFTWARE SUPPORT FOR SECURITY ACTIVITIES
- The method of Internet of Things access and network communication based on MQTT
- An Intrusion Detection Model for Wireless Sensor Network Based on Information Gain Ratio and Bagging Algorithm.
- A survey on smart agriculture: Development modes, technologies, and security and privacy challenges
- A decentralized scalable security framework for end‐to‐end authentication of future IoT communication
- E-COMMERCE: TRUSTED THIRD PARTY SECURITY MODELS
- Security Challenges in Software Engineering for the Cloud: A Systematic Review
- Packet analysis for network forensics: A comprehensive survey
- Security Information Sharing in Smart Grids: Persisting Security Audits to the Blockchain
- Automation of information security audit in the Information System on the example of a standard “CIS Palo Alto 8 Firewall Benchmark”
- Empirical Use of Network Time Protocol in Internet of Things Devices: Vulnerabilities and Security Measures
- A Survey on Security Mechanisms in IoT
- A survey on internet of things: Applications, recent issues, attacks, and security mechanisms
- A Survey on Wireless Security protocols (WEP, WPA and WPA2)
- Cyber security analysis on a production environment featuring software defined networks.
- Pathways toward a decarbonized future—Impact on security of supply and system stability in a sustainable German energy system
- OREA for improving data packet transmission in wireless sensor networks with cloud security mechanism
- New Frontiers in IoT: Networking, Systems, Reliability, and Security Challenges
- AFLNet: a greybox fuzzer for network protocols
- SADM-SDNC: security anomaly detection and mitigation in software-defined networking using C-support vector classification
- Security of IoT application layer protocols: Challenges and findings
- Access control method using electrocardiogram signal for fog computing security
- Introduction to IoT security
- UDP-Based Active Scan for IoT Security (UAIS).
- ENTERPRISE INFORMATION SECURITY MANAGEMENT SYSTEM BASED ON THE MODERN OBFUSCATION TECHNIQUE FOR MOBILE NETWORK OPERATORS
- Security Concepts Based on IEEE 802.1 X for G. hn Broadband PLC Access Networks
- A Model on IoT Security Method and Protocols for IoT Security Layers
- Mapping Obfuscation-Based PHY Security Scheme for Resource-Constrained Wireless Sensor Network
- A Mode Study on the Integration of Computer Network Technology and College English Curriculum
- MuLViS: multi-level encryption based security system for surveillance videos
- Overview on the Security in 5G Phase 2
- Security of power line communication systems: issues, limitations and existing solutions
- Security Issues in Internet of Things (IoT): A Comprehensive Review
- Does internet security matter for foreign direct investment? A spatial econometric analysis
- A Hybrid Security System for Unmanned Aerial Vehicles
- Security and Performance in IoT: A Balancing Act
- A new network forensic framework based on deep learning for Internet of Things networks: A particle deep framework
- A comprehensive model of information security factors for decision-makers
- A Blockchain-based security model for SDNs
- Computer Security-ESORICS 2020: 25th European Symposium on Research in Computer Security, ESORICS 2020, Guildford, UK, September 14-18, 2020 …
- A taxonomy of Sybil attacks in vehicular ad-hoc network (VANET)
- Research progress on big data security technology
- Network-Mediated Knowledge Spillovers in ICT/Information Security January 2020 Neil Gandal Nadav Kunievsky
- Security of communication in the special communications systems
- Secrecy transmission capacity in mobile ad hoc networks with security-aware Aloha protocol
- A survey of IoT security based on a layered architecture of sensing and data analysis
- On the Assessment of Information Security Ensuring Models of Critical Information Infrastructure Facilities
- A lightweight security scheme for advanced metering infrastructures in smart grid
- Vulnerability Analysis and Security Research of Docker Container
- Security and privacy issues in fog computing
- TBM: A trust-based monitoring security scheme to improve the service authentication in the Internet of Things communications
Research Topics Computer Science
Topic Covered
Top 10 research topics of Network Security | list of research topics of Network Security | trending research topics of Network Security | research topics for dissertation in Network Security | dissertation topics of Network Security in pdf | dissertation topics in Network Security | research area of interest Network Security | example of research paper topics in Network Security | top 10 research thesis topics of Network Security | list of research thesis topics of Network Security| trending research thesis topics of Network Security | research thesis topics for dissertation in Network Security | thesis topics of Network Security in pdf | thesis topics in Network Security | examples of thesis topics of Network Security | PhD research topics examples of Network Security | PhD research topics in Network Security | PhD research topics in computer science | PhD research topics in software engineering | PhD research topics in information technology | Masters (MS) research topics in computer science | Masters (MS) research topics in software engineering | Masters (MS) research topics in information technology | Masters (MS) thesis topics in Network Security.
Related Posts:
- Software Security Research Topics Ideas [MS PhD]
- Network Security topics for presentation
- How to maintain software security and application security
- Network Security MCQs
- Top Selling Famous Recommended Books of Network Security
- List of Journals on Network Security
Burp Scanner
Burp Suite's web vulnerability scanner

Product comparison
What's the difference between Pro and Enterprise Edition?

Download the latest version of Burp Suite.

How I choose a security research topic

James Kettle
Director of Research
Published: 14 June 2023 at 13:09 UTC
Updated: 14 June 2023 at 13:16 UTC

How do you choose what topic to research? That’s the single most common question I get asked, probably because selecting a topic is such a daunting prospect. In this post, I’ll take a personal look at how I select topics for security research. As a case study, I’ll use my latest research, which will be presented at Black Hat USA and DEF CON this August:
Smashing the State Machine: the True Potential of Web Race Conditions
The hardest part
Before we start, I should mention that I firmly believe that choosing a topic is not the hardest part of web security research.
I’ve spoken to so many people who have cool ideas but never attempt to execute them. On the rare occasion that someone does mention a research idea that I think is doomed from the outset, it’s clear that attempting it will still provide them with a major learning experience - hardly a terrible outcome.
In fact, I don’t think that coming up with research ideas is the hard part either. Once you start researching, you’ll likely find every topic you explore leaves you with ideas for three more projects.
I think the hardest part of research is knowing when to bail, and when to push on.
Fast failure
My primary criteria when I evaluate a topic is how much time I’ll need to invest before I have enough information to decide whether to abandon it or continue. Knowing when to abandon a topic and when to push on is an extremely valuable skill for research, and it’s worth putting thought into this before starting.
This year, the attack-concept I wanted to explore initially looked like it required a major up-front time investment. However, I identified a short-cut - if I could build a test website that was vulnerable and reasonably realistic, that would prove the concept was pursuing. I built the website, quickly discovered that the attack concept was extremely unrealistic, and quickly pivoted to a different concept.
The second concept showed just enough promise to make me waste six weeks on it before it flopped too. When looking for a third concept, race conditions was an attractive topic because I already had powerful tooling from the prior project. This meant it would only take about a day to adapt the tooling, and a week or two of manual testing to see if I could discover something significant in the wild. I found a novel high-impact vulnerability in under a week, which cemented my commitment to the topic.
The fear factor
I like to research topics I’m scared of. Fear is a great indicator of something I don’t fully understand, and challenges that I don’t know how to tackle. Race conditions provided this in buckets, and I place this up-front and center in my abstract:
For too long, web race-condition attacks have focused on a tiny handful of scenarios. Their true potential has been masked thanks to tricky workflows, missing tooling, and simple network jitter hiding all but the most trivial, obvious examples. In this session, I’ll introduce multiple new classes of race condition that go far beyond the limit-overrun exploits you’re probably already familiar with... [read full abstract]
Direct impact vs audience impact
As a security professional, it’s tempting to rate a research project’s impact based on the direct impact. For example, over the years I’ve seen a range of serious flaws in a certain popular CDN, and I suspect that if I directly targeted it, I could find multiple ways to take over all their customers’ websites - a reasonable chunk of the web. In terms of direct impact, this would be pretty good.
But when you submit to Black Hat, they ask you to specify ‘three actionable take-aways’ for the audience. How would my hypothetical CDN-popping talk answer this? The only action required would be from that sole CDN vendor - in effect I’d just be giving a war-story talk. These can be entertaining and inspiring, but that’s not what I’m aiming for.
I try to pick a topic where the audience will take away novel attack techniques, and any tools or methodology required to make them practical to apply.
Applicable audience
Over the last five years, my research has been focused on HTTP Request Smuggling and Web Cache Poisoning . Since I’m well-versed in this topic, doing further research directly on top has become relatively easy, and I’m perpetually aware of multiple promising ideas.
However, while creating the presentation for last year’s Browser-Powered Desync Attacks , I became acutely aware that it demanded an exceptional amount of prior technical knowledge from the audience.
Building on a little recent research often works well because you can summarise it yourself. However, building on a large volume of recent research means that anyone in the audience who isn’t already familiar is going to struggle, and overall less people will get the benefit.
This year, by focusing on race conditions - a topic with minimal recent developments - I’ve been able to start building on a foundation that most attendees will be familiar with. Relative to last year’s talk, you can expect this talk to have both greater potential for the experts, and greater accessibility for the masses.
Existing skill-sets vs personal development
There’s a second, more personal reason why I changed my research focus away from request smuggling. I expect request smuggling to keep yielding good research for years to come, but just like any topic, at some point it’ll dry up. If I maintain my exclusive focus on this topic, there’s a risk I’ll become over-specialised and end up in a bad place when the topic stops yielding fruit.
I deliberately choose race conditions to avoid this over-specialisation risk, even though I regarded it as a much riskier bet than doing even more request smuggling exploration. Personal development is a huge and easily overlooked part of research. I rarely repeat my presentations across months for the same reason - if you spend your time sharing the same presentation over and over, you’re sacrificing novel research time.
That said, there’s a balance to be had here - if you have specialist knowledge, that will give you an edge on certain topics. Race conditions appealed from the start because I’d observed low-level HTTP quirks that could enhance these attacks, and I’d also observed them in the wild when trying to exploit response queue poisoning.
No topic is perfect; this presentation has fewer case studies than usual for me because fully automated detection of these vulnerabilities is not practical. On the plus side, this leaves a large number of vulnerabilities on the table that the audience can find simply by applying the methodology.
Ultimately, I see over-thinking topic choice as a pitfall. Save your energy for the research itself - you’ll need it! If you found this useful, you might also like So you want to be a web security researcher , and the presentation Hunting Evasive Vulnerabilities .
If you’re got any thoughts or queries, feel free to ping me on Twitter or LinkedIn . Hopefully I’ll see some of you in-person at the presentation too!
Back to all articles
Related Research
Making desync attacks easy with trace, using form hijacking to bypass csp, hiding payloads in java source code strings.
Present and Future of Network Security Monitoring
Ieee account.
- Change Username/Password
- Update Address
Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.
You are using an outdated browser. Please upgrade your browser to improve your experience.
Security at Berkeley
The Security Group in the EECS Department at the University of California, Berkeley studies a wide variety of topics, including cryptography, network security, usable security, and secure machine learning.
To learn more about our research, we encourage you to visit the pages of our faculty and students, linked below.
We've got great people!
Formidable faculty.
- Alessandro Chiesa
- Natacha Crooks
- Anthony Joseph
- Vern Paxson
- Raluca Ada Popa
- David Wagner
Affable affiliates
- Serge Egelman
- Nicholas Weaver
Percipient postdocs & stellar staff
- Ioannis (Yannis) Demertzis
- Evgenios Kornaropoulos
- Katerina Sotiraki
- Sameer Wagh
- Primal Wijesekera
Gracious grad students
- Noura Alomar
- Eleanor Cawthon
- Emma Dauterman
- Vivian Fang
- Conor Gilsenan
- Julien Piet
- Deevashwer Rathee
- Mayank Rathee
- Nikita Samarin
- Chawin Sitawarin
- Eric Wallace
- Jean-Luc Watson
- Tiancheng Xie
Amazing alumni
- Devdatta Akhawe
- Jethro Beekman
- John Bethencourt
- Nikita Borisov
- Nicholas Carlini
- Weikeng Chen
- Xinyun Chen
- Monica Chew
- Chia Yuan Cho
- Arel Cordero
- Weidong Cui
- Thurston Dang
- Rachna Dhamija
- Adrienne Porter Felt
- David Fifield
- Matthew Finifter
- Ian Goldberg
- Dan Hendrycks
- Sakshi Jain
- Steve Hanna
- Mobin Javed
- Noah Johnson
- Rob Johnson
- Alex Kantchelian
- Chris Karlof
- Nathan Malkin
- Bill Marczak
- Michael McCoyd
- Adrian Mettler
- Brad Miller
- Mitar Milutinovic
- Pratyush Mishra
- David Molnar
- Austin Murdock
- Blaine Nelson
- Paul Pearce
- Adrian Perrig
- Rishabh Poddar
- Rebecca Portnoff
- Justin Samuel
- Naveen Sastry
- Prateek Saxena
- Ben Schwarz
- Umesh Shankar
- Richard Shin
- Jeongseok Son
- Emil Stefanov
- Cynthia Sturton
- Kurt Thomas
- Chris Thompson
- Matthias Vallentin
- Jason Waddle
- Joel Weinberger
- Alma Whitten
- Ka-Ping Yee
- Jiaheng Zhang
- Wenting Zheng
- Vijay D'Silva
- Maritza Johnson
- Lorenzo Martignoni
- Ivan Martinovic
- Stephen McCamant
- Bodo Möller
- Prateek Mittal
- Mathias Payer
- William Robertson
Adored admins
- Angie Abbatecola
- Lena Lau Stewart
We have lots of friends!
Security research at Berkeley spans a number of labs, centers, departments, colleges, and schools. You may also want to learn about (in no particular order):
- The cryptography research group
- RISELab (Real-time Intelligent Secure Explainable)
- Center for Evidence-based Security Research
- The Networking and Security Group at ICSI
- Berkeley Laboratory for Usable and Experimental Security (BLUES) and the Usable Security and Privacy Group at ICSI
- The Center for Long-Term Cybersecurity
- The School of Information and its Master's of Information and Cybersecurity
We host events!
- Security Seminar
- Security Reading Group
- The CLTC's seminar series
We teach courses!
Undergraduate.
- CS 161: Computer Security - s21 , f20 , s20 , f19 , s19 , f18 , s18 , f17 , s17 , f16 , s16 , s15 , s14 , s13 , s11 , s10 , f08 , f05
- CS 171: Undergraduate Cryptography - s21 , f19 , s19
- CS 194-138: Penetration Testing ("Cyberwar") - f17
- CS 261: Computer Security - s21 , f18 , f17 , f15 , f12 , s11 , f11 , f09 , f08 , f07 , f04 , f02 , f00 , f98
- CS 261N: Internet/Network Security - s20 , f16 , s15 , s14 , f12 , s12 , f10 , f09 , s09 , s08
- CS 276: Cryptography - f20 , f18 , f17 , f16 , f15 , f14 , s09 , s06 , s04 , s02
- CS 294-163: Decentralized Security: Theory and Systems - f19
- CS 294-155: Law and Cryptography - f19
- CS 294-156: Advanced Topics on Secure Hardware - f18
- CS 294-144/151: Blockchain and Cryptoeconomics - s19 , f18 , s18
- CS 294: Advanced Cryptography - s20 , f18 , s18
- CS 294: Secure Computation - s16
- CS 294-101: Cutting-edge Web Technologies - s15
- CS 294-105: Empirical Analysis - f14
- CS 294-65: Privacy Technologies: From Theory to Practice - s11
- CS 294: Advanced Topics in Computer Security - s10
- CS 294-24: Privacy and Security Enhancing Technologies - f07
- CS 294: Lattices, Learning with Errors and Post-Quantum Cryptography - s20
- INFO 290-001 Cybersecurity in Context - f19
For the most up-to-date list of courses, and to see what's being offered next semester, see the EECS course directory .
We'd love for you to join us!
If you would like to join Berkeley's EECS Department as a graduate student, please apply to our Ph.D. program . Many Berkeley undergraduates assist in our research; if you're interested in doing research, contact our faculty members directly. We also frequently host visiting students and professors.
Network Security Projects
The term ‘ Network security ’ provides the security for the computer services such as software and hardware and the communication devices like network infrastructure, and basic communication protocols of the network. It desires to attain data security on the network in an organization or in between the user individuals. If you are looking to implement interesting network security projects reach our network team specialist to guide your research work.
“Network security is one of the most important cyber security branches. Comparing to the wired systems, the wireless network like Wi-Fi and internet-linked wireless networks or devices having the most probability for attacks.”
The network security particularly protects the data on the flow. Network security preserves a high level of demand in the cyber security field . As the users’ need for fast internet is considered to be one of the main reasons for network security threats and it has become very common. So network security projects are in the order of the day.
“This article mainly focuses on the Network Security concepts and tools that can be implanted by the Network Security models and to stimulate your interests on proposing Network security projects.”
Let’s have a look at the process involved in Network Security that involves the following processes on detecting three leading and common attacks
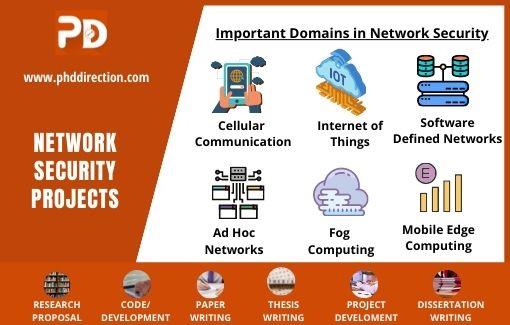
Process of Network Security
- Detecting phishing threats and harmful URL
- Detecting application attacks
- Detecting spoofing, scanning, and other network intrusions
The network security can be applied into two major ways of endpoint security and use cases authentication of malware, ransomware, and spyware detection and it detects the brute force attacks and unauthorized access as follows
- Detecting affected devices and suspicious entry
- Analyses User activities
- Detecting spyware and ransomware
- Categories malware detection
Network security models are functioning based on detecting malicious software or viruses and patching the affected devices. In the technology world, network security threats are unavoidable and the impact of such threats may extend up to affecting the organization’s monetary assets . The preventing and mitigating actions may vary according to the attacking phases used by the adversary . The attacking steps of the attacker are listed below
List of Attacking Steps
- Tracks erasing
- Control & command
- Exfiltration of data
- Internal recon
- Access expansion
- Data collection
- External recon and
- Manipulation
To mitigate the above malicious attacks performed by an adversary over the network, building security models are one of the best ways to save the network from such threats . To construct an effective security model, you must keep in mind the following features of an effective model.
- Prevention or Mitigation Techniques : the model must prevent the attack’s influence over the business resources in an organization
- Analysis Techniques: the model must use the analysis mechanism of an attack used by the detection method
- Detection Techniques: to detect the anomaly and suspicious activity, and the model must have the current and past historical data.
- Location detection: the model must have the capacity to detect the perimeter and zone of the attacked location.
- Attack Features: the model should have the detecting features for attacks analysis
- Attack Methods: the model has to identify the method of attack per segment.
The security models are used to detect, identify, and counteract the attack by identifying the method of attack and its location for effective patching and it must be updated with new techniques to identify and react according to the level of the threat. Here are the four main network security concepts identified by our engineers that could be performed by the above-mentioned models.
Top 4 Network Security Concepts
- Managing Network Device : due to the displaying of many weak points in the firmware, network device management involves repairing such issues
- Network Monitoring: if any suspicious pattern is sent to manipulate the network, this process involves the action of observation and assessment
- Network Protocol Design : it is used to prevent the attacker from snorting your packet, by sending an encrypted network packet on network interface cards and network devices.
- Designing network security architecture: for in-depth network security measures, this obliging concept is used often.
The above four network security components are considered to be the best in the field of network security . There are other major concepts too, which are professionally used by many research sectors. Scholars who chose to pick the network security projects are set apart to have better scopes in the relevant field and here our research team has come up with the research issues as listed below.
Latest Network Security Projects Research Topics
- Network steganography
- Privacy-friendly communication services and architectures
- Interconnecting system security
- Network interoperability
- Fault-tolerant models
- Distributed computations security
- Techniques of distributed consent
- Security simulation and analysis of distributed systems
- Analyzing network attack propagation
- Mitigation techniques of network layer attacks
- Distributed computing security: protocols and frameworks
- Network security essentials
- Technical aspects, management, and procedures of a secured network
- Vertical Handover Simulation
- Security over distributed systems
- Principles and protocols of network security
- Technologies and algorithms of network security
The above mentioned issues are exposed to research in the field of network security. If you feel those issues would be taken by someone then you, here we help you to find the areas that attract you for research and we guide you by providing innovative network security project topics . Here is the list of major research areas.
- Volunteer Computing in Big Data
- Technical aspects, management, and procedures of a secured network
Latest Network Security Project Topics
- Designing MIMO telecommunication system
- Social media sharing based on blockchain trust
- Using ML and AI to detect fake news in social media
- The technology of new authentication and biometric for access control, identity management, and device authentication
- Cyber-physical-social spaced user privacy protection mainly on online social networks and mobile devices
- Techniques of Intrusion Tolerance in IoT
- Lightweight cryptography for energy efficiency and balance security
Along with our suggestion in the latest research topics in network security that are based on the contemporary mechanism to secure a network, our world-class research developers know to predict the future project trends in network security . As the network threats are on the rise by now, the above-given list is based on securing the network by identifying the threats . But the future network security will be based on the game theory; the evaluating functions of security database and the précised zero-knowledge concurrency.
Future trends in network Security
- Analyzing cryptographic protocols by using Game Theory
- Succeeding enhanced equilibria by Cryptographic protocols
- Analyzing symbolism and concurrency
- Secured theorems for analyzing symbolic security
- Encrypted data evaluating functions
- Recovering private data
- Zero-knowledge sets
- Database privacy definitions
- Zero-knowledge concurrency
- Flexible Cryptography
- Non-Black-box Simulation
- Accurate Zero knowledge
In this article, we mainly focus on network security and there are some measures for analyzing the quality features given by the network security model to provide the fundamental assurance over its capacities in the following.
What are the Quality Attributes for Network Security?
- Ensure privacy
- Interoperability
- Mitigation ability
- Adaptability
- Reliability
- QoS Parameters
- QoE Parameters
- Scalability
The quality based on the basic functions of the model includes the ability of its measure, availability, ease of access, adapting the new mechanisms , etc. they are the characteristic of the network security models . Here are the countermeasures to improve the quality of the models after or before every attack

- QoS Parameters and QoE
The quality based on the basic functions of the model includes the ability of its measure, availability, ease of access, adapting the new mechanisms , etc. they are the characteristic of the network security models . Here are the countermeasures to improve the quality of the models after or before every attack .
How do we secure the network against cyber-attacks?
- Correlation and matching attribution
- Detecting anomaly
- Clustering scenario
- Matching model
- Statistical inference
- Consequences and prerequisites
- Based on structure
- Mixed approaches
In addition to the above methods to secure the network from cyber-attacks the process of detection is the most important step both in identifying the attack and detecting the right counteractions . The IDS are called the Intrusion Detection of a model and its functions are various as we listed below
Detection methods
- Detection based on Flow (Grouping traffic, Deep Learning, Feature Engineering)
- Detection based on Packet (Parsing Packet, Payload analysis)
- Detection based on the session (Statistical, sequence Feature)
- Detection based on log (rule-based system combination, Feature engineering, Text analysis)
- Statistical model
- Machine learning
- Time series
- Machine of finite-state
- Expert system
- Matching the pattern
Before the detection of the attack, a model would function to collect the traffic, selecting the feature of its functions because a network model must have the capacity over its mentioned fundamental working process,
Working process of a network model
- Traffic collection
- Feature Selection
- SVM, ANN, NB, DT, USML
- Evolution Measures
A network security model must meet certain requirements for accurate and precision modeling.
- Advanced Persistent Threats (APT) detection
- Real-time responding
- Large data warehouses Management
- Unstructured Data Analytics
- A large amount of data recollection
The working process of a network model concentrates on its functions over data collection that depends on the various types and functions. While those functions are prone to attack, we could identify the effect of the threat through IDS with our existing data. When we run out of data on the system malfunctions, anomaly detection is used to identify the threats by its following approaches.
Detecting Network Anomaly
- Statistical Approaches
- The flow of statistical data
- Analyzing Wavelet
- Hidden Markov Model
- Analyzing Covariance matrix
- Bayesian networks
- Hybrid clustering
- Reinforcement learning
- Deep learning
As discussed above, the scope of network security projects is on the rise as the network security field has a lot of raising research problems like an attackers’ developed source code of malware . It keeps on developing day by day along with the security codes. To confirm your acceptance to work with us to get an exciting experience in the areas you felt boring. We are here to enrich the quality of your project at a low-cost service . We also introduce you to the various fields related to network security if you are willing to know
Why Work With Us ?
Senior research member, research experience, journal member, book publisher, research ethics, business ethics, valid references, explanations, paper publication, 9 big reasons to select us.
Our Editor-in-Chief has Website Ownership who control and deliver all aspects of PhD Direction to scholars and students and also keep the look to fully manage all our clients.
Our world-class certified experts have 18+years of experience in Research & Development programs (Industrial Research) who absolutely immersed as many scholars as possible in developing strong PhD research projects.
We associated with 200+reputed SCI and SCOPUS indexed journals (SJR ranking) for getting research work to be published in standard journals (Your first-choice journal).
PhDdirection.com is world’s largest book publishing platform that predominantly work subject-wise categories for scholars/students to assist their books writing and takes out into the University Library.
Our researchers provide required research ethics such as Confidentiality & Privacy, Novelty (valuable research), Plagiarism-Free, and Timely Delivery. Our customers have freedom to examine their current specific research activities.
Our organization take into consideration of customer satisfaction, online, offline support and professional works deliver since these are the actual inspiring business factors.
Solid works delivering by young qualified global research team. "References" is the key to evaluating works easier because we carefully assess scholars findings.
Detailed Videos, Readme files, Screenshots are provided for all research projects. We provide Teamviewer support and other online channels for project explanation.
Worthy journal publication is our main thing like IEEE, ACM, Springer, IET, Elsevier, etc. We substantially reduces scholars burden in publication side. We carry scholars from initial submission to final acceptance.
Related Pages
Our benefits, throughout reference, confidential agreement, research no way resale, plagiarism-free, publication guarantee, customize support, fair revisions, business professionalism, domains & tools, we generally use, wireless communication (4g lte, and 5g), ad hoc networks (vanet, manet, etc.), wireless sensor networks, software defined networks, network security, internet of things (mqtt, coap), internet of vehicles, cloud computing, fog computing, edge computing, mobile computing, mobile cloud computing, ubiquitous computing, digital image processing, medical image processing, pattern analysis and machine intelligence, geoscience and remote sensing, big data analytics, data mining, power electronics, web of things, digital forensics, natural language processing, automation systems, artificial intelligence, mininet 2.1.0, matlab (r2018b/r2019a), matlab and simulink, apache hadoop, apache spark mlib, apache mahout, apache flink, apache storm, apache cassandra, pig and hive, rapid miner, support 24/7, call us @ any time, +91 9444829042, [email protected].
Questions ?
Click here to chat with us
Exploring the landscape of network security: a comparative analysis of attack detection strategies
- Original Research
- Published: 05 May 2024
Cite this article

- P. Rajesh Kanna ORCID: orcid.org/0000-0002-0961-3634 1 &
- P. Santhi 2
25 Accesses
Explore all metrics
The field of computer networking is experiencing rapid growth, accompanied by the swift advancement of internet tools. As a result, people are becoming more aware of the importance of network security. One of the primary concerns in ensuring security is the authority over domains, and network owners are striving to establish a common language to exchange security information and respond quickly to emerging threats. Given the increasing prevalence of various types of attacks, network security has become a significant challenge in the realm of computing. To address this, a multi-level distributed approach incorporating vulnerability identification, dimensioning, and countermeasures based on attack graphs has been developed. Implementing reconfigurable virtual systems as countermeasures significantly improves attack detection and mitigates the impact of attacks. Password-based authentication, for instance, can be susceptible to password cracking techniques, social engineering attacks, or data breaches that expose user credentials. Similarly, ensuring privacy during data transmission through encryption helps protect data from unauthorized access, but it does not guarantee the prevention of other types of attacks such as malware infiltration or insider threats. This research explores various techniques to achieve effective attack detection. Multiple research methods have been utilized and evaluated to identify the most suitable approach for network security and attack detection in the context of cloud computing. The analysis and implementation of diverse research studies demonstrate that the based signature intrusion detection method outperforms others in terms of precision, recall, F-measure, accuracy, reliability, and time complexity.
This is a preview of subscription content, log in via an institution to check access.
Access this article
Price includes VAT (Russian Federation)
Instant access to the full article PDF.
Rent this article via DeepDyve
Institutional subscriptions
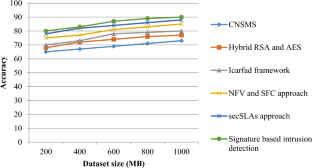
Similar content being viewed by others

Scalable Network Intrusion Detection and Countermeasure Selection in Virtual Network Systems

A Survey on Different Network Intrusion Detection Systems and CounterMeasure

Improving Attack Graph Scalability for the Cloud Through SDN-Based Decomposition and Parallel Processing
Data availability.
The authors do not have permission to share data.
Barbhuiya FA, Biswas S, Hubballi N, Nandi S (2011) A host based DES approach for detecting ARP spoofing. In: 2011 IEEE Symposium on Computational Intelligence in Cyber Security (CICS), pp 114–121
Bhatia V, Choudhary S, Ramkumar KR (2020) A comparative study on various intrusion detection techniques using machine learning and neural network. In: 2020 8th international conference on reliability, infocom technologies and optimization (trends and future directions) (ICRITO), Noida, India, 2020, pp 232–236. https://doi.org/10.1109/ICRITO48877.2020.9198008
Bhushan B, Sahoo G (2018) Recent advances in attacks, technical challenges, vulnerabilities and their countermeasures in wireless sensor networks. Wireless Pers Commun 98:2037–2077. https://doi.org/10.1007/s11277-017-4962-0
Article Google Scholar
Bhushan B, Sahoo G (2019) Secure Location-Based Aggregator Node Selection Scheme in Wireless Sensor Networks. In: Proceedings of ICETIT 2019. Lecture Notes in Electrical Engineering, vol 605. Springer https://doi.org/10.1007/978-3-030-30577-2_2
Bhushan B, Sahoo G (2020) Requirements, protocols, and security challenges in wireless sensor networks: an industrial perspective. Handbook of computer networks and cyber security: principles and paradigms. Springer, Cham, pp 683–713
Chapter Google Scholar
Casola V, De Benedictis A, Rak M, Villano U (2018) Security-by-design in multi-cloud applications: an optimization approach. Inf Sci 454:344–362
Article MathSciNet Google Scholar
Chavan S, Shah K, Dave N, Mukherjee S, Abraham A, Sanyal S (2004) Adaptive neuro-fuzzy intrusion detection systems. In: International conference on information technology: coding and computing, 2004. Proceedings. ITCC 2004, Las Vegas, NV, USA, vol 1. IEEE, pp 70–74. https://doi.org/10.1109/ITCC.2004.1286428
Chen XZ, Zheng QH, Guan XH, Lin CG (2006) Quantitative hierarchical threat evaluation model for network security. J Softw 17(4):885–897
Chen Z, Han F, Cao J, Jiang X, Chen S (2013) Cloud computing-based forensic analysis for collaborative network security management system. Tsinghua Sci Technol 18(1):40–50
Choudhury AJ, Kumar P, Sain M, Lim H, Jae-Lee H (2011) A strong user authentication framework for cloud computing. In: IEEE Asia-Pacific Services Computing Conference (APSCC), pp 110–115
Dinesha HA, Agrawal VK (2012) Multi-level authentication technique for accessing cloud services. In: IEEE International Conference on Computing, Communication and Applications (ICCCA), pp 1–4
Donadio P, Fioccola GB, Canonico R, Ventre G (2014) Network security for Hybrid Cloud. In: Euro Med Telco Conference (EMTC), 2014, pp 1–6
Fathi R, Salehi MA, Leiss EL (2015) User-friendly and secure architecture (UFSA) for authentication of cloud services. In: IEEE 8th International Conference on Cloud Computing (CLOUD), pp 516–523
Han H, Lu XL, Ren LY (2002) Using data mining to discover signatures in network-based intrusion detection. In: Proceedings of the first international conference on machine learning and cybernetics, Beijing (1)
He X, Chomsiri T, Nanda P, Tan Z (2014) Improving cloud network security using the Tree-Rule firewall. Future Gener Comput Syst 30:116–126
He J, Ota K, Dong M, Yang LT, Fan M, Wang G, Yau SS (2017) Customized network security for cloud service. IEEE Trans Serv Comput 13:801–814
Hussein MK, Zainal NB, Jaber AN (2015) Data security analysis for DDoS defense of cloud based networks. In: 2015 IEEE student conference on research and development (SCOReD), pp 305–310. IEEE
Ijaz S, Hashmi FA, Asghar S, Alam M (2017) Vector Based Genetic Algorithm to optimize predictive analysis in network security. Appl Intell 48:1086–1096
Google Scholar
Jeon J, Park JH, Jeong YS (2020) Dynamic analysis for IoT malware detection with convolution neural network model. IEEE Access 8:96899–96911
Jia X, Liu Y, Yan Y, Wu D (2016) Network security situational awareness method based on capability-opportunity-intent model. Appl Res Comput 6:1775–1779
Jiang S, Kumar R (2004) Failure diagnosis of discrete-event systems with linear-time temporal logic specifications. IEEE Trans Autom Control 49(6):934–945
Jinhua G, Kejian X (2013) ARP spoofing detection algorithm using ICMP protocol. In: 2013 International Conference on Computer Communication and Informatics (ICCCI), pp 1–6
Kaci A, Rachedi A (2019) Mc-Track: a cloud based data oriented vehicular tracking system with adaptive security. In: 2019 IEEE global communications conference (GLOBECOM). IEEE Press, pp 1–6. https://doi.org/10.1109/GLOBECOM38437.2019.901397
Kim H, Kim J, Kim Y, Kim I, Kim KJ (2018) Design of network threat detection and classification based on machine learning on cloud computing. Cluster Comput 22:2341–2350
Kishan L, Ambulgekar HP (2015) Public audit ability and privacy preserving in cloud storage. J Inf Secur Res 6(1):25–33
Ko RKL, Lee BS, Pearson S (2011)Towards achieving accountability, auditability and trust in cloud computing. InInternational conference on advances in computing and communications, pp. 432–444. Springer, Berlin, Heidelberg
Kumar S, Tapaswi S (2012) A centralized detection and prevention technique against ARP poisoning. In 2012 International Conference on Cyber Security, Cyber Warfare and Digital Forensic (CyberSec), pp. 259–264. IEEE
Lai S-F (2016) Design and implementation of cloud security defense system with software defined networking technologies. In 2016 International Conference on Information and Communication Technology Convergence (ICTC). IEEE
Li M, Tuo Y, Huang Y (2016) Cyberspace situation awareness model and application. Communications Technology
Mahajan V, Peddoju SK (2017) Integration of network intrusion detection systems and honeypot networks for cloud security. In: 2017 International Conference on Computing, Communication and Automation (ICCCA), pp 829–834
Mahalle VS, Shahade AK (2014) Enhancing the data security in cloud by implementing hybrid (rsa & aes) encryption algorithm. In: 2014 International Conference on Power, Automation and Communication (INPAC), pp 146–149
Maitlo A, Arain RH, Shaikh RA, Shaikh H, Shah MH, Shah SA, Mahar MH (2018) Optimized hybrid security model using base 64 algorithm in conjunction with substitution cipher to enhance text security. IJCSNS 18(3):93
Massonet P, Deru L, Achour A, Dupont S, Croisez L-M, Levin A, Villari M (2017) Security in lightweight network function virtualisation for federated cloud and IoT. In: 2017 IEEE 5th International Conference on Future Internet of Things and Cloud (FiCloud), pp 148–154
Massonet P (2016) Enforcement of global security policies in federated cloud networks with virtual network functions. In: 2016 IEEE 15th International Symposium on Network Computing and Applications (NCA). IEEE
Mishra P, Pilli ES, Varadharajant V, Tupakula U (2016) NvCloudIDS: a security architecture to detect intrusions at network and virtualization layer in cloud environment. In: 2016 International Conference on Advances in Computing, Communications and Informatics (ICACCI), pp 56–62
Mitra M, Banerjee P, Barbhuiya FA, Biswas S, Nandi S (2013) IDS for ARP spoofing using LTL based discrete event system framework. Netw Sci 2(3–4):114–134
Mulay M, Surana R, Tibdewal Y (2015) Enhanced security in multi cloud using visual cryptography and secret sharing. Int J Peer Rev Refereed (IJAPRR) 2(2):53–57
Naeem H, Ullah F, Naeem MR, Khalid S, Vasan D, Jabbar S, Saeed S (2020) Malware detection in industrial internet of things based on hybrid image visualization and deep learning model. Ad Hoc Netw 34(2):1–22
Nam SY, Djuraev S, Park M (2013) Collaborative approach to mitigating ARP poisoning-based man-in-the-middle attacks. Comput Netw 57(18):3866–3884
Neminath H, Biswas S, Roopa S, Ratti R, Nandi S, Barbhuiya FA, Sur A, Ramachandran V (2010) A DES approach to intrusion detection system for ARP spoofing attacks. In: 2010 18th Mediterranean Conference on Control & Automation (MED), pp 695–700
Ngo QD, Nguyen HT, Nguyen LC, Nguyen DH (2020) A survey of IoT malware and detection methods based on static features. ICT Express 6(4):280–286
Nikiforakis N, Younan Y, Joosen W (2010) HProxy: Client side detection of SSL striping attack. In Proceedings of the 7th Conference on Detections of Intrusions and Malware & Vulnerability Assessment
Rajesh Kanna P, Santhi P (2021) Unified deep learning approach for efficient intrusion detection system using integrated spatial-temporal features. Knowl-Based Syst 226:107132. https://doi.org/10.1016/j.knosys.2021.107132
Rajesh Kanna P, Santhi P (2022) Hybrid intrusion detection using mapreduce based black widow optimized convolutional long short-term memory neural networks. Expert Syst Appl 194:116545. https://doi.org/10.1016/j.eswa.2022.116545
Rajesh Kanna P, Sindhanaiselvan K, Vijaymeena MK (2017) A defensive mechanism based on PCA to defend denial of-service attack. Int J Sec Appl 11(1):71–82
Rak M, Suri N, Luna J, Petcu D, Casola V, Villano U (2013) Security as a service using an SLA-based approach via SPECS. In: IEEE 5th International Conference on Cloud Computing Technology and Science (CloudCom), vol. 2, pp 1–6
Ramalingam V, Mariappan DB, Gopal R, Baalamurugan KM (2020) An effective social internet of things (SIoT) model for malicious node detection in wireless sensor networks. CRC Press, Boca Raton
Sathish Kumar G, Premalatha K, Uma Maheshwari G, Rajesh Kanna P (2023) No more privacy concern: a privacy-chain based homomorphic encryption scheme and statistical method for privacy preservation of user’s private and sensitive data. Expert Syst Appl 234:121071. https://doi.org/10.1016/j.eswa.2023.121071
Sathish Kumar G, Premalatha K, Uma Maheshwari G, Rajesh Kanna P et al (2024) Differential privacy scheme using Laplace mechanism and statistical method computation in deep neural network for privacy preservation. Eng Appl Artif Intell 128:107399. https://doi.org/10.1016/j.engappai.2023.107399
Schoo P, Fusenig V, Souza V, Melo M, Murray P, Debar H, Medhioub H, Zeghlache D (2010) Challenges for cloud networking security. In International Conference on Mobile Networks and Management, pp. 298–313
Seo JW, Lee SJ (2016) A study on efficient detection of network-based IP spoofing DDoS and malware-infected systems. Springerplus 5(1):1878
Shafiq M, Tian Z, Bashir AK, Du X, Guizani M (2020a) Corrauc: a malicious bot-IoT traffic detection method in IoT network using machine learning techniques. IEEE Internet Things 12(2):1–13
Shafiq M, Tian Z, Sun Y, Du X, Guizani M (2020b) Selection of effective machine learning algorithm and bot-IoT attacks traffic identification for internet of things in smart city. Futur Gener Comput Syst 107:433–442
Sharma C, Kate V (2014) Icarfad: a novel framework for improved network security situation awareness. Int J Comput Appl 87(19):26–31
Sinha P, Jha VK, Rai AK, Bhushan B (2017) Security vulnerabilities, attacks and countermeasures in wireless sensor networks at various layers of OSI reference model: a survey. In 2017 International Conference on Signal Processing and Communication (ICSPC), pp. 288–293. https://doi.org/10.1109/CSPC.2017.8305855
Song MS, Lee JD, Jeong Y-S, Jeong H-Y, Park JH (2014) DS-ARP: a new detection scheme for ARP spoofing attacks based on routing trace for ubiquitous environments. Sci World J 2014:264654
Tian H, Chen Z, Chang CC, Kuribayashi M, Huang Y, Cai Y, Chen Y, Wang T (2017) Enabling public audit ability for operation behaviors in cloud storage. Soft Comput 21(8):2175–2187
Trapero R, Modic J, Stopar M, Taha A, Suri N (2017) A novel approach to manage cloud security SLA incidents. Futur Gener Comput Syst 72:193–205
Wang Q, Wang C, Li J, Ren K, Lou W (2009) Enabling public verifiability and data dynamics for storage security in cloud computing. In European symposium on research in computer security. Springer, Berlin, Heidelberg, pp. 355–370
Wei Y, Hefei YF (2009) A network security situational awareness model based on log audit and performance correction. Chin J Comput 32(4):763–772
Worku SG, Xu C, Zhao J, He X (2014) Secure and efficient privacy-preserving public auditing scheme for cloud storage’. Comput Electr Eng 40(5):1703–1713
Wu H, Ding Y, Winer C, Yao L (2010) Network security for virtual machine in cloud computing. In 2010 5th International Conference on Computer Sciences and Convergence Information Technology (ICCIT), pp. 18–21
Yang J (2012) Network security evaluation model based on cloud computing. In International Conference on Information Computing and Applications. Springer, Berlin, Heidelberg
Zardari MA, Jung LT, Zakaria MN (2013) Hybrid multicloud data security (HMCDS) model and data classification. In: 2013 international conference on advanced computer science applications and technologies, pp 166–171
Zhang L, Peng J, Du Y (2012) Evaluation method summary for information security risk assessment. J Tsinghua Univ (Science and Technology)
Zhao F, Li C, Liu CF (2014) A cloud computing security solution based on fully homomorphic encryption. In 16th International Conference on Advanced Communication Technology (ICACT), pp. 485–488
Zhengbing H, Zhitang L, Jumgi W (2008) A novel Intrusion detection system (NIDS) based on signature search of datamining. In WKDD First International Workshop on Knowledge discovery and Data Ming, pp. 10–16
Download references
Author information
Authors and affiliations.
Department of Computer Science and Engineering, Bannari Amman Institute of Technology, Erode, Tamil Nadu, India
P. Rajesh Kanna
TIFAC-CORE in Cyber Security, Amrita School of Engineering, Amrita Vishwa Vidyapeetham, Coimbatore, Tamil Nadu, India
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to P. Rajesh Kanna .
Ethics declarations
Conflict of interest.
The authors declare that they have no known competing financial interests or personal relationships that could have appeared to influence the work reported in this paper.
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
Reprints and permissions
About this article
Rajesh Kanna, P., Santhi, P. Exploring the landscape of network security: a comparative analysis of attack detection strategies. J Ambient Intell Human Comput (2024). https://doi.org/10.1007/s12652-024-04794-y
Download citation
Received : 19 February 2020
Accepted : 22 March 2024
Published : 05 May 2024
DOI : https://doi.org/10.1007/s12652-024-04794-y
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Cloud environment
- Intrusion detection
- Network security
- Attack detection
- Find a journal
- Publish with us
- Track your research
NETWORK SECURITY RESEARCH TOPICS
Network security research topics is also one of most accepted area for Research dealing with many protocols. Importance and necessitate of network security makes it admirable area for research. Why is Network Security so important, this question revolve around every one of us. It has also a simple answer which lies in its name i.e. SECURITY. Due to its interdisciplinary nature, we can also develop many security protocols to avoid the current network security violation. To perform an outstanding research, we also need to review recent security violations and also explore related methods and also techniques for it.
We can also work on network forensic and analyze best technique and algorithm for it.
Internet, the word which changed the world depends on Network-security as it is prone to many security attacks, malicious activities, also misleading information and unintelligible communication. Hence, there is also a need for effective security solution which can also be taken as a challenge by young scholars and work on it. Network security research topics which are currently undergoing are cyber-insurance, cumulative Metric for an information network etc. Most commonly also used security mechanisms are Encipherment, Digital signature, also coding-decoding etc. But these are also fundamentals of Network security. It is also fast growing field which needs current update and latest algorithm also for enhance the research. For this, we have a wide collection of Network security research topics with its tool
RESEARCH ISSUES IN NETWORK-SECURITY:
RFID technologies Security in Ad hoc network Security also in telecommunication network Wireless security Collaborative network security Defining network security protocols Network security also in protection measures Network forensics Embedded also in network security IPV6 network security Malware detection etc.
SOFTWARE AND TOOL DETAILS ========================== 1)NeSSi(JAVA) 2)NST(C) 3)JAVASNOOP(JAVA) 4)EXata (C++) 5)NETwork Attacks (also in NETA-omnet++)
Purpose of the every software and tool =======================================.
NeSSi–> novel network simulation tool also used for security research and evaluation purposes due to its varied capability.
NST–> performs routine security, networking diagnostic and also monitoring tasks.
JAVASNOOP–> Security tool also used to test the security of Java applications.
EXata–> network emulator which also provides network security and cyber warfare features
ETwork Attacks (NETA)–>Framework also to simulate attack behaviors in heterogeneous networks using OMNeT++.
Related Search Terms
network security research issues, network security research topics, phd projects in network security, Research issues in network security
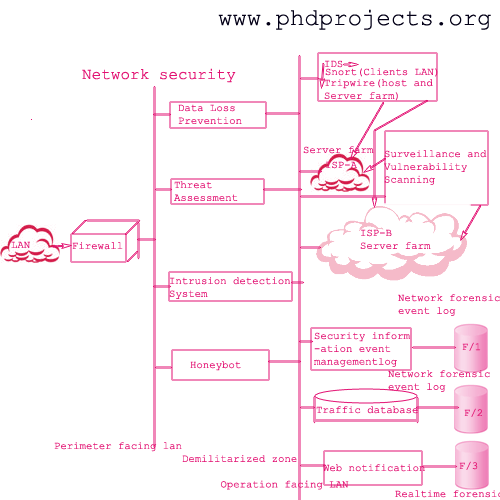
Funding support: Army Research Office (ARO), and the Army Educational Outreach Program (AEOP) .
3. Security and Privacy in Dynamic Spectrum Sharing
4. Security and Privacy Protection of Data Collection and Analysis
On the other hand, in recent years large companies are already collecting many users' data for analytics/advertisement purposes and providing better services. To protect users' privacy, encryption may not be the best solution in this scenario since the service provider must be able to query statistical information from the data. Data obfuscation/perturbation techniques have became promising as they aim at hiding the secrets of individual users while still allowing statistical analysis. Differential privacy is a formal notion to quantify the privacy level of users in this setting. However, how to achieve a good balance between privacy and data utility is always a challenge, especially in the local setting where the service provider is untrusted. Our recent research focus on developing context-aware privacy notions and mechanisms to enhance the utility-privacy tradeoff, by leveraging statistical and information-theoretic approaches.
Funding support: National Science Foundation (NSF) and Amazon Web Services. Project Websites: Secure data service outsourcing (completed)
5. Cyber-Physical System Security: Autonomous and Connected Vehicles & Unmanned Aerial Systems.
Vehicular automation is now appearing that promises a new era of transportation technology. Although automation introduces opportunities to optimize the efficiency and safety of transportation systems, it also exposes users to new security risks due to increased reliance on computers, sensors and networked communication. The goal of this research is to provide a secure foundation for a transportation system that increasingly relies on cooperative automation strategies and vehicle connectedness to achieve increases in safety, efficiency, and capacity. We anticipate a three phase deployment of automation technologies: (1) autonomous vehicles without connectivity will use local sensing to form and maintain platoons, (2) vehicles will begin to incorporate traffic-related information shared via vehicle-to-vehicle communication into their decision making processes, and (3) a trusted infrastructure will emerge that supplies guidance to vehicles via vehicle-to-infrastructure communication to achieve safe, optimal, and adaptive system-wide traffic flows. Our work examine the vulnerabilities of inter-vehicular and intra-vehicular systems from both communication and controls perspectives, then propose defense mechanisms that are practical and low-overhead, for example, by deriving security and trust from the physical layer. Unmanned Aircraft Systems (UAS) have received significant attention in the past decade due to their utility in intelligence, reconnaissance, and recreational applications at a fraction of the cost of employing manned aircraft. UAS systems are an advancing technology with tremendous potential, but which also raise serious concerns with regard to safety, security, and privacy. As UASs continue to proliferate, aviation regulatory agencies around the world are facing a challenging dilemma in terms of safely integrating UAS operations into their respective national airspace systems and enforcing their compliance to relevant regulations. The significance of the dilemma is exacerbated by the lack of technical approaches for effectively countering the threats posed by nefarious or unintentionally noncompliant UAS operations and enforcing the relevant regulations to safeguard controlled/restricted airspace. This project aims to address this critical need by developing offensive and defensive measures for detecting and bringing down UASs that violate controlled/restricted airspace in an automated, controlled, and reliable manner. Our project team proposes to develop a set of systematic approaches for countering the threat posed by nefarious or noncompliant UASs. The multi-disciplinary team consists of exertise that include UAS flight control systems, CPS security, wireless communications and networking, and reinforcement learning and intelligent control. Funding support: National Science Foundation (NSF). Project Websites: Security in autonomous vehicular transportation News coverage: The Epoch Times, Driverless transportation , The Atlantic , 163 Tech News (网易科技新闻) , 爬车网
Funded Research Projects
- DURIP: A Millimeter-Wave Communication System for Wireless Security and Networking Research and Education, $249,934, Army Research Office, 04/21/2021 - 04/20/2022, PI (Co-PI: Loukas Lazos).
- Undergraduate Research Apprentice Program (URAP)/High School Apprentice Program (HSAP) Supplement, $15,000, Army Research Office, 05/15/2021 - 08/15/2021, PI (Co-PI: Loukas Lazos).
- In-band Wireless Trust Establishment Resistant to Advanced Signal Manipulations, Army Research Office, 01/01/2019 - 12/31/2021, PI (Co-PI: Loukas Lazos).
- SaTC: CORE: Medium: Collaborative: Enforcement of Geofencing Policies for Commercial Unmanned Aircraft Systems, National Science Foundation, 09/01/2018 - 08/31/2021, PI.
- SpecEES: Secure and Fair Spectrum Sharing for Heterogeneous Coexistent Systems , National Science Foundation, 10/1/2017-9/30/2020, Co-PI (with PI Loukas Lazos and Co-PI Marwan Krunz) (Project website)
- Toward High Performance Tactical Multi Hop Wireless Networks via Exploiting Antenna Reconfigurability, Office of Naval Research, 6/1/2016-5/31/2019.
- EARS: Collaborative Research: Crowdsourcing-Based Spectrum Etiquette Enforcement in Dynamic Spectrum Access , National Science Foundation, $360,000, 1/1/2015-12/31/2018, PI (Co-PIs: Ryan Gerdes and Bedri Cetiner). (Project website)
- TWC: Medium: Secure and Resilient Vehicular Platooning , National Science Foundation , 8/1/2014-7/31/2019, $1,229,923, Co-PI (PI: Ryan Gerdes) (Project website)
- CAREER: Toward Cooperative Interference Mitigation for Heterogeneous Multi-hop MIMO Wireless Networks , $489,999, National Science Foundation, 7/1/2014-6/31/2019, PI (Project website) .
- CSR: Small: Collaborative Research: Towards User Privacy in Outsourced Cloud Data Services , $175,000, National Science Foundation, 10/1/2012-9/31/2015, PI.
- Proving the Possession of Multi-Owner Data in the Cloud, $2,500, Amazon AWS Research Grant, 2014-2016
We thank the generous support of:
This is a potential security issue, you are being redirected to https://csrc.nist.gov .
You have JavaScript disabled. This site requires JavaScript to be enabled for complete site functionality.
An official website of the United States government
Here’s how you know
Official websites use .gov A .gov website belongs to an official government organization in the United States.
Secure .gov websites use HTTPS A lock ( Lock Locked padlock icon ) or https:// means you’ve safely connected to the .gov website. Share sensitive information only on official, secure websites.
- Drafts for Public Comment
- All Public Drafts
- NIST Special Publications (SPs)
- NIST interagency/internal reports (NISTIRs)
- ITL Bulletins
- White Papers
- Journal Articles
- Conference Papers
- Security & Privacy
Applications
Technologies.
- Laws & Regulations
- Activities & Products
- News & Updates
- Cryptographic Technology
- Secure Systems and Applications
- Security Components and Mechanisms
- Security Engineering and Risk Management
- Security Testing, Validation, and Measurement
- Cybersecurity and Privacy Applications
- National Cybersecurity Center of Excellence (NCCoE)
- National Initiative for Cybersecurity Education (NICE)
Security and Privacy
- digital signatures
- key management
- lightweight cryptography
- message authentication
- post-quantum cryptography
- random number generation
- secure hashing
- cybersecurity supply chain risk management
- general security & privacy
- access authorization
- access control
- Personal Identity Verification
- public key infrastructure
- personally identifiable information
- privacy engineering
- categorization
- continuous monitoring
- controls assessment
- privacy controls
- security controls
- risk assessment
- roots of trust
- system authorization
- advanced persistent threats
- information sharing
- intrusion detection & prevention
- vulnerability management
- accessibility
- testing & validation
- acquisition
- asset management
- audit & accountability
- awareness training & education
- configuration management
- contingency planning
- incident response
- maintenance
- media protection
- patch management
- personnel security
- physical & environmental protection
- program management
- security automation
- reliability
- artificial intelligence
- cloud & virtualization
- combinatorial testing
- personal computers
- quantum information science
- smart cards
- operating systems
- communications & wireless
- cyber-physical systems
- cybersecurity education
- cybersecurity framework
- cybersecurity workforce
- industrial control systems
- Internet of Things
- mathematics
- positioning navigation & timing
- small & medium business
Laws and Regulations
- Comprehensive National Cybersecurity Initiative
- Cybersecurity Strategy and Implementation Plan
- Cyberspace Policy Review
- Executive Order 13636
- Executive Order 13702
- Executive Order 13718
- Executive Order 13800
- Executive Order 13905
- Executive Order 14028
- Executive Order 14110
- Federal Cybersecurity Research and Development Strategic Plan
- Homeland Security Presidential Directive 7
- Homeland Security Presidential Directive 12
- OMB Circular A-11
- OMB Circular A-130
- Cyber Security R&D Act
- Cybersecurity Enhancement Act
- E-Government Act
- Energy Independence and Security Act
- Federal Information Security Modernization Act
- First Responder Network Authority
- Health Insurance Portability and Accountability Act
- Help America Vote Act
- Internet of Things Cybersecurity Improvement Act
- Federal Acquisition Regulation
Activities and Products
- annual reports
- conferences & workshops
- quick start guides
- reference materials
- standards development
- financial services
- hospitality
- manufacturing
- public safety
- telecommunications
- transportation
File(s) under embargo
until file(s) become available
An Image-based ML Approach for Wi-Fi Intrusion Detection System and Education Modules for Security and Privacy in ML
The research work presented in this thesis focuses on two highly important topics in the modern age. The first topic of research is the development of various image-based Network Intrusion Detection Systems (NIDSs) and performing a comprehensive analysis of their performance. Wi-Fi networks have become ubiquitous in enterprise and home networks which creates opportunities for attackers to target the networks. These attackers exploit various vulnerabilities in Wi-Fi networks to gain unauthorized access to a network or extract data from end users' devices. The deployment of an NIDS helps detect these attacks before they can cause any significant damages to the network's functionalities or security. Within the scope of our research, we provide a comparative analysis of various deep learning (DL)-based NIDSs that utilize various imaging techniques to detect anomalous traffic in a Wi-Fi network. The second topic in this thesis is the development of learning modules for security and privacy in Machine Learning (ML). The increasing integration of ML in various domains raises concerns about its security and privacy. In order to effectively address such concerns, students learning about the basics of ML need to be made aware of the steps that are taken to develop robust and secure ML-based systems. As part of this, we introduce a set of hands-on learning modules designed to educate students on the importance of security and privacy in ML. The modules provide a theoretical learning experience through presentations and practical experience using Python Notebooks. The modules are developed in a manner that allows students to easily absorb the concepts regarding privacy and security of ML models and implement it in real-life scenarios. The efficacy of this process will be obtained from the results of the surveys conducted before and after providing the learning modules. Positive results from the survey will demonstrate the learning modules were effective in imparting knowledge to the students and the need to incorporate security and privacy concepts in introductory ML courses.
Cybersecurity Modules Aligned with Undergraduate Computer Science and Engineering Curricula
Directorate for Education & Human Resources
Degree Type
- Master of Science
- Electrical and Computer Engineering
Campus location
Advisor/supervisor/committee chair, additional committee member 2, additional committee member 3, usage metrics.
- System and network security
- Data security and protection
- Data and information privacy
- Adversarial machine learning
- Deep learning

- Our Promise
- Our Achievements
- Our Mission
- Proposal Writing
- System Development
- Paper Writing
- Paper Publish
- Synopsis Writing
- Thesis Writing
- Assignments
- Survey Paper
- Conference Paper
- Journal Paper
- Empirical Paper
- Journal Support
- Network Security Research Topics
A definition of network security is the process of taking concurrent actions for network environment protection from illegal access by attackers. We can see various activities of attackers in the network such as misuse, data loss, modification, improper disclosure , and thereby legitimate user’s privacy is leaked.
Our service i.e. network security research topics are your secure environment to get comprehensive knowledge and guidance in network security . On this page, we discuss several important research issues and advances in network security.
HOW TO SECURE THE NETWORK?
There are a different number of threat detection responses are available in network security that is as follows.
- Filtering Malicious Packets: threats are detected by extracting traffic flow and packet features and these features are classified according to their mean values.
- Creation of Proxy Services: Packets and service requests are protected in the application layer.
- Stateful Inspection: Concurrent monitoring of service requests for dynamic filtering of packets which protects through deep inspection.
- Firewall (next generation): Both application layer and deep packet inspection are involved in the design of the firewall.
Due to the wide coverage of network security, we listed a few interesting network security research topics . In addition to these, we can also be establishing more research ideas. However, we will also look at own research idea from students and scholars .
Research Areas in Network Security
- Cellular Communication
- Internet of Things
- Software-Defined Networks
- Ad hoc Networks
- Fog Computing
- Volunteer Computing
- Smart Communication (Industry / Grid)
- Mobile Edge Computing
One of the decisive aims of this page is to get knowledge in network security for scholars. With this in mind here, we discuss the attackers in different types of networks . These attacks increasing complexity and affecting the network performance.
Important Network Security Attacks
We guide research scholars to choose innovative network security research topics based from preventing attack system in network security.
Black Hole Attack
- Goal: To send malicious route request and response messages
- Types of Networks Affected
- FANET,MANET
- Underwater WSN & WSN
- Wireless Mesh Networks
- Mesh Network Simulator
- And many more
Masquerade Attack
- Goal: Use fake IP address and Identifier for accessing the networks
- Software-Defined Networks / NFV
- 4G, 5G, and 6G Networks
- Wireless Ad Hoc Networks
DDoS Attack
- Goal: To cause network services unavailable Types of Networks Affected
- Software Defined Networking
- Content-Centric Networks
- 5G / 6G Cellular Networks
- Cloud and Fog RAN
Radio Jamming Attack
- Goal: Send unwanted signals for adding noise to the legitimate signals
- Cognitive Radio Network
- Industrial Internet of Things
- Named Data Networking
- Cellular and Ad Hoc Networks
Recently, all types of wireless networks are vulnerable to attackers such as WSN, SDN, NDN, MANET, and VANET . In particular, Distributed Denial of Service (DDoS) attacks are significant for detection. In sensor networks and IoT, DDoS attacks detection is necessary since IoT devices are very resource constraints. To fight with attackers to avoid restrictions in memory and other resources, computations with fewer techniques are useful. In this case, traditional cryptographic algorithms do not suit for satisfying authentication, confidentiality, integrity, and non-repudiation requirements.
Cryptography Algorithms in Network Security
- Quantum Key Distribution
- PRIDE and PRESENT
- Variant ECC Algorithms (e.g. Edwards Curve)
- Honey Encryption
- XTEA and TEA
Similar to cryptography algorithms, artificial intelligence (AI) is used for various threats protection . When choosing an AI technique, the number of layers must be smaller to reduce the number of computations and overhead in a network. Some of the techniques are listed below.
AI Algorithms in Network Security
- Deep Q Learning
- Convolutional Neural Network (CNN)
- Recurrent Neural Network (RNN)
- Deep Belief Network (DBN)
- Gated Recurrent Unit (GRU)
- Stacked Polynomial Networks
- AlexNet, SliceNet and LiteNet
Thesis writing is the central point in any stream of your course. It summarizes the core research idea that scholar wants to show in their research field. To validate any network security research topics , novelty and worthy publications is crucial which becomes simpler to collect from us. Our thesis writing in network security service is offered by technical engineers who are directly involved to assist you in a thesis or any other services such as proposal writing, synopsis writing, paper writing . Let’s look at below to know more about the thesis.
What are the chapters in thesis writing?
- State the importance of the research topic and discuss the background
- Give literature review with advantages and disadvantages
- Define terminologies and scope of the thesis
- Outline recent applications
- Discuss research problems and solutions
- Determine the proposed approach importance
- State the research questions and problems
- Given the hypothesis
- Describe the results and methodology
- Finally, conclude the research
We are customizing every part of the proposed approach in terms of protocol design, and generate more scenarios during comparison . Hence, thesis writing is full-fledged starting from novel network security research topics selection. You can contact us to making the new research with a novel set of techniques in network security.
MILESTONE 1: Research Proposal
Finalize journal (indexing).
Before sit down to research proposal writing, we need to decide exact journals. For e.g. SCI, SCI-E, ISI, SCOPUS.
Research Subject Selection
As a doctoral student, subject selection is a big problem. Phdservices.org has the team of world class experts who experience in assisting all subjects. When you decide to work in networking, we assign our experts in your specific area for assistance.
Research Topic Selection
We helping you with right and perfect topic selection, which sound interesting to the other fellows of your committee. For e.g. if your interest in networking, the research topic is VANET / MANET / any other
Literature Survey Writing
To ensure the novelty of research, we find research gaps in 50+ latest benchmark papers (IEEE, Springer, Elsevier, MDPI, Hindawi, etc.)
Case Study Writing
After literature survey, we get the main issue/problem that your research topic will aim to resolve and elegant writing support to identify relevance of the issue.
Problem Statement
Based on the research gaps finding and importance of your research, we conclude the appropriate and specific problem statement.
Writing Research Proposal
Writing a good research proposal has need of lot of time. We only span a few to cover all major aspects (reference papers collection, deficiency finding, drawing system architecture, highlights novelty)
MILESTONE 2: System Development
Fix implementation plan.
We prepare a clear project implementation plan that narrates your proposal in step-by step and it contains Software and OS specification. We recommend you very suitable tools/software that fit for your concept.
Tools/Plan Approval
We get the approval for implementation tool, software, programing language and finally implementation plan to start development process.
Pseudocode Description
Our source code is original since we write the code after pseudocodes, algorithm writing and mathematical equation derivations.
Develop Proposal Idea
We implement our novel idea in step-by-step process that given in implementation plan. We can help scholars in implementation.
Comparison/Experiments
We perform the comparison between proposed and existing schemes in both quantitative and qualitative manner since it is most crucial part of any journal paper.
Graphs, Results, Analysis Table
We evaluate and analyze the project results by plotting graphs, numerical results computation, and broader discussion of quantitative results in table.
Project Deliverables
For every project order, we deliver the following: reference papers, source codes screenshots, project video, installation and running procedures.
MILESTONE 3: Paper Writing
Choosing right format.
We intend to write a paper in customized layout. If you are interesting in any specific journal, we ready to support you. Otherwise we prepare in IEEE transaction level.
Collecting Reliable Resources
Before paper writing, we collect reliable resources such as 50+ journal papers, magazines, news, encyclopedia (books), benchmark datasets, and online resources.
Writing Rough Draft
We create an outline of a paper at first and then writing under each heading and sub-headings. It consists of novel idea and resources
Proofreading & Formatting
We must proofread and formatting a paper to fix typesetting errors, and avoiding misspelled words, misplaced punctuation marks, and so on
Native English Writing
We check the communication of a paper by rewriting with native English writers who accomplish their English literature in University of Oxford.
Scrutinizing Paper Quality
We examine the paper quality by top-experts who can easily fix the issues in journal paper writing and also confirm the level of journal paper (SCI, Scopus or Normal).
Plagiarism Checking
We at phdservices.org is 100% guarantee for original journal paper writing. We never use previously published works.
MILESTONE 4: Paper Publication
Finding apt journal.
We play crucial role in this step since this is very important for scholar’s future. Our experts will help you in choosing high Impact Factor (SJR) journals for publishing.
Lay Paper to Submit
We organize your paper for journal submission, which covers the preparation of Authors Biography, Cover Letter, Highlights of Novelty, and Suggested Reviewers.
Paper Submission
We upload paper with submit all prerequisites that are required in journal. We completely remove frustration in paper publishing.
Paper Status Tracking
We track your paper status and answering the questions raise before review process and also we giving you frequent updates for your paper received from journal.
Revising Paper Precisely
When we receive decision for revising paper, we get ready to prepare the point-point response to address all reviewers query and resubmit it to catch final acceptance.
Get Accept & e-Proofing
We receive final mail for acceptance confirmation letter and editors send e-proofing and licensing to ensure the originality.
Publishing Paper
Paper published in online and we inform you with paper title, authors information, journal name volume, issue number, page number, and DOI link
MILESTONE 5: Thesis Writing
Identifying university format.
We pay special attention for your thesis writing and our 100+ thesis writers are proficient and clear in writing thesis for all university formats.
Gathering Adequate Resources
We collect primary and adequate resources for writing well-structured thesis using published research articles, 150+ reputed reference papers, writing plan, and so on.
Writing Thesis (Preliminary)
We write thesis in chapter-by-chapter without any empirical mistakes and we completely provide plagiarism-free thesis.
Skimming & Reading
Skimming involve reading the thesis and looking abstract, conclusions, sections, & sub-sections, paragraphs, sentences & words and writing thesis chorological order of papers.
Fixing Crosscutting Issues
This step is tricky when write thesis by amateurs. Proofreading and formatting is made by our world class thesis writers who avoid verbose, and brainstorming for significant writing.
Organize Thesis Chapters
We organize thesis chapters by completing the following: elaborate chapter, structuring chapters, flow of writing, citations correction, etc.
Writing Thesis (Final Version)
We attention to details of importance of thesis contribution, well-illustrated literature review, sharp and broad results and discussion and relevant applications study.
How PhDservices.org deal with significant issues ?
1. novel ideas.
Novelty is essential for a PhD degree. Our experts are bringing quality of being novel ideas in the particular research area. It can be only determined by after thorough literature search (state-of-the-art works published in IEEE, Springer, Elsevier, ACM, ScienceDirect, Inderscience, and so on). SCI and SCOPUS journals reviewers and editors will always demand “Novelty” for each publishing work. Our experts have in-depth knowledge in all major and sub-research fields to introduce New Methods and Ideas. MAKING NOVEL IDEAS IS THE ONLY WAY OF WINNING PHD.
2. Plagiarism-Free
To improve the quality and originality of works, we are strictly avoiding plagiarism since plagiarism is not allowed and acceptable for any type journals (SCI, SCI-E, or Scopus) in editorial and reviewer point of view. We have software named as “Anti-Plagiarism Software” that examines the similarity score for documents with good accuracy. We consist of various plagiarism tools like Viper, Turnitin, Students and scholars can get your work in Zero Tolerance to Plagiarism. DONT WORRY ABOUT PHD, WE WILL TAKE CARE OF EVERYTHING.
3. Confidential Info
We intended to keep your personal and technical information in secret and it is a basic worry for all scholars.
- Technical Info: We never share your technical details to any other scholar since we know the importance of time and resources that are giving us by scholars.
- Personal Info: We restricted to access scholars personal details by our experts. Our organization leading team will have your basic and necessary info for scholars.
CONFIDENTIALITY AND PRIVACY OF INFORMATION HELD IS OF VITAL IMPORTANCE AT PHDSERVICES.ORG. WE HONEST FOR ALL CUSTOMERS.
4. Publication
Most of the PhD consultancy services will end their services in Paper Writing, but our PhDservices.org is different from others by giving guarantee for both paper writing and publication in reputed journals. With our 18+ year of experience in delivering PhD services, we meet all requirements of journals (reviewers, editors, and editor-in-chief) for rapid publications. From the beginning of paper writing, we lay our smart works. PUBLICATION IS A ROOT FOR PHD DEGREE. WE LIKE A FRUIT FOR GIVING SWEET FEELING FOR ALL SCHOLARS.
5. No Duplication
After completion of your work, it does not available in our library i.e. we erased after completion of your PhD work so we avoid of giving duplicate contents for scholars. This step makes our experts to bringing new ideas, applications, methodologies and algorithms. Our work is more standard, quality and universal. Everything we make it as a new for all scholars. INNOVATION IS THE ABILITY TO SEE THE ORIGINALITY. EXPLORATION IS OUR ENGINE THAT DRIVES INNOVATION SO LET’S ALL GO EXPLORING.
Client Reviews
I ordered a research proposal in the research area of Wireless Communications and it was as very good as I can catch it.
I had wishes to complete implementation using latest software/tools and I had no idea of where to order it. My friend suggested this place and it delivers what I expect.
It really good platform to get all PhD services and I have used it many times because of reasonable price, best customer services, and high quality.
My colleague recommended this service to me and I’m delighted their services. They guide me a lot and given worthy contents for my research paper.
I’m never disappointed at any kind of service. Till I’m work with professional writers and getting lot of opportunities.
- Christopher
Once I am entered this organization I was just felt relax because lots of my colleagues and family relations were suggested to use this service and I received best thesis writing.
I recommend phdservices.org. They have professional writers for all type of writing (proposal, paper, thesis, assignment) support at affordable price.
You guys did a great job saved more money and time. I will keep working with you and I recommend to others also.
These experts are fast, knowledgeable, and dedicated to work under a short deadline. I had get good conference paper in short span.
Guys! You are the great and real experts for paper writing since it exactly matches with my demand. I will approach again.
I am fully satisfied with thesis writing. Thank you for your faultless service and soon I come back again.
Trusted customer service that you offer for me. I don’t have any cons to say.
I was at the edge of my doctorate graduation since my thesis is totally unconnected chapters. You people did a magic and I get my complete thesis!!!
- Abdul Mohammed
Good family environment with collaboration, and lot of hardworking team who actually share their knowledge by offering PhD Services.
I enjoyed huge when working with PhD services. I was asked several questions about my system development and I had wondered of smooth, dedication and caring.
I had not provided any specific requirements for my proposal work, but you guys are very awesome because I’m received proper proposal. Thank you!
- Bhanuprasad
I was read my entire research proposal and I liked concept suits for my research issues. Thank you so much for your efforts.
- Ghulam Nabi
I am extremely happy with your project development support and source codes are easily understanding and executed.
Hi!!! You guys supported me a lot. Thank you and I am 100% satisfied with publication service.
- Abhimanyu
I had found this as a wonderful platform for scholars so I highly recommend this service to all. I ordered thesis proposal and they covered everything. Thank you so much!!!
Related Pages

Network Security PhD Research Topics
Network Security PhD Research Topics offer innovative platform for you to get our dedicated professional’s inventive ideas to improve your knowledge.We have 100+ international-level celebrated scientists to provide the best guidance for you in each step of your research.We offer highly confidential research for you by our best knowledge. Today, network security is one of the important aspects of networking technology. Due to this, a vast array of students is also utilizing our PhD Research Topics service from all over the world.
We have high experience in this respective field. Every day, we also update our creative ideas to spread our knowledge among students and research colleagues to reach a great position in this competitive world; if you are enthusiastic about utilizing our Network Security PhD Research Topic service, taking your mobile dial our number.
Security PhD Research Topics
Network Security PhD Research Topics offer amazing environment for PhD colleagues to chosen high tech research topics to accomplish their PhD curriculum. Our professionals provide the best knowledge in network security projects and their implementation. With our inclusive training, we can also easily implement any type of project by own.
Here, we talk about network security,
…”Network security is a dedicated field in a computer network that provides computer networking infrastructure production. It prevents and also monitors denial of computer network, misuse, unauthorized access, network-accessible resources, etc.”
Nearly we have also finished thousands of network security research in various research areas. Here, we also provided some of the network security areas for your better reference
Major Research Areas for Network PhD Research Topics
- Visual Cryptography
- Multimedia Security
- Wireless Network Security
- Image Forensic
- Cryptography and Cyber Security
- RFID Technology
- Stegnography
- Information Security and Forensic
- Security also in Telecommunication Networks
- Embedded System Security
- Ad Hoc Network Security
- Web Security
- Software Defined Networks Security
- IPv6 Network Security
- Collaborative Security
- Security also in Wireless Sensor Networks
- Network Security also in Neural Networks
- Security also in Cloud Computing and Big Data
- And also Security in Vehicular Ad Hoc Networks
Network Security Related Tools and Software
- NETZ-OMNET++
- NESSI[JAVA]
Antivirus Software for Network Security
- Norton Security Software
- Avira Antivirus Pro
- Malwarebytes Software
- Panda Antivirus
- REVE Antivirus
- VMware Virtual Center
Firewalls for Network Security
- Barracuda Firewall
- Comodo Free Firewall
- Cisco Firewall
- Anti NetCut3
- Zonealarm also in Firewall
- Little Snitch
- also FortiClient
Major Networking Attack
- Smartphone Trojan Horse
- Ransom-ware
- Medical Data Breach
- DDoS Attack
- IPv6 Traffic
- Pink Sweep also in Attack
- Hijack Attack
- Cyber Crime
- Brute Force Attack
- MiTM Attack
- Shellshock Attack
- Domain Name Server also in Attack
- Secure Sockets Layer
- Server Spoof Attack
- Industrial IoT Hack Attack
- Browser Attack
- Backdoor attack
- Port Scan Attack
- Jamming / Traffic Attack
- Massive DoS Attack
- Wormhole Attack
- Packet Capturing Attack
- Black Hole Attack
- Phishing Attack
- Password Cracking Attack
- also in Key Logger Attack
Network Security Algorithms
- ECC (Elliptic Curve Cryptographic) Algorithm
- Genetic algorithm also with Path Re-linking
- Diffie-Hellman Key Exchange
- Privacy Preserved Full-Text Retrieval also in Algorithm
- Boyer Moore String Matching also in Algorithm
- BESA Cryptographic also in Algorithms
- Real Time Rule Matching also in Algorithm
- Path Redundancy also Based Security also in Algorithm
- Byte Rotation also in Algorithm
- Adaptive Weighted also in algorithm
- Hybrid Cryptographic (AES and also DES) Algorithm
- Dynamic Cryptographic also in Algorithm
- Enhanced Password Processing Algorithm also Based on Visual Cryptography
- Packet Classification also in Algorithm
- Efficient Lossless Symmetric Key Cryptographic also in Algorithm
- BSC also in Cryptography Algorithm
- Simon Cryptography also in Algorithm
- Post Quantum Cryptographic also in Algorithm
- Hybrid Cryptographic Algorithm (AES, Blowfish, RC6 and also BRA)
- Network Access Control also in Algorithm
Latest Network Security PhD Research Topics
- Differentiated Services by Security and also Quality of Service Game Theoretic Joint Optimization in Next Generation Heterogeneous Networks
- Chaotic Compressive Sensing also Based Energy Efficient and also Secure Data Transmission System in Body to Body Networks
- Secure Data Aggregation Using FKM (Fuzzy Knowledge also Based Mechanism) in Wireless Sensor Networks
- Hidden Information Transmission also Using Frequency Based Secure Stegnography Algorithm
- Physical Layer Security also Using Key Space Improved Chaotic Encryption Scheme in OFDE-PON
- Video Surveillance Application also Using Efficient Compressed Sensing Based Security Mechanism also in Wireless Multimedia Sensor Networks
- Particle Swarm Optimization Mechanism under Path Loss also for Analyze Link Budget Power in Secured Cognitive Ad Hoc Networks
For your best understanding, we also aforesaid some interesting information about network security such as research areas, tools and software, antivirus software, firewalls, networking attacks, algorithms, and advanced research topics. Do you aspire to get more information from us? Approach us also directly.
“Doesn’t matter…………Being the best”
“always matters…………doing the best”, “let’s join together to bring out the best”, related pages, services we offer.
Mathematical proof
Pseudo code
Conference Paper
Research Proposal
System Design
Literature Survey
Data Collection
Thesis Writing
Data Analysis
Rough Draft
Paper Collection
Code and Programs
Paper Writing
Course Work
e-mail address: [email protected]
Tel 7639361621

Network security is the process that permits the users to regulate the network and manage the operating system and applications in the network. This page deals with the significant research aspects of network security. Let us start with the types of network security.
List of Network Security Research Areas
- Cryptographic Hashing
- Source Location Privacy
- Symmetric Key Cryptography
- IaaS Cloud Forensics
- Anomaly-based IDS
- Lightweight Architecture
- Retraining Massive Data
- Public Key Cryptography
- Software Defined Networking
- Hybrid Signature
- Identity-based Cryptography
- ANN-based Steganography
- Certificateless Cryptography
- Blockchain-based IDS
- Lightweight Cryptography
- Network Intrusion Detection System
- Internet Traffic Transforming
- Fiber Optical Security

Types of Network Security
- It is one of the network security systems which standardize the network traffic the regulated protocols and the firewall which has the part in the barriers among the internet and the internal networks
- It has a device that can scan the networks and that recognize the potential security issues and for example, testing for device penetration
- It is used for the surplus traffic such as the anti-virus scanning device and the content filtering device
- The devices scan and recognize the unnecessary traffic such as the intrusion detection appliances
For add on information, all the research field has its research issues. Similarly, the research problems in network security research areas are highlighted by our research experts with the appropriate solutions.
Network Security Problems and Solutions
- Data Leakage, Illegal Access and Access Illegal IoT
- Privacy Preserving
- Data and Privacy Leakage and Counterfeit
- Authentication, End to End Security and Encryption
- Security and Privacy Problems
- Security Mechanism
- Eavesdropping and Illegal Data Collecting
- Encryption, Data Authentication and etc
- Privacy Leakage and Data Accessing
- Access Control Mechanism, Data Processing
- Data Leakage and wsn simulation
- Access Control, Self Destruction
How to protect the network from attackers?
- It doesn’t use any algorithms or protocols
- If any two files have the same hash functions and it provided the stable authentication
- Evade the circular dependence
- The security dependency among the boundaries is clear
- Definite with the effective control
- The security control should be hinder and reconfigurable
- To protect the impersonation the well build cryptographic mechanisms are used
- The well build cryptographic mechanism has such qualities (updated, revoked and generated)
To conclude, we work by the best effort source and doing projects by all latest lists of updates in the network security research areas . So contact us for your network security research projects & thesis .

IMAGES
VIDEO
COMMENTS
Topics in Computer and Network Security Stanford CS 356, Fall 2023. CS 356 is graduate course that covers foundational work and current topics in computer and network security. The course consists of reading and discussing published research papers, presenting recent security work, and completing an original research project.
Cybersecurity-Related Research Topics. Developing machine learning algorithms for early detection of cybersecurity threats. The use of artificial intelligence in optimizing network traffic for telecommunication companies. Investigating the impact of quantum computing on existing encryption methods.
Criminal Law. Cyber Security Future Research Topics. Developing more effective methods for detecting and responding to cyber attacks. Investigating the role of social media in cyber security. Examining the impact of cloud computing on cyber security. Investigating the security implications of the Internet of Things.
Description of the topic. Network Security has become essential nowadays and there is a need for setting up robust mechanisms to maintain confidentiality and integrity (Feng et al., 2023). Due to the number of security mechanisms available, organizations found it hard to finalize and implement them on their network.
The research is conducted based on analysis of threat, risk and vulnerability in an enterprise network along with countermeasures to overcome the security incidents in an enterprise network.
Network Security Research Topics. Nowadays, different topics are emerging for comparative analysis research in the field of network security that contains advanced technologies and tools. Share your Network Security Research Ideas and Topics with us, and our team of top-level experts will provide you with guidance and support.
Wireless Network Security . Wireless Router . Network Security System. The use of computer networks in an agency aims to facilitate communication and data transfer between devices. The network that can be applied can be using wireless media or LAN cable. At SMP XYZ, most of the computers still use wireless networks.
Feature papers represent the most advanced research with significant potential for high impact in the field. A Feature Paper should be a substantial original Article that involves several techniques or approaches, provides an outlook for future research directions and describes possible research applications. ... The featured topic Network ...
Study of smart grid cyber-security, examining architectures, communication networks, cyber-attacks, countermeasure techniques, and challenges. Smart Grid (SG) technology utilizes advanced network communication and monitoring technologies to manage and regulate electricity generation and transport. However, this increased reliance on technology ...
Network security threats are patented to cause monetary loss. The data gathered in a network are used to identify the security threats like vulnerabilities and intrusions. Such data are called the data related to network security. Research Scholars can reach us in developing network security thesis topics based on data collection and detection ...
Network Security Research Topic ideas for MS, or Ph.D. Degree. I am sharing with you some of the research topics regarding Network Security that you can choose for your research proposal for the thesis work of MS, or Ph.D. Degree. CompTIA security+ guide to network security fundamentals. A survey of moving target defenses for network security.
Direct impact vs audience impact. As a security professional, it's tempting to rate a research project's impact based on the direct impact. For example, over the years I've seen a range of serious flaws in a certain popular CDN, and I suspect that if I directly targeted it, I could find multiple ways to take over all their customers ...
Network Security Monitoring (NSM) is a popular term to refer to the detection of security incidents by monitoring the network events. An NSM system is central for the security of current networks, given the escalation in sophistication of cyberwarfare. In this paper, we review the state-of-the-art in NSM, and derive a new taxonomy of the functionalities and modules in an NSM system. This ...
The Security Group in the EECS Department at the University of California, Berkeley studies a wide variety of topics, including cryptography, network security, usable security, and secure machine learning. To learn more about our research, we encourage you to visit the pages of our faculty and students, linked below.
The term 'Network security' provides the security for the computer services such as software and hardware and the communication devices like network infrastructure, and basic communication protocols of the network. It desires to attain data security on the network in an organization or in between the user individuals. If you are looking to implement interesting network security projects ...
The field of computer networking is experiencing rapid growth, accompanied by the swift advancement of internet tools. As a result, people are becoming more aware of the importance of network security. One of the primary concerns in ensuring security is the authority over domains, and network owners are striving to establish a common language to exchange security information and respond ...
In today's increasingly severe network security situation, network security situational awareness provides a more comprehensive and feasible new idea for the inadequacy of various single solutions and is currently a research hotspot in the field of network security. At present, there are still gaps or room for improvement in network security situational awareness in terms of model scheme ...
Network security research topics which are currently undergoing are cyber-insurance, cumulative Metric for an information network etc. Most commonly also used security mechanisms are Encipherment, Digital signature, also coding-decoding etc. But these are also fundamentals of Network security. It is also fast growing field which needs current ...
The overarching goal of our research program has been focusing on studying and building efficient and secure networks and systems to enable fast, reliable, private, and secure delivery and processing of information. Recent years have seen a proliferation of heterogeneous mobile and wireless devices (such as smartphones and Internet-of-Things ...
Computer Security Resource Center. Projects; Publications Expand or Collapse Topics ... Topics Select a term to learn more about it, and to see CSRC Projects, Publications, News, Events and Presentations on that topic. ... Federal Cybersecurity Research and Development Strategic Plan;
Please suggest me Ph.D. topic on cybersecurity particularly considering either app security, context-aware systems, and small devices including but not limited to embedded control systems, IoT ...
The research work presented in this thesis focuses on two highly important topics in the modern age. The first topic of research is the development of various image-based Network Intrusion Detection Systems (NIDSs) and performing a comprehensive analysis of their performance. Wi-Fi networks have become ubiquitous in enterprise and home networks which creates opportunities for attackers to ...
A definition of network security is the process of taking concurrent actions for network environment protection from illegal access by attackers.We can see various activities of attackers in the network such as misuse, data loss, modification, improper disclosure, and thereby legitimate user's privacy is leaked.. Our service i.e. network security research topics are your secure environment ...
Network Security PhD Research Topics Network Security PhD Research Topics offer innovative platform for you to get our dedicated professional's inventive ideas to improve your knowledge.We have 100+ international-level celebrated scientists to provide the best guidance for you in each step of your research.We offer highly confidential ...
Network security is the process that permits the users to regulate the network and manage the operating system and applications in the network. This page deals with the significant research aspects of network security. Let us start with the types of network security. List of Network Security Research Areas. Cryptographic Hashing; Source ...